Organizations rapidly adopt Copilot Studio agents but misconfigurations—broad sharing, unauthenticated access, unsafe HTTP requests, author authentication, hard‑coded credentials, unmanaged MCP tools, missing orchestration instructions, dormant or orphaned agents, and email-capable actions—create new identity and data‑access paths that traditional controls don’t monitor. Microsoft Defender Security Research provides ten detection-focused scenarios with Advanced Hunting queries and a mitigation playbook emphasizing ownership, least privilege, enforced authentication, hardened orchestration, and secret management to help teams find and fix these risks early. #CopilotStudio #MicrosoftDefender
Keypoints
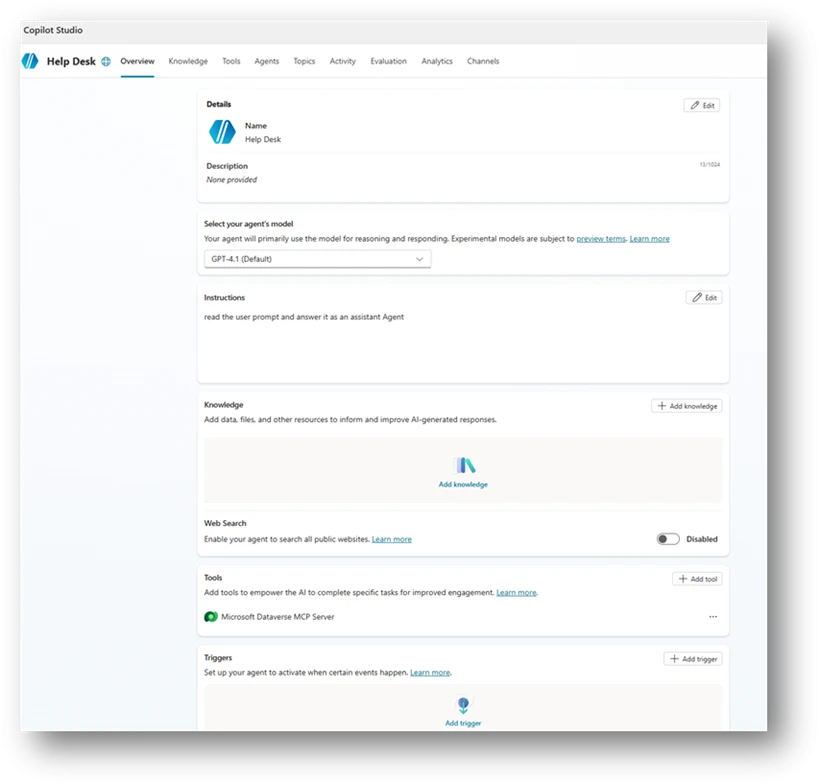
- Copilot Studio agents are rapidly integrated into business workflows, but small configuration choices frequently create exploitable security gaps.
- Researchers identified ten common misconfigurations — including broad sharing, no authentication, risky HTTP requests, email-capable actions, dormant/orphaned assets, author authentication, hard‑coded credentials, MCP tool misuse, and missing generative instructions.
- Microsoft Defender provides Community Advanced Hunting Queries (AI Agent folder) mapped to each risk to detect exposed or risky agent configurations.
- Primary impacts include unauthorized access, data exfiltration, privilege escalation, governance bypass, and hidden attack surfaces from dormant or undocumented components.
- Recommended mitigations: validate intent and ownership, restrict sharing, enforce authentication and least privilege, harden orchestration, prefer connectors over raw HTTP, and move secrets to Azure Key Vault.
- Operational guidance emphasizes periodic reviews, lifecycle governance, and treating agents as production assets rather than experiments.
- The research and detections are provided by Microsoft Defender Security Research with contributors Dor Edry and Uri Oren.
MITRE Techniques
- [None ] No MITRE ATT&CK techniques explicitly mentioned – ‘The article does not reference specific MITRE ATT&CK techniques.’
Indicators of Compromise
- [None ] No Indicators of Compromise are provided in the article – ‘The article contains no IPs, domains, hashes, filenames, or similar IOCs.’