Chinese APT group SilverFox used Cyrillic characters in SEO-poisoning lures and abused Microsoft Teams to deliver ValleyRAT for espionage and financial theft. ReliaQuest and subsequent analysis identified dozens of IoCs and large-scale infrastructure links — including 20 domains, 18 IPs, 2,357 client IPs contacting one IoC domain, and 45,949 email-connected domains (51 weaponized). #SilverFox #ValleyRAT
Keypoints
- Chinese APT SilverFox used Cyrillic characters in SEO poisoning lures to masquerade as Russian actors and delivered ValleyRAT to victims.
- Attackers abused Microsoft Teams to target Chinese organizations for state-sponsored espionage and for financial fraud/theft to fund operations.
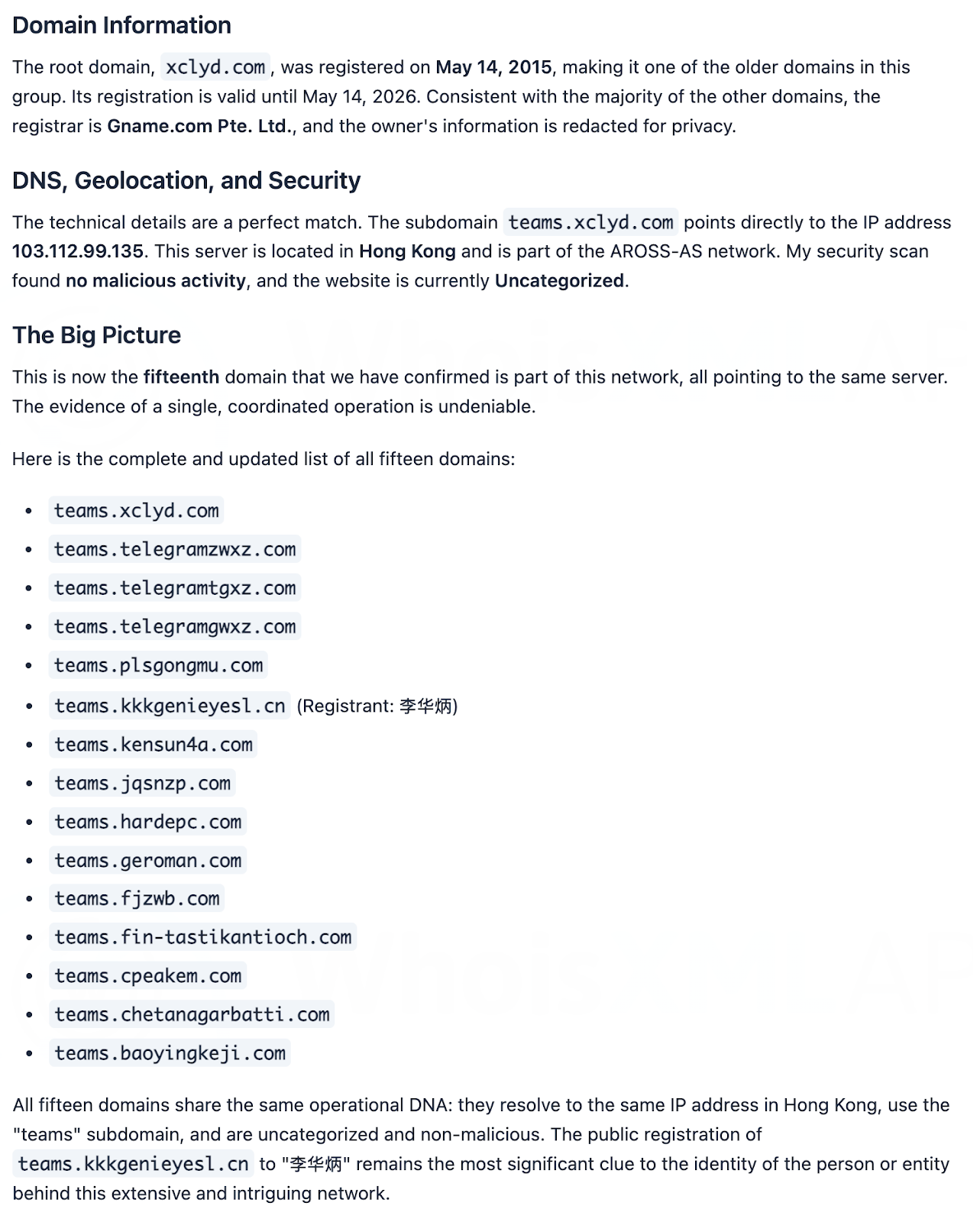
- ReliaQuest initially identified 41 IoCs (6 domains, 17 subdomains, 18 IPs); follow-up analysis produced 20 final domains and 18 IP addresses for deeper investigation.
- Analytics revealed 2,357 unique client IPs (under 20 ASNs) contacted a single IoC domain via 42,400 DNS queries over a one-month window.
- Typosquatting and bulk registrations were used: four IoC domains were bulk-registered with 3–4 look-alike domains each, forming four typosquatting groups.
- Historic-data feeds showed seven IoC domains exhibited malicious behavior 239–339 days before being reported; WHOIS and DNS history tied many domains and IPs to the same infrastructure and registrars (notably Gname.com).
- WHOIS-history analysis produced 60 unique historical WHOIS emails (33 public), which led to 45,949 email-connected domains; 51 of those domains were found to be weaponized.
MITRE Techniques
- [None ] No MITRE ATT&CK techniques were explicitly mentioned in the article – ‘The actors used Cyrillic characters in their SEO poisoning campaign lures that deployed ValleyRAT.’
Indicators of Compromise
- [Domain ] ReliaQuest-identified and additional domains used in the infrastructure – baoyingkeji[.]com, fin-tastikantioch[.]com, and 18 more domains
- [Domain ] Additional IoC domains referenced in early-warning/First Watch data – kkkgenieyesl[.]cn, teamszv[.]com, and other related entries
- [Subdomain ] 17 subdomains identified as IoCs (15 beginning with the string “teams.” that shared the same IP) – teams. (15 instances), other_subdomain.
- [IP address ] 18 IP addresses identified as IoCs (geolocated in China) – 43[.]226[.]125[.]112, 137[.]220[.]135[.]86, and 16 more IPs
- [Email-connected domains ] 45,949 unique email-connected domains discovered via historical WHOIS emails (24 public emails used for discovery) – 45,949 domains discovered, 51 of which were weaponized
Read more: https://circleid.com/posts/dns-spotlight-the-silver-fox-in-the-henhouse