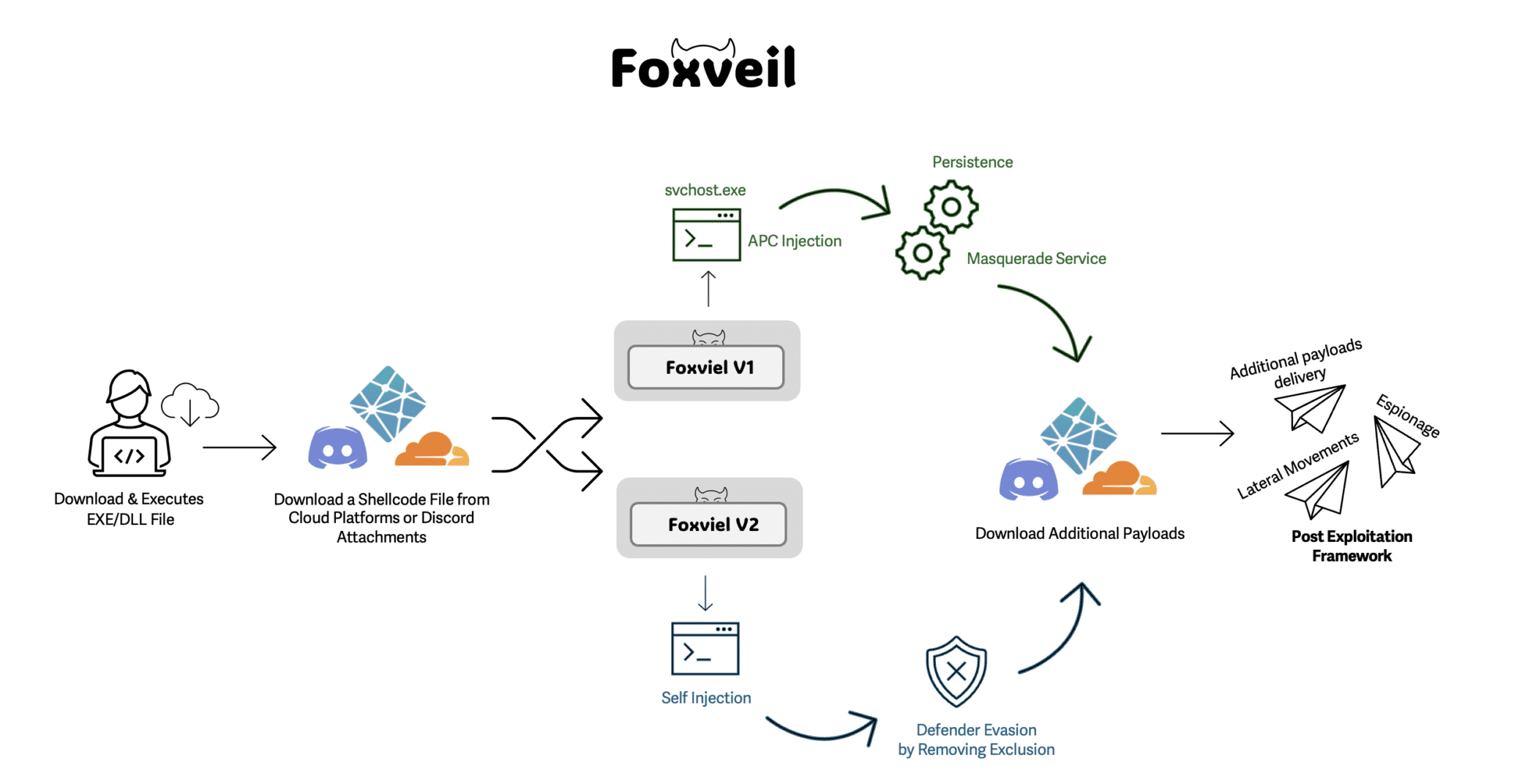
Foxveil is a newly identified initial-stage loader active since August 2025 that retrieves Donut-generated shellcode from trusted hosting platforms (Cloudflare Pages, Netlify) and occasionally Discord attachments, operating in two variants with different injection and persistence techniques. It uses in-memory injection (Early Bird APC in v1, self-injection in v2), service/SysWOW64-based persistence, and a runtime string-mutation routine to frustrate analysis; Cato’s SASE platform blocks the loader before staged payloads execute. #Foxveil #Cloudflare
Keypoints
- Foxveil is an initial-stage loader observed since August 2025 with two variants (v1 and v2) that retrieve next-stage payloads from Cloudflare Pages, Netlify, and sometimes Discord attachments.
- Foxveil v1 uses Early Bird APC injection into a newly spawned process masquerading as svchost.exe; v2 performs self-injection within the same process and commonly downloads shellcode from Discord attachments.
- Persistence differs by variant: v1 registers as a Windows service (AarSvc) and drops payloads to C:WindowsSysWOW64, while v2 drops payloads to SysWOW64 and includes a WMI call related to Defender exclusions.
- The loader employs a runtime string-mutation routine that rewrites high-signal analysis keywords (e.g., “fox”, “shellcode”, “beacon”) to impede static detection and reverse engineering.
- Next-stage payloads are written to SysWOW64 under legitimate-looking filenames (sms.exe, sihost.exe, taskhostw.exe) and Cato’s SASE Platform blocks the staged downloads before execution.
- Indicators point to later-stage post-exploitation frameworks (Cobalt Strike suspected) based on localhost listening behavior on ports such as 9933/9934 and memory-observed beacon-related strings.
MITRE Techniques
- [T1055 ] Process Injection – Foxveil executes downloaded shellcode in memory via injection: v1 uses an Early Bird APC injection into a newly spawned svchost.exe-masquerading process, while v2 performs self-injection. (‘Foxveil v1 spawns a new process that mimics svchost.exe, then injects the shellcode using an APC injection, consistent with an Early Bird-style workflow.’)
- [T1543.003 ] Create or Modify System Process: Windows Service – Foxveil v1 establishes persistence by registering itself as a Windows service (AarSvc) to blend into service lists. (‘Foxveil v1 establishes persistence by registering itself as a Windows service (Figure 6)’)
- [T1105 ] Ingress Tool Transfer – The loader retrieves next-stage payloads and Donut-generated shellcode from threat actor-controlled staging on Cloudflare Pages, Netlify, and Discord attachments. (‘Foxveil contacts threat actor-controlled infrastructure hosted on Cloudflare Pages and/or Netlify, or retrieves payloads via Discord attachments.’)
- [T1047 ] Windows Management Instrumentation – Foxveil v2 invokes a WMI call to MSFT_MpPreference related to Defender exclusion paths, indicating attempts to modify Defender configuration. (‘wmic /Namespace:rootMicrosoftWindowsDefender Path MSFT_MpPreference Call Remove ExclusionPath=”C:WindowsSysWOW64″‘)
- [T1027 ] Obfuscated Files or Information – Foxveil implements a runtime string-mutation routine that replaces high-signal strings with random values to frustrate static detection and reverse engineering. (‘When detected, the code replaces those strings with randomly generated values.’)
- [T1036 ] Masquerading – Foxveil uses filenames and placements that mimic legitimate Windows processes (e.g., sms.exe, sihost.exe) and writes payloads to C:WindowsSysWOW64 to reduce suspicion. (‘These filenames mimic legitimate Windows processes to reduce suspicion and survive casual inspection.’)
- [T1620 ] Reflective Code Loading – Use of Donut-generated shellcode and in-memory execution patterns indicates reflective or direct in-memory loading of payloads rather than disk-first execution. (‘The shellcode is executed via injection (variant-dependent)’ and ‘Donut is a widely used shellcode generator’)
- [T1562 ] Impair Defenses – Observed attempts to alter Microsoft Defender configuration via WMI suggest efforts to impair or manipulate defensive controls. (‘This behavior indicates an attempt to manipulate Microsoft Defender configuration’)
Indicators of Compromise
- [SHA-256 ] Malicious sample hashes observed – 62dd94ece73f510d03c74a00bfe9d8ad09d49c140fc30415a843c97cf018107f, 26d4e07514498453aa5d409a28489008080d307899bda8357870f193bdb994b8, and 32 more hashes
- [Domains ] Staging and payload hosting domains (Cloudflare Pages / Netlify) – syscore[.]pages[.]dev, csrss[.]netlify[.]app, and multiple other Pages/Netlify domains observed
- [File names ] Masqueraded next-stage filenames written to disk – sms.exe, sihost.exe (also observed: taskhostw.exe, taskhostw1.exe, audiodg.exe)
- [File paths ] On-disk placement used for persistence and staging – C:WindowsSysWOW64 (next-stage payloads written here)
- [Temporary attachments/URLs ] Discord-hosted attachments used to deliver Donut shellcode (time-limited links) – Donut shellcode downloaded via Discord attachment (links observed but expired)
- [Network ports ] Local listening ports consistent with suspected beacon activity – localhost listening on ports 9933 and 9934 (used to infer possible Cobalt Strike behavior)
Read more: https://www.catonetworks.com/blog/cato-ctrl-foxveil-new-malware/