OysterLoader (aka Broomstick / CleanUp) is a multi-stage C++ loader distributed via fake signed MSI installers that delivers payloads (notably Rhysida ransomware and commodity stealer Vidar) using staged shellcode, custom LZMA, and steganographically hidden DLLs. Its operators use extensive obfuscation (API-hammering, dynamic API hashing, custom Base64 alphabets and RC4), robust HTTP-based C2 with fallback servers, scheduled-task persistence, and anti-analysis checks. #OysterLoader #Rhysida
Keypoints
- OysterLoader is a four-stage C++ loader distributed via fake websites offering legitimate IT software, typically delivered as signed MSI installers to appear benign.
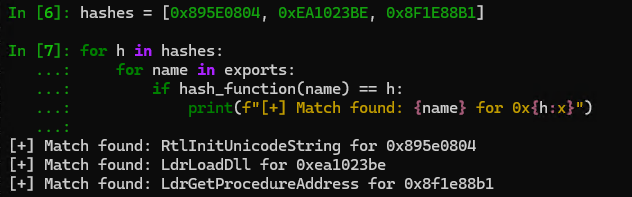
- Stage 1 (TextShell packer) performs heavy API call flooding, anti-debug checks, dynamic API resolution with custom hashing, and maps a shuffled payload into RWX memory.
- Stage 2 is custom shellcode that implements an in-house LZMA decompressor and relocation fixups to reconstruct and execute a position-independent payload in memory.
- Stage 3 performs environment checks (process counting, language checks), communicates with delivery servers (/reg, /login), retrieves a steganographically concealed PE, drops COPYING3.dll, and schedules execution via a task.
- Stage 4 (COPYING3.dll) is the core orchestrator: HTTP-based C2 over port 80/HTTPS with custom-shift Base64 alphabets, endpoint updates (/api/v2/facade, /api/v2/init), and a JSON fingerprint/beacon protocol for commands and payloads.
- IOC set includes hardcoded C2 IPs/domains, scheduled task names and DLL file names, a persistent mutex, RC4 key and custom header/alphabet strings; infrastructure has evolved through multiple endpoint revisions.
MITRE Techniques
- [T1204.002 ] User Execution: Malicious File – Delivery via fake signed MSI installers impersonating legitimate software to induce user installation (‘distributed mainly through fake websites that copy legitimate software. It is disguised as a software installer and serves as a MicroSoft Installer (MSI). the MSI is often signed to appear benign.’)
- [T1036 ] Masquerading – Use of fake sites and legitimate-looking installers to impersonate trusted applications (‘fake websites that copy legitimate software… disguised as a software installer’).
- [T1027.006 ] Steganography – Hiding the next-stage PE inside an icon image returned by C2 and extracting/decrypting it (‘the C2 responds with an image … the malware uses steganography to hide the next stage payload as an icon’).
- [T1027 ] Obfuscated Files or Information – Custom LZMA implementation, non-standard headers/bitstream, API hashing and heavy code obfuscation to evade analysis (‘custom LZMA decompression routine with a non-standard header and modified bitstream’; ‘dynamically imported APIs… each sample uses a slightly different hashing algorithm’).
- [T1105 ] Ingress Tool Transfer – Downloading and writing a retrieved PE to disk (COPYING3.dll) and executing it (‘Once decrypted the PE is written into a file name COPYING3.dll in the %APPDATA% directory’).
- [T1055 ] Process Injection – Allocating RWX memory and copying/executing shellcode and staged payloads in-memory (‘it allocates a memory area with necessary permissions (Read, Write, Execute) and makes a raw copy of the data in the newly allocated memory’).
- [T1140 ] Deobfuscate/Decode Files or Information – RC4 decryption of stego payloads and custom Base64 decoding for C2 messages (‘it decrypts the data using RC4 algorithm along with a hardcoded key’; ‘JSON completely encoded with a custom algorithm based on Base64 encoding’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – Use of HTTP/HTTPS for C2 communication, registration (/reg), login (/login) and beaconing endpoints (‘communicates over HTTPS, the first message acts as a registration as indicated by the C2 URL (/reg)’; ‘All traffic uses WinINet APIs … exchanges data in JSON format’).
- [T1053.005 ] Scheduled Task/Job – Persistence via a scheduled task that runs rundll32 to call the dropped DLL every 13 minutes (‘the DLL is executed by the task scheduler… task name COPYING runs every 13 minutes … rundll32.exe … COPYING3.dll DllRegisterServer’).
- [T1218.011 ] Signed Binary Proxy Execution: Rundll32 – Using rundll32.exe to execute the dropped DLL (‘rundll32.exe C:…COPYING3.dll DllRegisterServer’).
- [T1497.001 ] Virtualization/Sandbox Evasion: Debugger Detection – Anti-debug check using IsDebuggerPresent leading to infinite loop to hinder analysis (‘IsDebuggerPresent() check; if a debugger is detected, the malware enters an infinite loop (while(1);)’) .
- [T1057 ] Process Discovery – Counting running processes and enforcing an execution threshold (exits if below 60 processes) (‘EnumProcess to count the number of running processes, if the count is below 60, the malware exits’).
- [T1082 ] System Information Discovery – Exfiltration of host fingerprint (username, computer name, running processes, OS version) in JSON to C2 (‘the first data that is sent to the C2 is a JSON … contains … a3 username … a4 computer name …’ and annexed fingerprint example).
Indicators of Compromise
- [IP address ] C2 servers – 85.239.53[.]66, 51.222.96[.]108, and 1 more IP (135.125.241[.]45)
- [Domain ] Active C2/facade endpoints – grandideapay[.]com, nucleusgate[.]com, and 4 more domains (cardlowestgroup[.]com, socialcloudguru[.]com, coretether[.]com, registrywave[.]com)
- [File name ] Dropped payloads and DLLs – COPYING3.dll, VisualUpdater (dropped to %APPDATA% and executed by scheduled task), and other campaign names like AlphaSecurity, DetectorSpywareSecurity
- [Scheduled task ] Persistence task names and commands – Task name COPYING (runs every 13 minutes) using rundll32.exe to call COPYING3.dll (‘/Create /SC MINUTE /MO 13 /TN “COPYING3” /TR “C:WindowsSystem32rundll32.exe … COPYIN G3.dll DllRegisterServer”‘)
- [HTTP path/URL ] C2 endpoints and delivery paths – /reg, /login, /api/kcehc, /api/jgfnsfnuefcnegfnehjbfncejfh, /api/v2/facade (used for registration, payload delivery and beaconing)
- [Mutex ] Single-instance mutex – h6p#dx!&fse?%AS! (used by stage 3 to prevent multiple instances)
- [Hardcoded key/alphabet ] Encryption/encoding artifacts – hardcoded RC4 key used to decrypt icon payloads (long key beginning ‘vpjNm4FDCr82AtUfhe39EG5JLwuZszKP…’), and non-default Base64 alphabet string used for C2 encoding
Read more: https://blog.sekoia.io/oysterloader-unmasked-the-multi-stage-evasion-loader/