BQTLock uses stealthy process injection and UAC bypass to escalate privileges and move into credential theft and screen capture before obvious ransomware activity, increasing breach risk. GREENBLOOD is a Go-based, ChaCha8-encrypting ransomware that locks files rapidly, attempts self-deletion to hinder forensics, and pressures victims via a TOR leak site. #BQTLock #GREENBLOOD
Keypoints
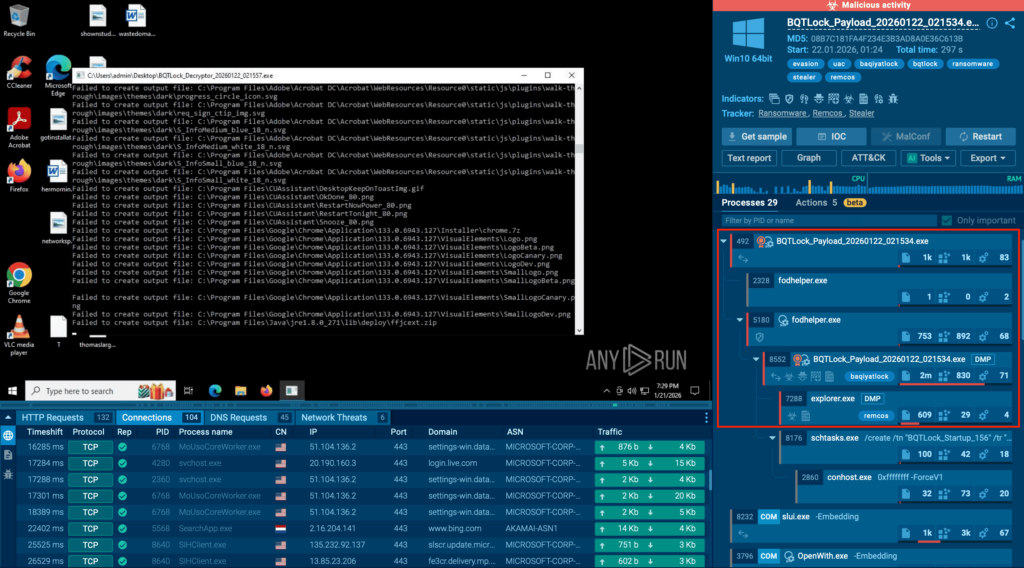
- BQTLock hides inside legitimate processes by injecting Remcos into explorer.exe, performs UAC bypass via fodhelper.exe, and establishes autorun persistence to retain elevated access after reboot.
- BQTLock escalates from stealth to active data theft and screen capture, turning infections into combined ransomware + data breach incidents.
- GREENBLOOD is Go-based and uses fast ChaCha8 encryption to disrupt operations in minutes, then attempts self-deletion and uses a TOR leak site to increase extortion pressure.
- Both families compress the SOC response window—BQTLock via stealth/setup and GREENBLOOD via rapid encryption and cleanup—raising containment costs and business impact.
- ANY.RUN’s interactive sandbox enables behavior-first triage to confirm process injection, UAC bypass, persistence, encryption, and self-delete during execution and to extract IOCs immediately.
- Integrating sandbox-derived indicators into threat intelligence and TI feeds helps teams find related variants, harden detections, and move from reactive to proactive defense.
MITRE Techniques
- [T1055 ] Process Injection – Injects Remcos into explorer.exe to remain hidden inside legitimate system activity. (‘injects the Remcos payload into explorer.exe to remain hidden inside legitimate system activity’)
- [T1548.002 ] Bypass User Account Control – Performs a UAC bypass via fodhelper.exe to obtain elevated privileges. (‘performs a UAC bypass via fodhelper.exe to obtain elevated privileges’)
- [T1547.001 ] Registry Run Keys / Startup Folder (Boot or Logon Autostart Execution) – Sets autorun persistence to keep elevated access after reboot. (‘sets autorun persistence to keep elevated access after reboot’)
- [T1003 ] OS Credential Dumping – Moves into credential theft after escalation, exposing sensitive account material. (‘Credentials stealing by BQTLock discovered by ANY.RUN’)
- [T1056 ] Input Capture – Performs screen capture activity that may expose sensitive corporate information. (‘screen capture activity that may expose sensitive corporate information’)
- [T1486 ] Data Encrypted for Impact – Uses ChaCha8-based encryption to rapidly lock files and disrupt operations within minutes. (‘Fast ChaCha8-based encryption capable of disrupting operations within minutes’)
- [T1070 ] Indicator Removal on Host – Attempts self-deletion/cleanup to limit forensic visibility and hamper post-incident investigation. (‘Attempts to delete the executable, limiting post-incident forensic visibility’)
Indicators of Compromise
- [Malware Family ] observed threats – BQTLock, GREENBLOOD
- [Process Name ] attack hosts/processes involved – explorer.exe (Remcos injected), fodhelper.exe (UAC bypass)
- [Command Line / Query ] detection pivot – commandLine:”greenblood” (used in ANY.RUN TI Lookup to find related executions)
- [Leak site / TOR domain ] extortion channel – TOR-based leak site referenced (no specific domain provided)
- [Encryption Algorithm ] impact indicator – ChaCha8-based encryption (GREENBLOOD rapid file locking)
- [Executable / File ] cleanup/self-delete context – GREENBLOOD executable deletion attempts (no filename provided)
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/emerging-ransomware-bqtlock-greenblood/