Researchers discovered a ClickFix-style macOS lure (macclouddrive.com/s2) that tricks users into pasting a Terminal one-liner which downloads a daemonized Zsh stager that executes a remote AppleScript to harvest browser credentials, Keychain data, crypto wallets, and other sensitive files. The campaign uses the MacSync infostealer with rotating jmpbowl.* C2 domains and conditionally trojanizes Electron wallet apps (Ledger Wallet.app, Trezor Suite.app) to capture PINs and recovery phrases for long-term phishing. #MacSync #jmpbowl
Keypoints
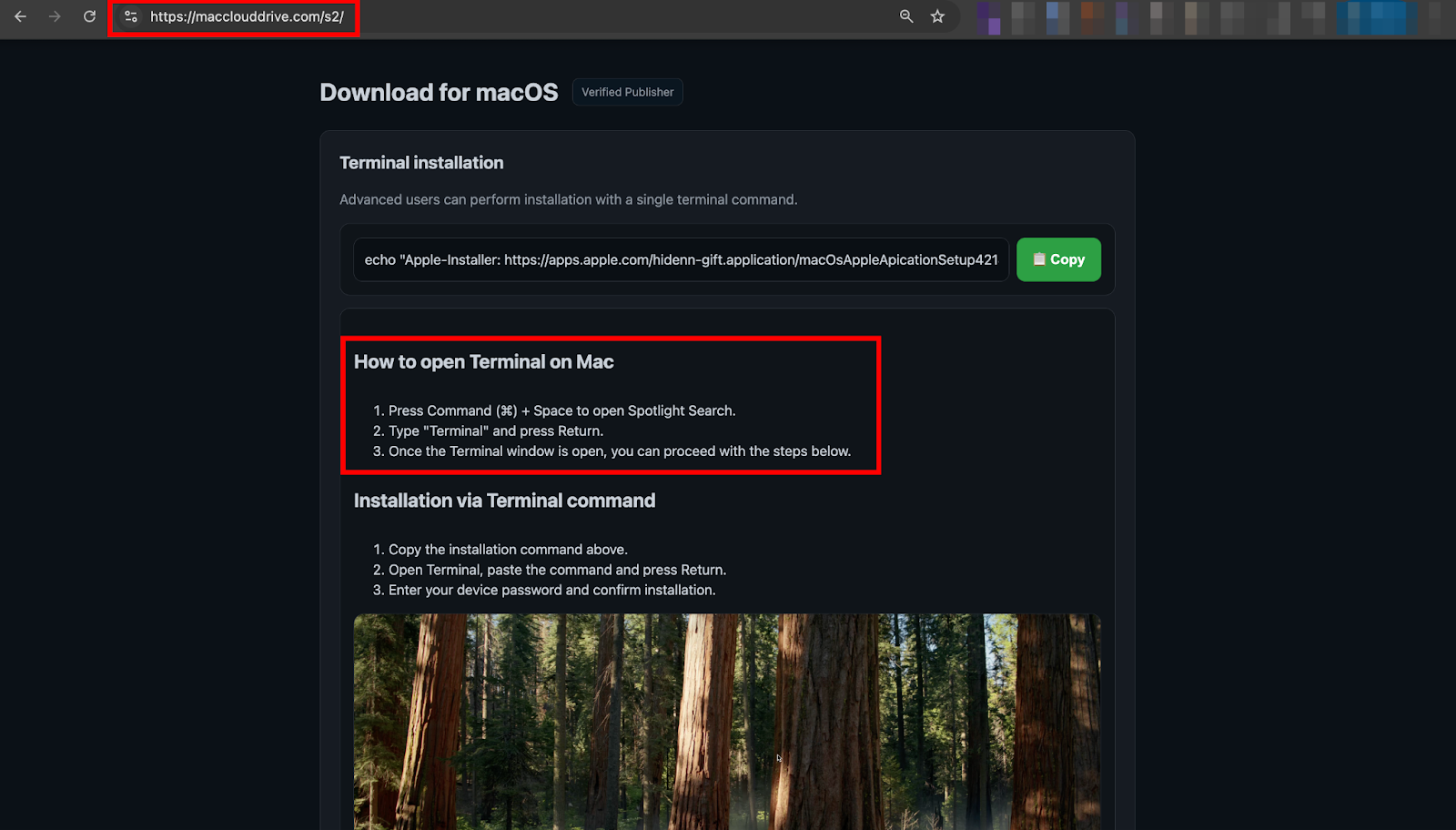
- The attack begins with phishing redirects (e.g., crosoftonline.com/login.srf) to a ClickFix-style lure (macclouddrive.com/s2) that instructs victims to paste a Terminal command to “install” a macOS cloud app.
- The delivered one-liner downloads and executes a compact, obfuscated Zsh stager which daemonizes, fetches a remote AppleScript payload, runs it in-memory via osascript, and uploads a /tmp/osalogging.zip archive to C2.
- The remote AppleScript is the full infostealer: it phishes the macOS login password with repeated fake dialogs, copies Keychain files, browser profiles, extension storage, desktop wallets, SSH/AWS/Kube configs, Telegram sessions, Notes, and opportunistic user files.
- MacSync specifically targets cryptocurrency artifacts—enumerating browser wallet extension IDs, desktop wallet directories, and wallet-related files—enabling offline decryption with the phished system password and high-probability wallet takeover.
- For persistence and high-value phishing, the AppleScript conditionally trojanizes Electron-based wallet companion apps (partial overwrite for Ledger Wallet.app and full replacement for Trezor Suite.app), injecting a multi-step PIN/recovery-phrase wizard and applying ad-hoc codesigning.
- Infrastructure shows active campaign evolution: at least eight rotating jmpbowl.* C2 domains, multiple /v1–/v3 variant paths, and at least five near-identical clone lure sites—indicating affiliate-friendly, scalable MaaS operation.
MITRE Techniques
- [T1566 ] Phishing – Initial delivery and redirection from a spoofed Microsoft login to a ClickFix lure that convinces users to execute a command (‘open Spotlight, launch Terminal, paste the command’).
- [T1204 ] User Execution – Social-engineered trick causing the user to paste and run a malicious shell one-liner in Terminal (‘Copy’ button and instructions to paste the command into Terminal).
- [T1059 ] Command and Scripting Interpreter – Use of shell and AppleScript interpreters to execute staged payloads and in-memory AppleScript via osascript (‘curl … | zsh’ and ‘… | osascript’).
- [T1105 ] Ingress Tool Transfer – Remote retrieval of secondary and component payloads via curl from attacker-controlled URLs (base64-decoded URL ‘http://jmpbowl[.]xyz/curl/89a229f9…’).
- [T1027 ] Obfuscated Files or Information – Delivery of the second-stage Zsh stager compressed and base64-encoded to evade static detection (‘gzip-compressed, then base64-encoded, and embedded as a heredoc’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – C2 and payload delivery over HTTP(S) (requests to ‘http://jmpbowl.xyz/dynamic?txd=’).
- [T1041 ] Exfiltration Over C2 Channel – Upload of the collected loot archive to a C2 endpoint via multipart HTTP POST (‘-F “file=@/tmp/osalogging.zip”‘ to /gate).
- [T1555 ] Credentials from Password Stores – Theft and offline decryption of browser-saved credentials and Keychain data by copying ~/Library/Keychains/ and browser Login Data (‘cp -r …/Library/Keychains/’ and Login Data SQLite extraction).
- [T1005 ] Data from Local System – Recursive copying of filesystem data including wallet directories, SSH keys, AWS/Kubernetes configs, Telegram tdata, Apple Notes, and Desktop/Documents/Downloads files via GrabFolder/GrabFolderLimit handlers (‘GrabFolder() for unrestricted, full copies of critical directories’).
- [T1543 ] Create or Modify System Process – Trojanization of Electron applications by overwriting app.asar and Info.plist and applying ad-hoc codesigning to maintain persistence and deliver phishing UI (‘mv /tmp/app.asar /Applications/Ledger Wallet.app/Contents/Resources/app.asar’ and ‘codesign -f -d -s – /Applications/Ledger Wallet.app’).
Indicators of Compromise
- [Phishing Domain ] ClickFix-style lure and distribution domains – macclouddrive[.]com, macfilevault[.]com, and 4 other macfile*/maccloud* clone sites.
- [C2 Domain ] Credential exfiltration and dynamic payload hosting – jmpbowl[.]xyz, jmpbowl[.]today, and 6 other jmpbowl.* variants.
- [Landing Page / Redirect ] Initial phishing redirect and final lure path – crosoftonline[.]com/login.srf, https://macclouddrive.com/s2/.
- [Exfil Artifact ] Temporary loot archive created and uploaded by the stealer – /tmp/osalogging.zip.
- [File Hashes ] Known malicious files from trojanized Ledger Wallet.app – app.asar SHA-256: ec6bc84be18ce4cb55fb915370c00f2a836ffefc65c6b728efb8d2d28036e376; Info.plist SHA-256: c99dea85f0ef8d3e2f3771c8ebd02d7dee0d90efc5c8392e5c266a59640a4206.
- [File/Path Names ] Overwritten or targeted application bundle components – /Applications/Ledger Wallet.app/Contents/Resources/app.asar, /Applications/Ledger Wallet.app/Contents/Info.plist, /Applications/Trezor Suite.app (full bundle replacement).
- [Command/URL ] One-liner download and execution artifacts – base64-decoded fetch URL example: http://jmpbowl[.]xyz/curl/89a229f9a73cffc67089f388c6c12f3f9d80e7ae2c32745cd5212421a89c3e50 (presented in the paste-to-Terminal command).