Netskope Threat Labs is tracking phishing campaigns that weaponize fake video conference invites for Zoom, Microsoft Teams, and Google Meet, tricking users into downloading a “mandatory” software update from typo-squatted domains. Those updates are digitally signed remote monitoring and management (RMM) tools — including Datto RMM, LogMeIn, and ScreenConnect — that give attackers administrative access and a platform to exfiltrate data or deploy additional malware. #DattoRMM #ScreenConnect
Keypoints
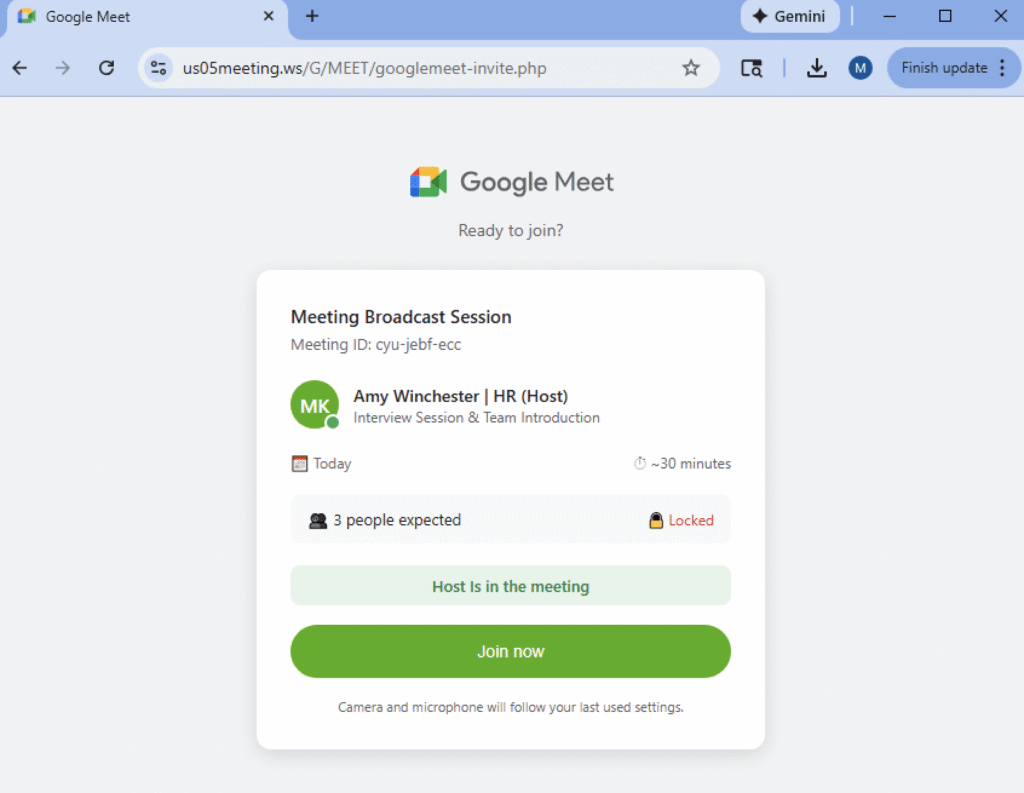
- Attackers send convincing fake meeting invites and host pixel-perfect phishing pages mimicking Zoom, Microsoft Teams, and Google Meet.
- Victims are prompted to install a purported “mandatory” software update to join the call, increasing likelihood of user execution.
- Payloads are digitally signed RMM agents (Datto RMM, LogMeIn, ScreenConnect) renamed to match expected platform installers.
- Using legitimate, signed RMM tools allows attackers to bypass signature-based controls and blend with normal enterprise traffic.
- Once installed, RMM features (file transfer, remote shell, screen sharing) enable data collection, lateral movement, and persistence.
- Attackers can leverage RMM infrastructure to push further malware at scale, turning a single compromised endpoint into a widespread breach.
MITRE Techniques
- [T1566 ] Phishing – Attackers send fake video conference invites as the primary lure to coerce victims into actions. (‘weaponize fake meeting invites for various video conference applications’)
- [T1204.002 ] User Execution: Malicious File – Victims are tricked into downloading and running a provided “update” that installs the payload. (‘download and execute a provided “update” before being allowed to join.’)
- [T1036.005 ] Masquerading: Match Legitimate Name – Malicious installers are renamed to mimic legitimate installers to reduce suspicion. (‘renamed to match the expected platform, using names like GoogleMeeet.exe or ZoomWorkspaceinstallersetup.msi’)
- [T1105 ] Ingress Tool Transfer – Attackers deliver legitimate RMM binaries to victims and can use those tools to deploy additional malware across the environment. (‘use the RMM’s own infrastructure to push more potent malware across the entire environment’)
- [T1021 ] Remote Services – Deployed RMM agents provide remote administrative access for command execution, file transfer, and screen viewing. (‘enable attackers to remotely access victims’ machines and gain full administrative control’)
Indicators of Compromise
- [Domain ] Phishing redirect – zoom-meet.us (typo-squatted Zoom domain used in the campaign)
- [File name ] Renamed installer binaries used as bait – GoogleMeeet.exe, ZoomWorkspaceinstallersetup.msi
- [Signed RMM agents ] Payloads deployed to gain administrative access – Datto RMM, LogMeIn Unattended, ScreenConnect
Read more: https://www.netskope.com/blog/attackers-weaponize-signed-rmm-tools-via-zoom-meet-teams-lures