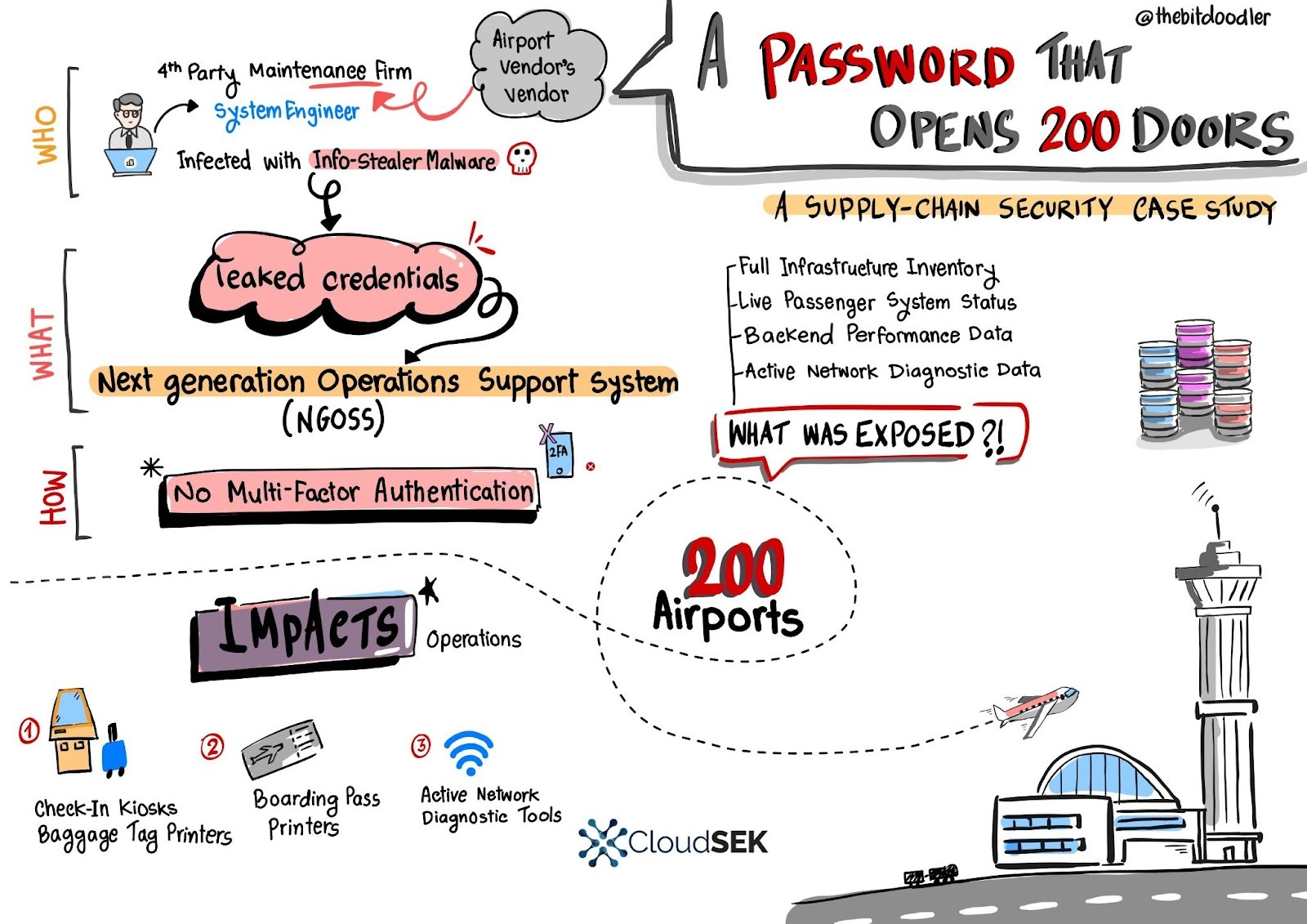
A single leaked username and password for a European fourth‑party engineer granted access to a central Next Generation Operations Support System (NGOSS) portal that managed operational dashboards for over 200 airports, exposing live infrastructure inventories, device statuses, and network diagnostic tools. SVigil detected the credential circulation and the vendor revoked access and enforced emergency MFA to avert potentially massive DoS and baggage-reconciliation outages. #SVigil #NGOSS
Keypoints
- A leaked simple username and password for a 4th‑party maintenance engineer were posted on underground forums, granting access to a primary vendor’s NGOSS portal used by ~200 airports.
- The NGOSS portal lacked Multi‑Factor Authentication, allowing single‑factor credentials to expose full operational control panels and inventory data.
- Exposed data included internal IP addresses, hostnames (e.g., BHS-SVR-02), live device status for kiosks/printers, and backend performance metrics for MSSQL/PostgreSQL servers.
- The portal provided active network diagnostic tools (Ping, Trace Route) usable from inside airport networks, enabling internal reconnaissance and DoS vectors.
- Realistic attack scenarios included targeted kiosk/terminal DoS, baggage reconciliation outages that could ground flights, and coordinated multi-hub attacks with potential losses from millions to over $1B.
- Immediate mitigations were credential revocation, emergency MFA rollout, and auditing of third‑party accounts; strategic recommendations included vendor zero trust and supply‑chain audits.
- The incident highlights supply‑chain risk: a single weak link or leaked credential can cascade into global aviation operational and financial damage.
MITRE Techniques
- [T1078 ] Valid Accounts – Leaked operational credentials were used to gain legitimate access to the vendor portal (‘These credentials … were the only keys needed to access the primary vendor’s main Next Generation Operations Support System (NGOSS) portal.’)
- [T1082 ] System Information Discovery – The portal exposed hostnames, device roles, and system metrics enabling discovery of infrastructure (‘Full Infrastructure Inventory: Every server, switch, and core manager, complete with internal IP addresses, hostnames, and device roles (e.g., BHS-SVR-02 for Baggage Handling).’)
- [T1016 ] System Network Configuration Discovery – Internal IP addressing and network device roles were visible, providing a real‑time map of airport network topology (‘a complete, real-time map of the entire operational ecosystem for hundreds of airports’ and ‘internal IP addresses’).
- [T1046 ] Network Service Scanning – Built‑in diagnostics allowed active network probes from inside the trusted network (‘The portal allowed the user to run live “Ping” and “Trace Route” commands from inside the trusted airport network’).
- [T1499 ] Endpoint Denial of Service – The described attack scenarios use repeated diagnostics and connectivity floods to render kiosks/stations unavailable (‘repeatedly trigger diagnostics / flood connectivity, rendering kiosks and associated CUSS/CUPPS stations unavailable for 6 hours’).
Indicators of Compromise
- [Credentials ] leaked access used to authenticate to vendor portal – “simple username and password” for a European fourth‑party engineer, and revocation of those credentials after detection
- [Hostnames / Device Names ] exposed inventory context – BHS-SVR-02 (baggage handling server), check-in kiosk and boarding-pass-printer hostnames
- [Internal IP Addresses ] network mapping context – internal IP addresses for servers and switches (examples not enumerated in article)
- [Portal / Service Names ] access targets – NGOSS (Next Generation Operations Support System) portal, Baggage Reconciliation System (BRS)
- [Backend Services ] performance context – MSSQL and PostgreSQL database performance metrics visible in dashboards
Read more: https://www.cloudsek.com/blog/the-hidden-backdoor-to-200-airports-a-supply-chain-failure-in-aviation