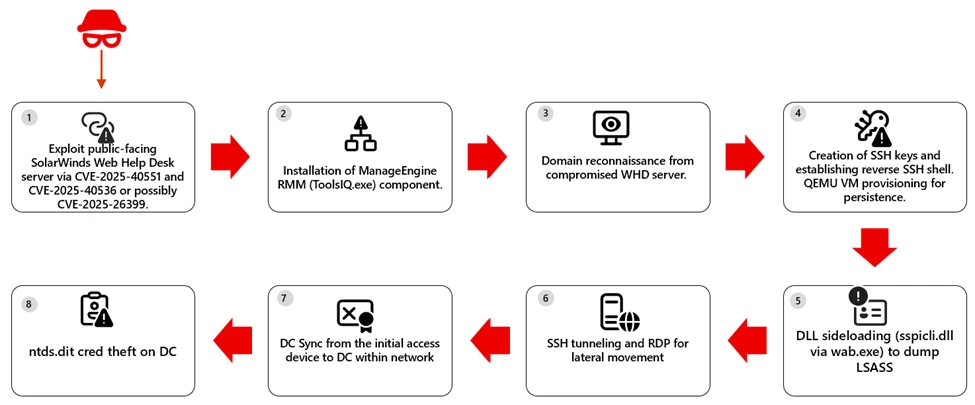
The Microsoft Defender Research Team observed a multi-stage intrusion where internet‑exposed SolarWinds Web Help Desk (WHD) instances were exploited for unauthenticated remote code execution, enabling payload download, installation of ManageEngine RMM components, credential theft, and lateral movement to high‑value assets. The report provides detection, hunting, and hardening guidance—emphasizing patching, removing public access to admin paths, and behavior‑based detection across identity, endpoint, and network layers. #SolarWindsWHD #ManageEngine
Keypoints
- Attackers exploited internet‑facing SolarWinds Web Help Desk (WHD) instances to achieve unauthenticated remote code execution and an initial foothold.
- Post‑exploitation activity included spawning PowerShell to use BITS for payload download, installation of ManageEngine RMM components, and enumeration of domain users and groups including Domain Admins.
- Persistence and lateral movement techniques observed included reverse SSH, SSH tunneling/port forwarding, RDP access, and creation of a scheduled task to launch a QEMU VM at startup.
- Credential theft methods included DLL sideloading via wab.exe to load a malicious sspicli.dll for LSASS access and at least one instance of DCSync against a domain controller.
- Microsoft Defender provided coverage across stages (MDVM for vulnerable WHD, Defender for Endpoint alerts for suspicious PowerShell, SSH tunneling, scheduled tasks, and Defender for Identity for suspected credential theft).
- Recommended mitigations: patch WHD CVEs (CVE-2025-40551, CVE-2025-40536, CVE-2025-26399), remove public admin access, increase logging, evict unauthorized RMM artifacts, rotate credentials, and isolate compromised hosts.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Exploited internet‑facing SolarWinds WHD to achieve unauthenticated remote code execution; [‘active, in-the-wild exploitation of exposed SolarWinds Web Help Desk (WHD)’]
- [T1059.001 ] PowerShell – Spawned PowerShell on compromised hosts to orchestrate payload download and execution via BITS; [‘compromised service of a WHD instance spawned PowerShell to leverage BITS for payload download and execution’]
- [T1105 ] Ingress Tool Transfer – Used BITS and other download mechanisms to transfer and execute payloads on compromised systems; [‘spawned PowerShell to leverage BITS for payload download and execution’]
- [T1053 ] Scheduled Task/Job – Created a scheduled task to launch QEMU at system startup under SYSTEM for hidden persistence and SSH exposure; [‘SCHTASKS /CREATE /V1 /RU SYSTEM /SC ONSTART /F /TN “TPMProfiler” /TR “C:Userstmpqemu-system-x86_64.exe … hostfwd=tcp::22022-:22″‘]
- [T1021.004 ] Remote Services: SSH – Established reverse SSH and SSH tunneling/port forwarding for lateral access and remote control; [‘reverse SSH and RDP access’ and ‘hostfwd=tcp::22022-:22’]
- [T1021.001 ] Remote Services: RDP – Used Remote Desktop sessions for interactive access and lateral movement; [‘established … RDP access’]
- [T1574.002 ] DLL Side-Loading – Abused wab.exe to load a malicious sspicli.dll to access LSASS memory and steal credentials; [‘used DLL sideloading by abusing wab.exe to load a malicious sspicli.dll’]
- [T1003.001 ] OS Credential Dumping: LSASS Memory – Accessed LSASS memory via sideloaded components to harvest credentials; [‘access to LSASS memory and credential theft’]
- [T1003.006 ] DCSync – Performed DCSync to request password data from a domain controller using high‑privilege credentials obtained post‑compromise; [‘activity escalated to DCSync from the original access host’]
Indicators of Compromise
- [CVE ] Vulnerabilities referenced as exploitation vectors – CVE-2025-40551, CVE-2025-40536, CVE-2025-26399
- [File names / binaries ] Artifacts installed or abused during intrusion – qemu-system-x86_64.exe, sspicli.dll, and ToolsIQ.exe
- [Scheduled task name ] Persistence artifact – “TPMProfiler” scheduled task configured to launch QEMU at startup
- [Detection name ] AV/telemetry detections referenced – Trojan:Win32/HijackWebHelpDesk.A (Microsoft Defender Antivirus)
- [Network / port ] Lateral access indicators – SSH tunneling with hostfwd tcp::22022-:22 (exposes SSH on forwarded port 22022)