Bitdefender researchers uncovered an Android RAT campaign that uses a malicious dropper (TrustBastion) and Hugging Face as a hosting/staging platform to deliver polymorphic APK payloads. The malware abuses Accessibility Services, screen-capture/overlay permissions and fake financial interfaces to steal credentials and exfiltrate data via a C2 at 154.198.48.57. #TrustBastion #HuggingFace
Keypoints
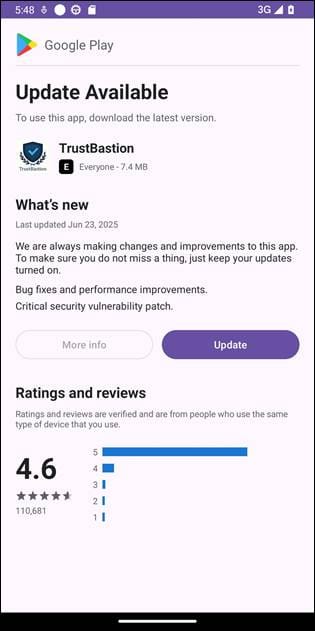
- Attackers distribute a malicious dropper (TrustBastion) via deceptive ads and fake “update” prompts to initiate installation.
- The dropper redirects victims to payloads hosted on Hugging Face datasets rather than directly from attacker-controlled domains.
- Adversaries implemented server-side polymorphism, producing new APK variants roughly every 15 minutes to evade hash-based detection.
- Installed payloads request Accessibility Services, screen recording/casting and overlay permissions to obtain persistent visibility and control.
- The RAT displays fake system and financial interfaces (e.g., Alipay, WeChat) to harvest credentials and lock-screen inputs.
- A centralized C2 infrastructure (domain trustbastion[.]com, IP 154.198.48.57) coordinates payload delivery, commands and data exfiltration.
- The same underlying malicious code was re-used across differently named apps/repositories (TrustBastion → Premium Club) to prolong operations.
MITRE Techniques
- [T1204 ] User Execution – Deceptive update prompts and social-engineering lead users to install and run the dropper (‘the dropper immediately displays a prompt warning users that an update is required to continue using the application.’)
- [T1105 ] Ingress Tool Transfer – Payloads are retrieved from external hosting (Hugging Face) after initial dropper redirection (‘the final APK is downloaded directly from Hugging Face datasets.’)
- [T1027 ] Obfuscated Files or Information – Server-side polymorphism generates frequent APK variants to evade hash-based detection (‘The attackers use server-side polymorphism by producing new payloads roughly every 15 minutes.’)
- [T1113 ] Screen Capture – The malware requests screen-recording and casting permissions to capture on-screen content (‘the payload requests permissions enabling screen recording, screen casting, and overlay display’)
- [T1056 ] Input Capture – Fraudulent authentication interfaces and overlays are used to harvest credentials and inputs (‘displays fraudulent authentication interfaces designed to harvest sensitive credentials.’)
- [T1102 ] Web Service – Legitimate web hosting (Hugging Face) and dataset/CDN links are abused to host and distribute malicious APKs (‘Hugging Face online service is abused to host and distribute dangerous APKs.’)
- [T1071 ] Application Layer Protocol – Persistent C2 communication over network ports is used to receive commands and exfiltrate data (‘C2 endpoint was identified at IP address 154.198.48.57, communicating over port 5000’)
Indicators of Compromise
- [File hash ] dropper/payload samples – d184d705189e42b54c6243a55d6c9502, d8b0fd515d860be2969cf441ea3b620d, and 3 more hashes
- [Domain ] infrastructure and distribution – trustbastion[.]com, au-club[.]top
- [IP address ] C2 and alternative hosts – 154.198.48.57, 108.187.7.133
- [Package name ] malicious app identifiers – rgp.lergld.vhrthg, com.nrb.phayrucq
- [File name ] hosted APK filename – b.apk (used in Hugging Face dataset/CDN download links)
Read more: https://www.bitdefender.com/en-us/blog/labs/android-trojan-campaign-hugging-face-hosting-rat-payload