Cephalus is a Go-developed ransomware family observed from June 2025 that gains initial access mainly through exposed RDP without MFA, often using stolen credentials, and follows a double-extortion model by exfiltrating sensitive data prior to encryption. AttackIQ published an emulation of Cephalus TTPs to help organizations validate controls and test detection/prevention across behaviors like process injection, Defender tampering, shadow copy deletion, scheduled task persistence, and AES/RSA hybrid encryption. #Cephalus #AttackIQ
Keypoints
- Cephalus is a Go-based ransomware strain with activity dating to June 2025 and public reporting in August 2025.
- Primary initial access is achieved via exposed RDP services lacking MFA, frequently using stolen credentials.
- The group practices double-extortion by exfiltrating sensitive data before encrypting files to intensify ransom pressure.
- Cephalus uses hybrid encryption (AES-256 CTR for files and RSA-1024 for key protection) and employs evasion/anti-analysis techniques such as fake AES key generation, secure memory handling, process injection, and DLL sideloading.
- It disables and modifies Windows Defender protections, adds exclusions, terminates backup/database services, and deletes Volume Shadow Copies to hinder recovery.
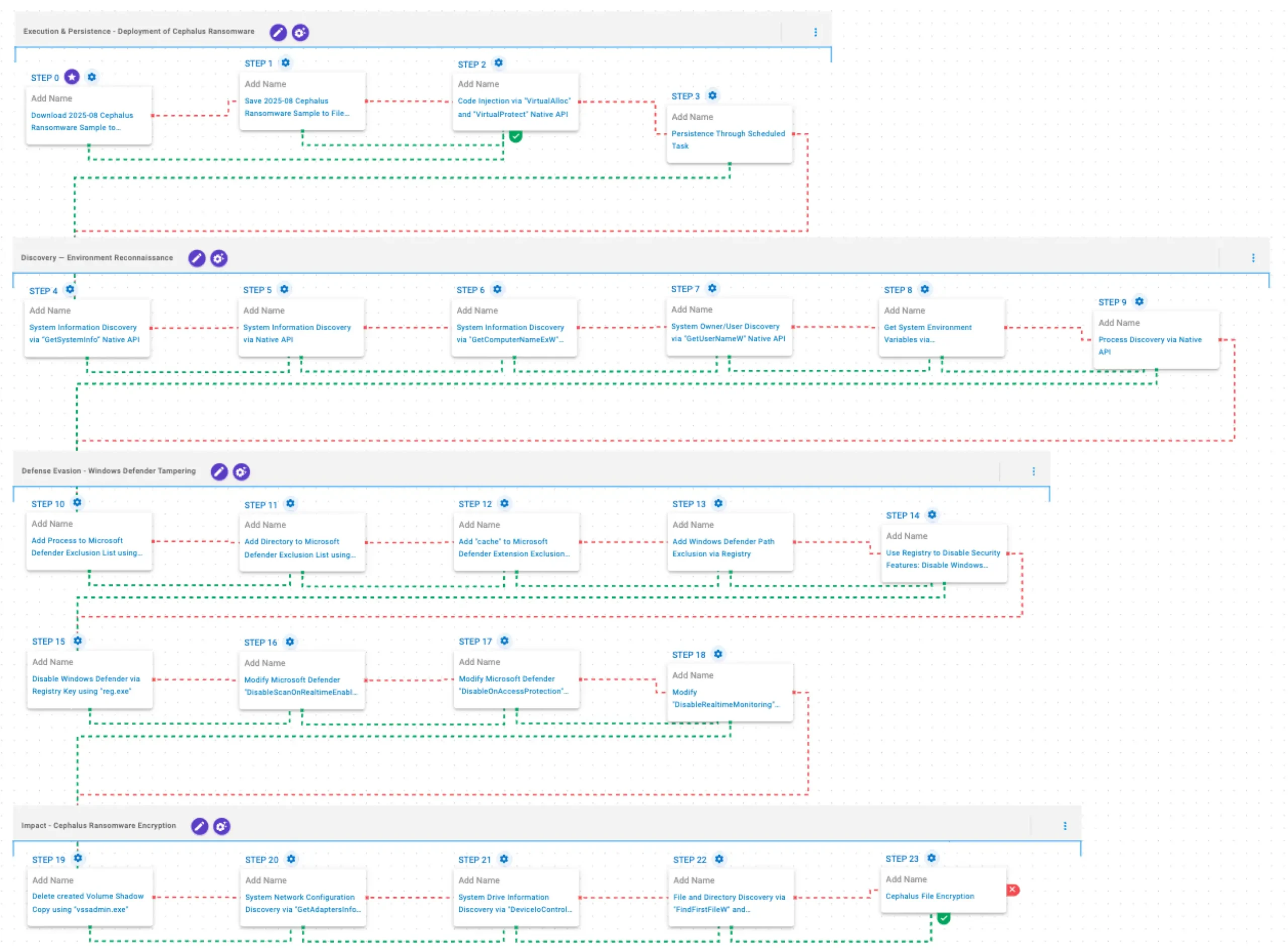
- AttackIQ released an emulation (AEV platform) that replicates Cephalus TTPs—covering delivery, discovery, defense evasion, persistence, and encryption—to validate security control effectiveness and response workflows.
MITRE Techniques
- [T1105 ] Ingress Tool Transfer – Sample delivery and disk staging used to test controls (‘The Cephalus Ransomware Sample (SHA256: a34acd47127196ab867d572c2c6cf2fcccffa3a7a87e82d338a8efed898ca722) is saved to disk in two separate scenarios to test network and endpoint controls and their ability to prevent the delivery of known malicious samples.’)
- [T1055 ] Process Injection – Cephalus injects code into legitimate processes using VirtualAlloc and VirtualProtect to execute payloads (‘This scenario performs process injection by allocating memory in a running process with VirtualAlloc, writing shellcode to that memory space, and then changing the memory protection option with VirtualProtect.’)
- [T1053.005 ] Scheduled Task – Persistence is achieved by creating scheduled tasks via schtasks to ensure execution after reboots (‘This scenario creates a new scheduled task for persistence using the schtasks utility.’)
- [T1082 ] System Information Discovery – Multiple native APIs are called to collect system and environment information for fingerprinting and behavior adjustment (‘This scenario executes the GetSystemInfo Windows native API call to retrieve system information.’ / ‘This scenario executes RtlGetVersion, and NetWkstaGetInfo Windows native API calls to enumerate system information.’ / ‘This scenario executes the GetComputerNameExW Windows native API call to retrieve a NetBIOS or DNS name associated with the local computer.’ / ‘This scenario executes the GetEnvironmentStrings Windows native API call to discover environmental variables…’)
- [T1033 ] Account Discovery (System Owner/User Discovery) – Retrieves the local account name via GetUserNameW to identify the current user context (‘This scenario executes the GetUserNameW Windows native API call to retrieve the account name associated with the local computer.’)
- [T1057 ] Process Discovery – Enumerates running processes using CreateToolhelp32Snapshot and Process32FirstW/Process32NextW (‘This scenario executes the CreateToolhelp32Snapshot Windows native API call to receive a list of running processes and iterates through each process object with Process32FirstW and Process32NextW.’)
- [T1562.001 ] Disable or Modify Security Tools – Cephalus adds Defender exclusions and modifies Defender settings via PowerShell and registry edits to weaken protections (‘This scenario adds a process to the Microsoft Defender exclusion list using the Add-MpPreference Powershell cmdlet.’ / ‘This scenario adds the C:WindowsSystem32svchost.exe path to Windows Defender path exclusions via a registry key modification.’)
- [T1112 ] Modify Registry – Uses registry modifications to disable Windows Defender real-time monitoring and scanning (‘This scenario disables the real-time monitoring functionality of Windows Defender by modifying specific registry values.’ / ‘This scenario modifies the registry value DisableAntiSpyware under HKLMSOFTWAREPoliciesMicrosoftWindows Defender to disable Windows Defender.’)
- [T1490 ] Inhibit System Recovery – Deletes Volume Shadow Copies using vssadmin to prevent restore-based recovery (‘This scenario executes the vssadmin.exe utility to delete a recent Volume Shadow Copy created by the assessment template.’)
- [T1016 ] System Network Configuration Discovery – Retrieves adapter/network configuration via GetAdaptersInfo for network profiling (‘This scenario executes GetAdaptersInfo Windows native API call to retrieve adapter information from the local computer.’)
- [T1083 ] File and Directory Discovery – Traverses file system using FindFirstFileW and FindNextFileW to enumerate targets for encryption (‘This scenario executes the FindFirstFileW and FindNextFileW Windows native API calls to enumerate the file system.’)
- [T1486 ] Data Encrypted for Impact – Performs file encryption in place using AES-256 CTR and protects keys with RSA-1024 to render data inaccessible (‘This scenario performs the file encryption routines used by common ransomware families… Files matching an extension list are identified and encrypted in place using similar encryption algorithms as used by Cephalus ransomware.’)
- [T1574.002 ] DLL Side-Loading – Uses legitimate trusted executables to load malicious DLLs as an additional evasion/persistence method (recommended emulation scenario: ‘This scenario leverages a legitimate and trusted executable to load a malicious Dynamic-link Library (DLL).’)
Indicators of Compromise
- [File Hash ] Cephalus sample – a34acd47127196ab867d572c2c6cf2fcccffa3a7a87e82d338a8efed898ca722
- [File Path ] Defender exclusion and system binary paths observed – %TEMP%aiq-temp-exclusion, C:WindowsSystem32svchost.exe
- [Filenames/Utilities ] Tools and utilities used in attack and remediation interference – vssadmin.exe (shadow copy deletion), schtasks.exe (persistence creation)
- [Registry Keys/Values ] Defender-related registry modifications used to disable protections – HKLMSOFTWAREPoliciesMicrosoftWindows DefenderReal-Time ProtectionDisableScanOnRealtimeEnable, HKLMSOFTWAREPoliciesMicrosoftWindows DefenderDisableAntiSpyware
- [File Extension ] Added to Defender exclusion list to evade detection – .cache
Read more: https://www.attackiq.com/2026/02/05/emulating-cephalus-ransomware/