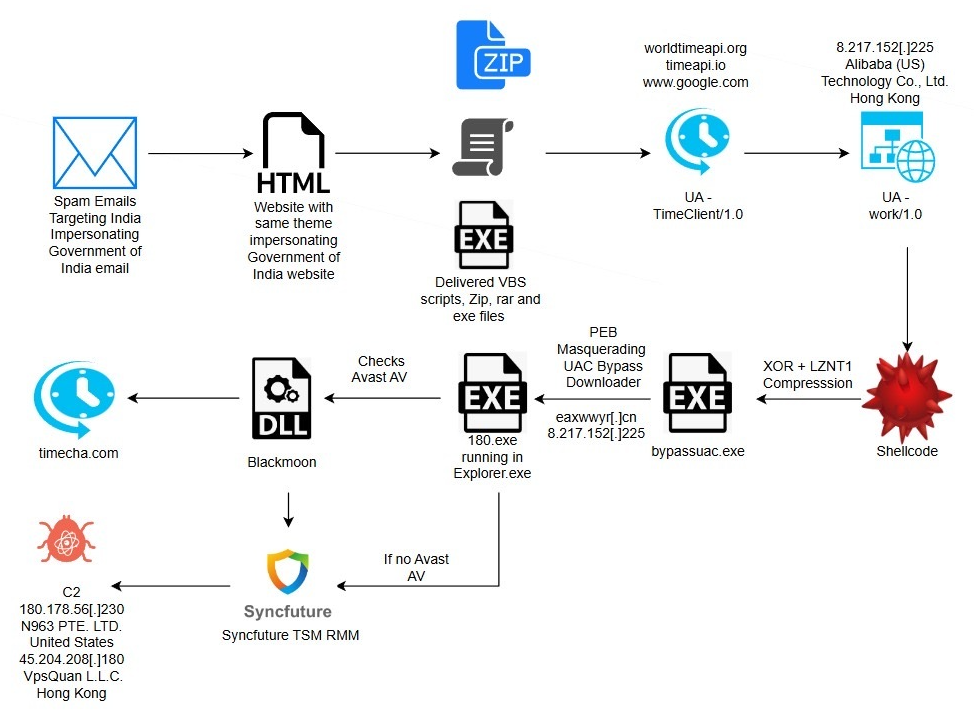
eSentire TRU uncovered a multi-stage espionage campaign targeting residents of India that uses phishing lures impersonating the Income Tax Department to deliver a DLL side-loading loader which fetches shellcode, bypasses UAC via a COM elevation moniker, and ultimately deploys a repurposed SyncFuture TSM platform for persistent remote surveillance. The intrusion chain includes anti-analysis, PEB process masquerading, Avast-specific GUI automation to create antivirus exclusions, service-based Safe Mode persistence, and multiple signed binaries and certificates abused to appear legitimate. #Blackmoon #SyncFuture
Keypoints
- Actors targeted Indian residents with phishing emails impersonating the Income Tax Department and delivering a malicious archive (Inspection.zip) via shortened URLs and SendGrid-hosted senders.
- Initial execution leveraged DLL side‑loading: a legitimate Microsoft-signed binary was used to load a malicious MpGear.dll that implements layered anti-debugging and anti-analysis checks.
- The loader contacted a hardcoded C2 (8.217.152[.]225) to download encrypted shellcode which was XOR-decrypted, LZNT1-decompressed and executed in memory via VirtualAlloc + CreateThread.
- Privilege escalation and defense evasion included a COM-based UAC bypass (COM elevation moniker) and PEB manipulation to masquerade as explorer.exe.
- When Avast Free Antivirus was present, the malware automated mouse clicks to add malicious files to Avast’s exclusion list, enabling stealthy persistence.
- Operators deployed a repurposed commercial SyncFuture/TSM product (signed binaries like Setup.exe, mysetup.exe, MANC.exe) to establish resilient service persistence (configured to run in Safe Mode) and comprehensive monitoring/exfiltration capabilities.
- Multiple valid and abused code-signing certificates (2019–2024), extensive logging, registry modifications, ACL weakening scripts, and Safe Mode service entries were used to ensure long-term espionage-focused access.
MITRE Techniques
- [T1566.001 ] Phishing: Spearphishing Attachment – Used to deliver the malicious archive and lure: (‘”Download Documents” link using the shortened URL “https://surl[.]li/wuvdwi” that redirected victims to a malicious file named “Inspection.zip”‘).
- [T1574.002 ] Hijack Execution Flow – DLL Side‑Loading – A legitimate, signed Microsoft application was used to load a malicious DLL payload: (‘a legitimate, signed Microsoft application is used to load a malicious DLL’).
- [T1218 ] Signed Binary Proxy Execution – Abuse of signed/legitimate binaries and stolen signatures to execute malicious code: (‘legitimate Microsoft Signed binary … used for DLL Sideloading of the malicious payload “MpGear.dll”‘).
- [T1055 ] Process Injection – Shellcode execution in memory via dynamic allocation and thread creation: (‘the malware allocates a new region of executable memory using VirtualAlloc … Execution is transferred to the shellcode by calling CreateThread’).
- [T1548.002 ] Abuse Elevation Control Mechanism – Bypass UAC (COM Elevation Moniker) – The loader uses a file-less COM-based technique to obtain elevated ICMLuaUtil and call ShellExecute in a high-integrity context: (‘uses a well-known, file-less COM-based technique to bypass the User Account Control (UAC) prompt’).
- [T1036 ] Masquerading – Process Masquerading via PEB modification – The malware overwrote PEB ProcessParameters (ImagePathName/CommandLine) and module list entries to appear as explorer.exe: (‘modifies its own Process Environment Block (PEB) to masquerade as the legitimate Windows explorer.exe process’).
- [T1105 ] Ingress Tool Transfer – Download of follow-on payloads and tools from attacker-controlled domains: (‘the binary downloads the next stage “180.exe” from hxxps://eaxwwyr[.]cn domain to the %TEMP% directory’).
- [T1071.001 ] Command and Control: Web Protocols – C2 communication and data transfer over HTTP(S) used to retrieve shellcode and additional stages: (‘contacts a Command-and-Control (C2) server to download a packed shellcode’ and HTTP GET to 8.217.152[.]225:80 ‘/1bin’).
- [T1497 ] Virtualization/Sandbox Evasion and Anti-Analysis – Multi-layered anti-debugging, timing checks, and network time/API checks to detect analysis environments: (‘multi-layered anti-debugging routine’ and attempts to connect to timecha[.]com and other time APIs before proceeding’).
- [T1543.003 ] Create or Modify System Process – Windows Service – Installation of core components as Windows services and SafeBoot registry entries to persist even in Safe Mode: (‘installs a core component as a Windows service, configuring it to run even in Safe Mode’).
- [T1112 ] Modify Registry – Creation and modification of registry keys for persistence and configuration (GcServices and SafeBoot/Svc entries): (‘creates a registry key under HKEY_CURRENT_USERSOFTWAREMicrosoftGcServices’ and SafeBoot service entries under SYSTEMControlSet001ControlSafeBoot*).’
Indicators of Compromise
- [IP Address ] C2 and hosting infrastructure – 8.217.152[.]225 (downloader C2), 103.97.131[.]44 (hosting malicious VBS), and several other hosting IPs.
- [Domain / URL ] Phishing and payload hosts – gfmqvip[.]vip (Inspection.zip host), eaxwwyr[.]cn (stage download), surl[.]li/wuvdwi (shortened phishing URL), and other thematic phishing domains.
- [File Hashes ] Malware binaries and unpacked components – a416892cd439e289f188f9a85c21943b316b3489f70757d0d7df54e4edd9f14b (stage2 PE), 659ff4b41b26b8ea91f7ccf968dc0305ff380571cfe7f70e80d79142142aa1a7 (180.exe), and other hashes (e.g., game-float-core.dll and MANC.exe hashes) and 3 more hashes.
- [File Names ] Delivered or dropped files – Inspection.zip, Inspection Document Review.exe (signed Microsoft loader), MpGear.dll, 180.exe, game-float-core.dll, Setup.exe, mysetup.exe, MANC.exe.
- [Email Addresses ] Phishing sender addresses observed – legroslorna748@gmail[.]com (associated with many .cn domains), weekskataleya@gmail[.]com (associated with t-lebosports[.]cn), and additional actor-controlled addresses.
- [Registry Keys / Paths ] Persistence and configuration indicators – HKCUSOFTWAREMicrosoftGcServices (wlda/wldb values), SafeBoot registry entries under SYSTEMControlSet001ControlSafeBoot* for Manc service, and Avast exclusions path SOFTWAREAvast SoftwareAvastpropertiesexclusionsIDPExcludedFiles.