This article analyzes how attackers misuse QR codes to deliver phishing (quishing), in‑app deep links for account takeovers, and direct APK downloads to bypass app store protections. It highlights telemetry showing over 11,000 daily detections of malicious QR codes and documents campaigns abusing QR shorteners and messaging‑app deep links targeting Telegram and Signal. #Telegram #Signal
Keypoints
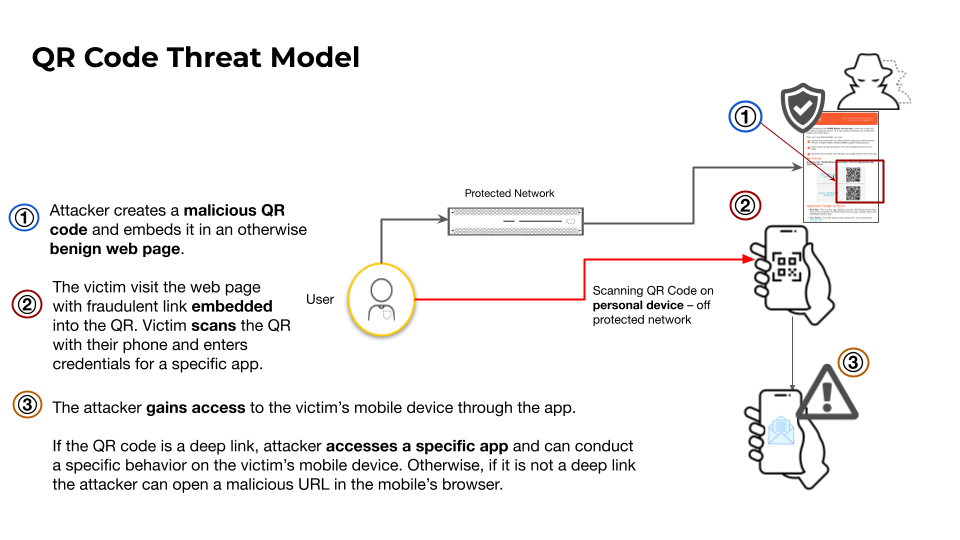
- QR codes are increasingly abused to hide malicious destinations via URL shorteners, in‑app deep links, and direct APK downloads, enabling evasion of web and mobile security controls.
- Telemetry shows an average of over 11,000 daily detections of malicious QR code use and 75,000 QR code detections per day across crawled pages, with ~15% linking to malicious content.
- QR code shorteners (e.g., qrco[.]de, me-qr[.]com, qrs[.]ly) convert static images into dynamic endpoints, allowing attackers to change destinations and leverage service reputations to evade detection.
- In‑app deep links (custom URL schemes and standard web URLs redirected into apps) enable account takeover, contact/calendar poisoning, automatic payments, and rogue Wi‑Fi connections—often invisible to standard web crawlers.
- Attack campaigns include mass phishing and targeted messenger‑app takeover efforts (notably Telegram and Signal), with confirmed campaigns targeting Ukrainian Signal users linked to state‑aligned actors.
- Attackers distribute malicious Android APKs via QR codes to bypass app store vetting; telemetry found 1,457 distinct APKs and tens of thousands of host pages distributing APKs requesting excessive permissions.
MITRE Techniques
- [T1566 ] Phishing – QR codes are used to deliver phishing pages and scams (quishing), tricking users into scanning and following malicious links (‘phishing (known as quishing)’).
- [T1204 ] User Execution – QR codes rely on user interaction to trigger malicious outcomes (scanning and following deep links or downloads), exploiting low user vigilance (‘some people instinctively scan them without hesitation’).
Indicators of Compromise
- [Domain/URL ] examples of malicious landing pages, shorteners and phishing hosts – hxxps[:]//qrco[.]de/bgP6vx, hxxps[:]//cdnimg.jeayacrai[.]in[.]net/qY42h5ei3SBo9ZmvO!/, and multiple snitch/open-group variants (and many other domains listed).
- [IP Address ] examples of infrastructure used in scams – 20.217.81[.]20 (host for financial scam URL) and other hosting IPs observed in telemetry.
- [Deep link / URI ] in‑app deep links and payment URIs used for account takeover and payments – tg[:]//login?token=…, upi://pay?pa=Q573631163@ybl, metamask[:]//connect?… , bitcoin:12wXzmwak8LJ88e1ejupY3brfQi43xdDhb.
- [APK filename ] malicious or suspicious Android package files distributed via QR codes – yicai.apk, NagaPocker.apk, app-u7cp-release.apk (and other APKs such as ludashi_home.apk, k12sns.apk).
- [Domains targeting messenger takeovers ] examples of domains used in Telegram/Signal/WhatsApp campaigns – fable.tele-tale[.]cn, Olb228hoki[.]live, signal.skyriver[.]ch, snitch.open-group[.]site (and multiple gui.snitch-dev variants).
Read more: https://unit42.paloaltonetworks.com/qr-codes-as-attack-vector/