Koi Security tracked the threat group “DarkSpectre” across multiple campaigns (Zoom Stealer, ShadyPanda, GhostPoster) that collectively affected over 8.8 million users and uncovered a new GhostPoster-linked Opera extension installed nearly 1 million times by December 2025. Their analysis produced 15 prioritized IoCs (three subdomains, seven domains, one IP, four emails), revealed aged-domain reuse and China-hosted infrastructure, and discovered 8,579 email-connected domains for further investigation. #DarkSpectre #GhostPoster
Keypoints
- Koi Security has monitored the threat group “DarkSpectre” for over a year and links it to major campaigns using Zoom Stealer, ShadyPanda, and GhostPoster that impacted more than 8.8 million users.
- Researchers discovered a new DarkSpectre campaign that has affected 2.2 million users and used a GhostPoster-linked Opera browser extension with nearly 1 million installs as of December 2025.
- The team identified 20 initial IoCs then refined the list to 15 IoCs for analysis: three subdomains, seven domains, one IP address, and four email addresses.
- Detailed analysis showed 57 unique client IPs queried one IoC domain (168 DNS queries), DNS history totaling 1,283 resolutions for the seven domains, and domain registrations dating from 2011–2024 indicating use of aged domains.
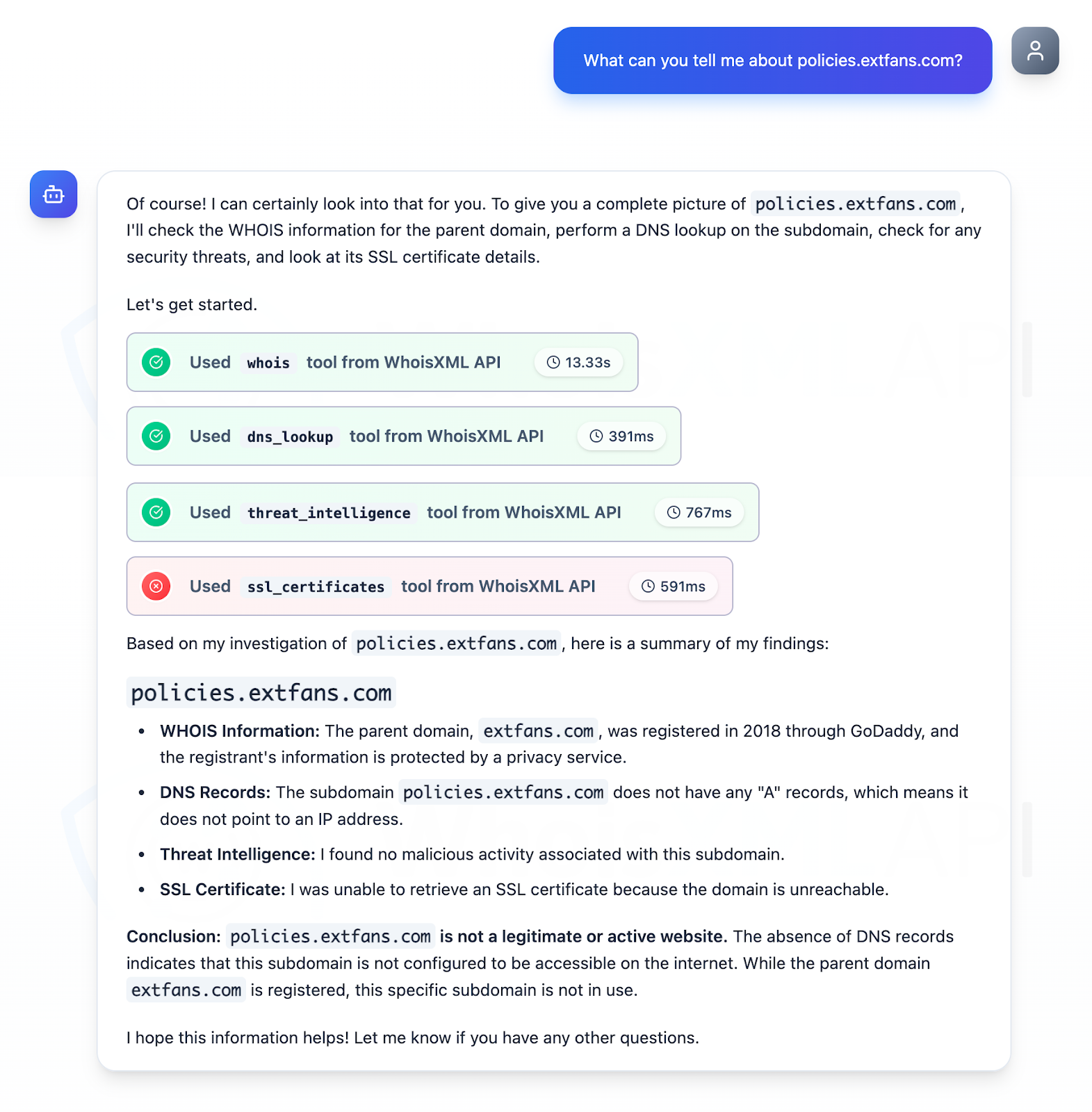
- One subdomain (policies[.]extfans[.]com) was determined to be illegitimate and inactive, while two other subdomains appeared to belong to legitimate infrastructures that could have been compromised.
- The sole IoC IP is geolocated in China under China Unicom but is currently unused and lacked historical domain resolutions; separate queries found three additional IPs (two malicious).
- WHOIS and reverse-WHOIS investigations expanded leads to 8,579 unique email-connected domains and produced additional artifacts available for download from Koi Security’s report.
MITRE Techniques
- [None ] No MITRE ATT&CK techniques were explicitly mentioned in the article.
Indicators of Compromise
- [Subdomains ] Subdomain IoCs analyzed – policies[.]extfans[.]com (illegitimate, currently inactive), plus two additional subdomains tied to legitimate infrastructures that may have been compromised.
- [Domains ] Domain IoCs and context – gmzdaily[.]com, infinitynewtab[.]com, and 5 other domains (7 domains under deeper analysis; DNS history shows 1,283 total resolutions and first resolutions dating as early as 2017).
- [IP addresses ] IP IoCs and context – single IoC IP geolocated in China (administered by China Unicom; currently unused), and three additional IPs discovered (two of which were identified as malicious).
- [Email addresses ] Email IoCs and context – four IoC email addresses (one invalid, one used to register domains, and two other emails identified as legitimate), plus an expanded set of 8,579 email-connected domains discovered via reverse-WHOIS searches.
Read more: https://circleid.com/posts/divulging-the-dns-secrets-of-darkspectre