Socket researchers identified a developer-account compromise in the Open VSX Registry that published malicious updates to four oorzc extensions embedding the GlassWorm loader, using staged AES-encrypted loaders and Solana transaction memos as a dynamic dead drop. The macOS-focused follow-on payload steals browser cookies, wallet files, keychain, AWS and SSH credentials and establishes persistence via a LaunchAgent; remove affected extensions, check for persistence, and rotate exposed tokens and keys. #GlassWorm #OpenVSX
Keypoints
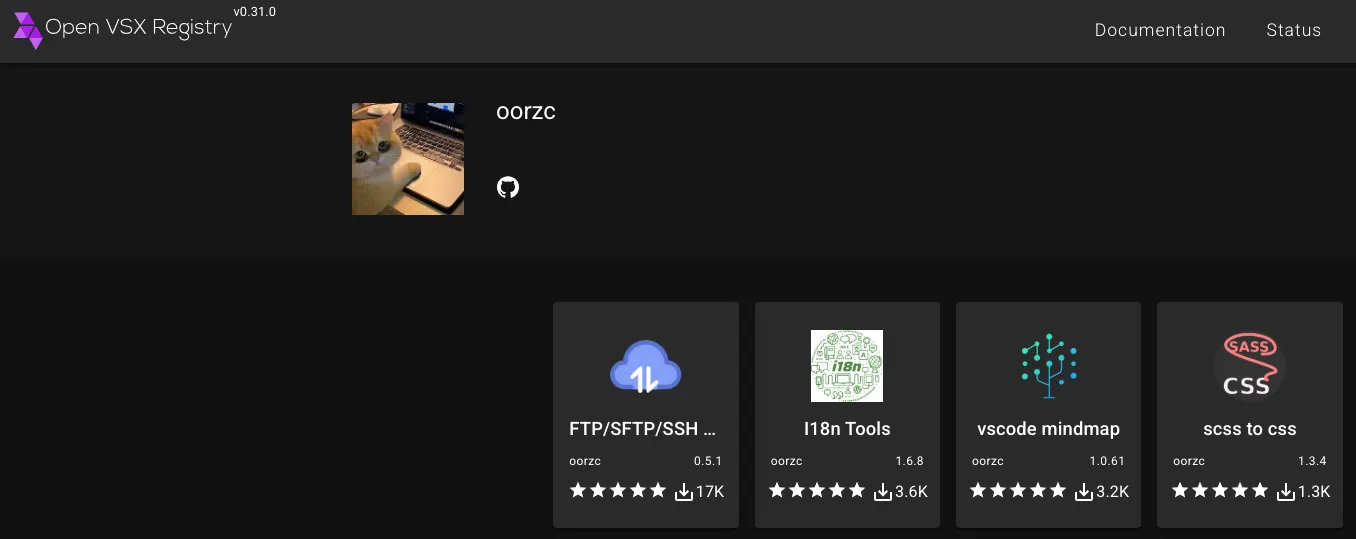
- On January 30, 2026, four Open VSX extensions published by the oorzc author ([email protected], [email protected], [email protected], [email protected]) were released with malicious versions embedding a GlassWorm loader.
- Those extensions had accumulated more than 22,000 combined Open VSX downloads prior to the malicious releases and were published under an established publisher identity, indicating a developer credential or token compromise rather than typosquatting.
- The malicious updates use staged AES-256-CBC encrypted loaders that decrypt and eval() runtime code, perform geofencing to avoid Russian locales, and resolve next-stage C2 configuration from Solana transaction memos (a blockchain dead drop).
- Downstream macOS payloads harvest browser cookies, history, wallet-extension data (e.g., MetaMask), desktop cryptocurrency wallet files (Electrum, Exodus, Ledger Live, Trezor Suite, Binance, TonKeeper), Apple keychain and Notes, FortiClient VPN configs, and developer secrets ( ~/.aws, ~/.ssh, npm _authToken, GitHub artifacts).
- Exfiltration is performed via HTTP POST to hardcoded IP-based endpoints (example path /p2p on 45[.]32[.]150[.]251) and persistence is established via a LaunchAgent (e.g., com.user.nodestart.plist) that runs a Node runtime at login.
- Open VSX maintainers deactivated the publisher’s tokens, removed malicious releases (and all versions of oorzc.ssh-tools), and Socket recommends removing affected extensions, checking for persistence and staging artifacts, and immediately rotating/revoking exposed tokens and keys.
MITRE Techniques
- [T1195 ] Supply Chain Compromise – Threat actor used compromised publishing credentials to publish malicious updates to legitimate Open VSX extensions (‘compromise of the developer’s publishing credentials’).
- [T1059.006 ] Command and Scripting Interpreter: JavaScript – The malicious chain decrypts and executes JavaScript at runtime using eval() in Node.js (‘eval(b);’).
- [T1027 ] Obfuscated Files or Information – The extensions embed AES-encrypted blobs and perform runtime decryption to conceal payloads (‘uses AES-256-CBC to decrypt a long hex string, converts the result to UTF-8, and immediately executes it with eval’).
- [T1102 ] Web Service (third-party/alternative C2) – The loader resolves next-stage configuration from Solana transaction memos, using the blockchain as a dynamic dead drop (‘retrieves its next instruction from a transaction memo on Solana’).
- [T1547 ] Boot or Logon Autostart Execution – Persistence on macOS is achieved by writing a LaunchAgent plist under ~/Library/LaunchAgents to run a Node runtime at login (‘writes a plist under ~/Library/LaunchAgents (e.g., com.user.nodestart.plist) and uses it to start a bundled or downloaded Node runtime’).
- [T1539 ] Steal Web Session Cookie – The payload collects browser cookies and session material across Chromium and Firefox-family browsers (‘collects browser cookies, form history, and login databases across Firefox-family and Chromium-based browsers’).
- [T1552 ] Unsecured Credentials – The implant searches for and harvests developer tokens and credentials including npm _authToken, GitHub artifacts, AWS credentials, and SSH keys (‘inspects npm configuration for _authToken and referencing GitHub authentication artifacts’ and ‘includes ~/.aws (credentials and config) and ~/.ssh (private keys)’).
- [T1041 ] Exfiltration Over C2 Channel – Collected archives are exfiltrated via HTTP POST to hardcoded IP-based endpoints (e.g., POST to /p2p on 45[.]32[.]150[.]251) (‘it POSTs to paths such as /p2p and /2p2 on 45[.]32[.]150[.]251’).
Indicators of Compromise
- [Open VSX Extension Names ] Malicious Open VSX packages published under oorzc – [email protected], [email protected] (and [email protected], [email protected]).
- [Blockchain Address ] Solana dead-drop used for C2 configuration – BjVeAjPrSKFiingBn4vZvghsGj9KCE8AJVtbc9S8o8SC.
- [IP Address ] Exfiltration/C2 endpoints observed – 45[.]32[.]150[.]251 (POST paths observed: /p2p, /2p2).
- [Embedded Crypto Material ] Hardcoded AES material used by staged loaders – AES key: wDO6YyTm6DL0T0zJ0SXhUql5Mo0pdlSz; example IV (hex): c4b9a3773e9dced6015a670855fd32b.
- [File Paths / Artifacts ] Staging, persistence, and indicators on compromised macOS hosts – /tmp/ijewf, /tmp/out.zip, and LaunchAgent plist such as ~/Library/LaunchAgents/com.user.nodestart.plist.
Read more: https://socket.dev/blog/glassworm-loader-hits-open-vsx-via-suspected-developer-account-compromise