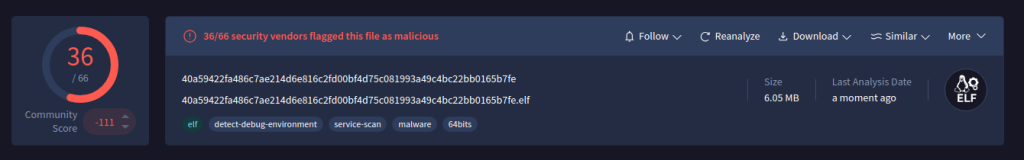
This report analyzes a cross‑platform Python‑based Remote Access Trojan (RAT) packaged as an ELF that performs system fingerprinting, generates a semi‑persistent UID, communicates with an unencrypted HTTP C2 (/api/{uid}/hello), supports threaded remote command execution, unrestricted file transfer, screenshot capture, ZIP bundling, and persistence via XDG autostart and the Windows Run key. K7 Labs observed high detection rates for the sample (MD5: 0fed60850aa38127095f21182cc2c85d) and recommends keeping protections like K7 Total Security up to date. #PythonRAT #K7Labs
Keypoints
- Sample is an ELF that unpacks Python files (agent-svc.pyc / agent.pyc) and contains a single Agent class which performs system fingerprinting and operational tasks.
- The RAT generates a semi‑persistent UID by combining username and MAC address to identify victims across sessions.
- Command-and-control uses unprotected HTTP POSTs to /api/{uid}/hello and sends both system data and command outputs in plaintext without encryption or authentication.
- Persistence mechanisms include creating ~/.config/autostart/dpkgn.desktop on Linux (XDG autostart) and adding a Current User Run registry entry named “lee” on Windows, requiring no admin privileges.
- Remote capabilities include threaded command execution, file enumeration (/tmp/list.txt), unrestricted multipart file upload/download, ZIP archive creation for bulk exfiltration, and screenshot capture via PIL ImageGrab.
- Anti‑forensics and cleanup functions remove persistence entries, delete installation directories, and use post‑reboot RunOnce cleanup on Windows to cover tracks.
MITRE Techniques
- [T1082 ] System Information Discovery – Malware performs system fingerprinting collecting “operating system, hostname, current user” (‘collecting details (as shown in Figure 4) such as : operating system hostname current user’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – C2 uses HTTP POST to communicate with the server at “/api/{uid}/hello” (‘unprotected HTTP POST requests directed at the /api/{uid}/hello endpoint (highlighted in Figure 7), transmitting system data as plain text in JSON format.’).
- [T1041 ] Exfiltration Over Command and Control Channel – Command outputs and collected data are sent in plaintext to the C2 without integrity checks (‘transmitting command output in plaintext without integrity checks or authentication.’).
- [T1547 ] Boot or Logon Autostart Execution – Linux persistence via XDG autostart keeps the agent running at login (‘creating a fake startup file at ~/.config/autostart/dpkgn.desktop which is highlighted in Figure 10.’).
- [T1547.001 ] Registry Run Keys and Startup Folder – Windows persistence is achieved by adding an entry to the Current User Run key named “lee” (‘adding a registry entry in the current user’s Run key (marked in Figure 11). It uses the name “lee” to point to its executable.’).
- [T1083 ] File and Directory Discovery – The RAT enumerates files and produces directory-wide listings for exfiltration (‘it enumerates files on the system by generating a directory-wide file list in /tmp/list.txt and uploading the results to the remote server for further analysis.’).
- [T1105 ] Ingress Tool Transfer – The malware supports downloading files from remote URLs using streamed chunks (‘download() retrieves files from URLs using streamed 8,000‑byte chunks.’).
- [T1113 ] Screen Capture – Screenshots are taken and uploaded to the C2 using PIL ImageGrab (‘Screenshots are captured in a separate thread, recording the entire host screen via PIL’s ImageGrab module (see Figure 18)’).
- [T1070 ] Indicator Removal on Host – The clean/uninstall routine removes persistence components, hidden directories, and startup entries to erase traces (‘clean function shown in Figure 19 is responsible for uninstalling the malware from the victim system by detecting the operating system and removing all persistence components, including hidden directories and startup entries’).
Indicators of Compromise
- [File Hash ] analyzed sample – 0fed60850aa38127095f21182cc2c85d (reported with detection name “Trojan”).
- [File Name ] extracted Python artifacts – agent-svc.pyc, agent.pyc.
- [File Path ] persistence and enumeration artifacts – ~/.config/autostart/dpkgn.desktop, /tmp/list.txt.
- [Registry Value ] Windows persistence – ‘lee’ entry added to Current User Run key to autorun the executable.
- [API Endpoint ] C2 communication – /api/{uid}/hello used for hello/beacon and command exchange.
Read more: https://labs.k7computing.com/index.php/the-pyrat-code-python-based-rat-and-its-internals/