TrendAI Research analyzed a supply-chain compromise of EmEditor’s official download page in which a modified EmEditor .MSI installer executed PowerShell to retrieve multistage malware. The malware disables PowerShell ETW, harvests credentials from Windows Credential Manager, fingerprints and geofences hosts, and exfiltrates data to a C2 at cachingdrive[.]com #EmEditor #cachingdrive
Keypoints
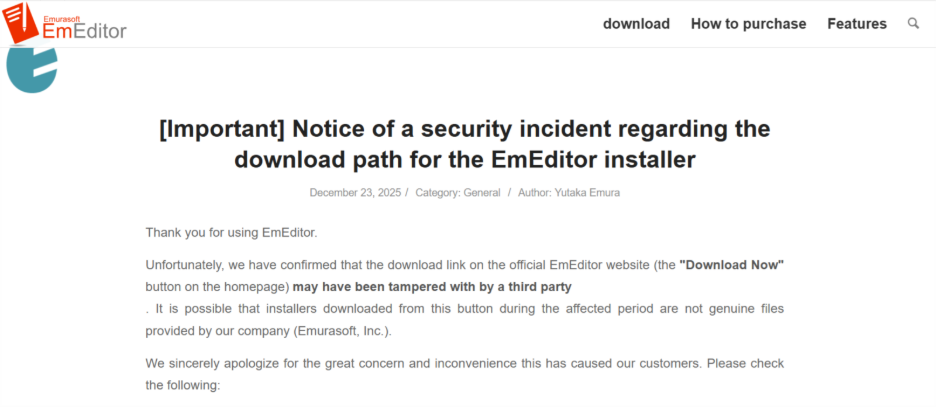
- The EmEditor download page was compromised and a modified .MSI installer was served to users to deliver multistage malware.
- The installer’s CustomAction spawns PowerShell to retrieve and execute obfuscated first-stage scripts hosted on lookalike domains.
- The malware chain performs credential theft (accessing Windows Credential Manager), disables PowerShell ETW, and detects installed security products.
- A separate payload handles system fingerprinting, geofencing (excluding select CIS countries), registry checks, C2 reporting, and data exfiltration.
- The C2 infrastructure observed includes cachingdrive[.]com and consistent campaign string “2daef8cd” embedded in communications.
- TrendAI recommends validating installer integrity, governing PowerShell usage, preserving endpoint telemetry, enforcing least privilege, and securing software distribution infrastructure.
MITRE Techniques
- [T1195 ] Supply Chain Compromise – Used to deliver a modified EmEditor installer to victims via the official download page (‘downloaded from the website of EmEditor. The package (an .MSI file) is modified…’).
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – Installer spawns PowerShell to retrieve first-stage code and execute obfuscated scripts (‘spawn a PowerShell command to retrieve its first-stage code’).
- [T1105 ] Ingress Tool Transfer – Payload retrieval from external URLs using Invoke-WebRequest to fetch follow-on scripts (‘the URLs are executed through the Invoke-WebRequest (IWR) method’).
- [T1555.002 ] Credentials from Password Stores: Windows Credential Manager – Malware accesses the Windows Credential Manager to harvest stored credentials (‘how it accesses the Credential Manager’).
- [T1562.001 ] Impair Defenses: Disable or Modify Tools – Malware disables PowerShell Event Tracing for Windows (ETW) to reduce detection (‘Disable PowerShell Event Tracing for Windows (ETW)’).
- [T1041 ] Exfiltration Over C2 Channel – Collected information is sent to a command-and-control server at cachingdrive[.]com for reporting and exfiltration (‘The malware sends all collected information to its C&C server at: hxxps://cachingdrive[.]com/gate/init/2daef8cd.’).
- [T1012 ] Query Registry – Malware reads registry entries to check for installed security applications (‘Registry checking (for security applications)’).
- [T1057 ] Process Discovery – Malware detects running processes to identify installed security software (‘Process detection (identify the security software installed in the system)’).
- [T1113 ] Screen Capture – Malware takes screenshots of the victim system as part of data collection (‘Taking screenshots’).
- [T1497 ] Virtualization/Sandbox Evasion – Malware includes anti-virtualization checks to detect and evade sandbox or VM environments (‘Anti-virtualization’).
Indicators of Compromise
- [Domain/URL ] malicious download hosts and C2 – emeditorjp.com (compromised download hosting), cachingdrive.com/gate/init/2daef8cd (command-and-control endpoint).
- [URL ] payload retrieval endpoints – emeditorgb.com/run/mg8heP0r (first-stage payload URL), emeditorde.com/gate/start/2daef8cd (secondary payload URL).
- [File Name ] compromised installer – EmEditor .MSI installer with modified CustomAction that executes PowerShell (no specific filename provided in report).
- [String / Campaign ID ] consistent campaign identifier in communications – ‘2daef8cd’ observed across C2 and payload URLs.
- [Command Line / Hunting Query ] detection queries and indicators – example hunting pattern: processCmd:(powershell AND (emeditorjp.com OR emeditorgb.com/run/mg8heP0r OR emeditorde.com/gate/start/2daef8cd OR cachingdrive.com/gate/init/2daef8cd)).
Read more: https://www.trendmicro.com/en_us/research/26/a/watering-hole-attack-targets-emeditor-users.html