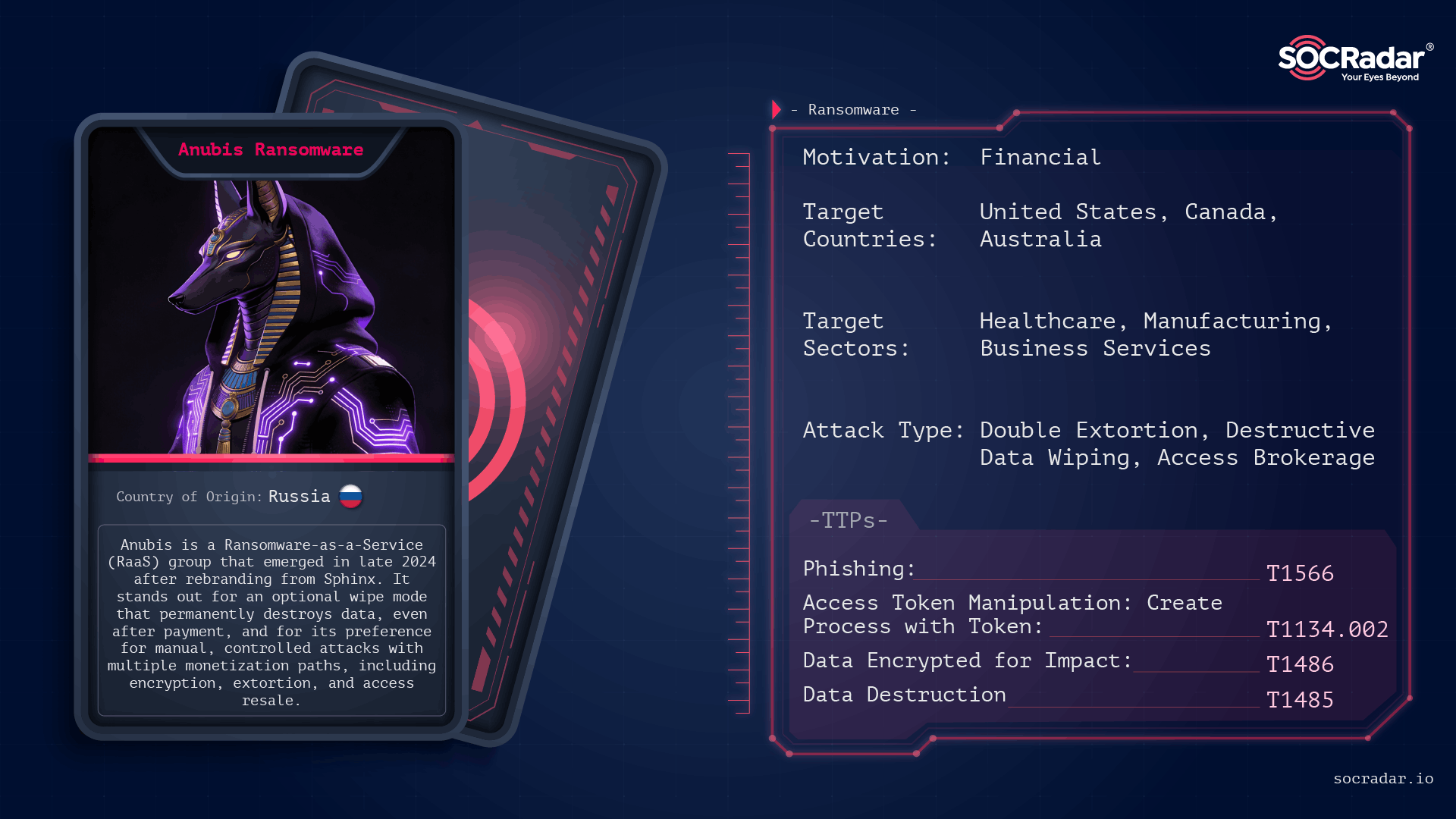
Anubis (formerly Sphinx) is a Ransomware-as-a-Service operation first observed in late 2024 that combines standard file encryption with an optional destructive wipe mode, permanently destroying data and removing decryption as a guaranteed outcome. Its affiliate-driven model and parallel monetization channels (data extortion and access resale) let operators choose between encryption, data-only extortion, or selling access, concentrating on high-value targets and controlled, high-impact intrusions. #Anubis #Sphinx
Keypoints
- Anubis surfaced in late 2024 as a rebrand of earlier Sphinx builds, with near-identical code-level functionality indicating a direct lineage.
- It implements a dual execution model: standard ECIES-based file encryption (.anubis extension) and an optional operator-triggered wipe mode that irreversibly overwrites files.
- The RaaS is affiliate-driven and monetizes via encryption, standalone data extortion, and access resale, allowing affiliates to select the most profitable or least risky outcome for each intrusion.
- Affiliates perform manual, hands-on intrusions (spear-phishing, abused remote services, trojanized installers) and deploy Anubis after achieving sufficient access and data visibility.
- Anubis uses privilege escalation, token manipulation to reach SYSTEM, aggressive defense evasion (process termination, shadow copy deletion), and statically compiled Go binaries with in-memory decryption to hinder analysis.
- Defensive recommendations emphasize reducing external exposure (RDP/VPN), enforcing MFA, immutable/offline backups, detection of pre-encryption behaviors, and prioritizing early containment over recovery due to wipe risk.
MITRE Techniques
- [T1566 ] Phishing – Initial access through spear-phishing emails with malicious documents or compressed executables (‘Anubis affiliates most commonly gain initial access through spear-phishing emails containing malicious documents or compressed executables.’)
- [T1133 ] External Remote Services – Abusing exposed services like RDP for initial access and direct deployment (‘affiliates actively abuse exposed Internet-facing services, particularly Remote Desktop Protocol (RDP).’)
- [T1078 ] Valid Accounts – Use of compromised credentials and brute-force to access remote services (‘Compromised credentials, brute-force attempts, or previously obtained access are used to directly deploy the ransomware.’)
- [T1059 ] Command and Scripting Interpreter – Manual, timed execution often using command-line parameters to control encryption and wipe behavior (‘The ransomware requires explicit command-line parameters to function correctly.’)
- [T1569.002 ] System Services: Service Execution – Controlled execution patterns rather than self-propagation, with operators deploying payloads after reconnaissance (‘Anubis is not designed to self-propagate. Execution is typically manual and timed.’)
- [T1548.002 ] Abuse Elevation Control Mechanism – Attempts to relaunch with elevated rights when not running as admin (‘If not, it attempts to relaunch itself with elevated rights.’)
- [T1134 ] Access Token Manipulation – Escalation to SYSTEM-level via access token manipulation enabling unrestricted interaction (‘When administrative access is available, the malware escalates further to SYSTEM-level execution using access token manipulation techniques.’)
- [T1562.001 ] Impair Defenses: Disable or Modify Tools – Terminates processes for databases, backups, and endpoint protection to unlock files and reduce detection (‘It terminates processes related to databases, backup software, endpoint protection platforms, and productivity applications to unlock files and reduce detection during encryption.’)
- [T1490 ] Inhibit System Recovery – Deletes Volume Shadow Copies and suppresses Windows recovery to limit recovery options (‘Volume Shadow Copies are deleted, Windows recovery options are suppressed, and system artifacts are removed to complicate forensic analysis.’)
- [T1070 ] Indicator Removal on Host – Removes system artifacts and employs anti-analysis checks and in-memory decryption to evade analysis (‘Observed samples also employ in-memory decryption stages and basic anti-analysis checks to evade sandboxing and debugging.’)
- [T1486 ] Data Encrypted for Impact – Hybrid ECIES-based encryption of file contents and renaming to .anubis with HTML ransom notes (‘Encrypted files are renamed with the .anubis extension, and HTML-based ransom notes are dropped across affected directories.’)
- [T1485 ] Data Destruction – Optional operator-activated wipe mode that overwrites files, preventing recovery (‘When enabled, files are overwritten rather than encrypted, resulting in permanent data loss.’)
- [T1048 ] Exfiltration Over Alternative Protocols – Data exfiltration performed prior to encryption using separate tools or legitimate transfer utilities (‘Data exfiltration typically occurs before ransomware execution and is carried out using separate tools or legitimate transfer utilities.’)
- [T1567 ] Exfiltration Over Web Service – Stolen data published via Tor leak sites and used for extortion (‘Stolen data is later leveraged for extortion via Anubis-operated Tor leak sites.’)
Indicators of Compromise
- [File Extension ] Encrypted file marker – .anubis (encrypted files renamed with this extension)
- [File Name ] Ransom note filename – RESTORE FILES.html (HTML-based ransom notes dropped across affected directories)
- [Leak Site / Infrastructure ] Data leak and negotiation portals – Tor-based portals for negotiation and data leak sites (Anubis-operated Tor leak sites)
- [Forums / Underground References ] Promotional and intelligence sources – RAMP, XSS (early advertisements and operator activity on Russian-language forums)
- [Binary Attributes ] Malware build characteristics – Go statically compiled payloads (large statically compiled Go binaries with in-memory decryption and anti-analysis checks)
Read more: https://socradar.io/blog/dark-web-profile-anubis-ransomware/