Orion Ransomware is a newly observed operation whose public activity is limited to a data leak site listing 13 alleged victims and affiliate recruitment messaging rather than demonstrated ransomware development or independently verified intrusions. Analysis links the operator to prior reputation-driven extortion activity associated with Babuk2, indicating recycled leak material and low confidence in original operational capability. #Orion #Babuk2
Keypoints
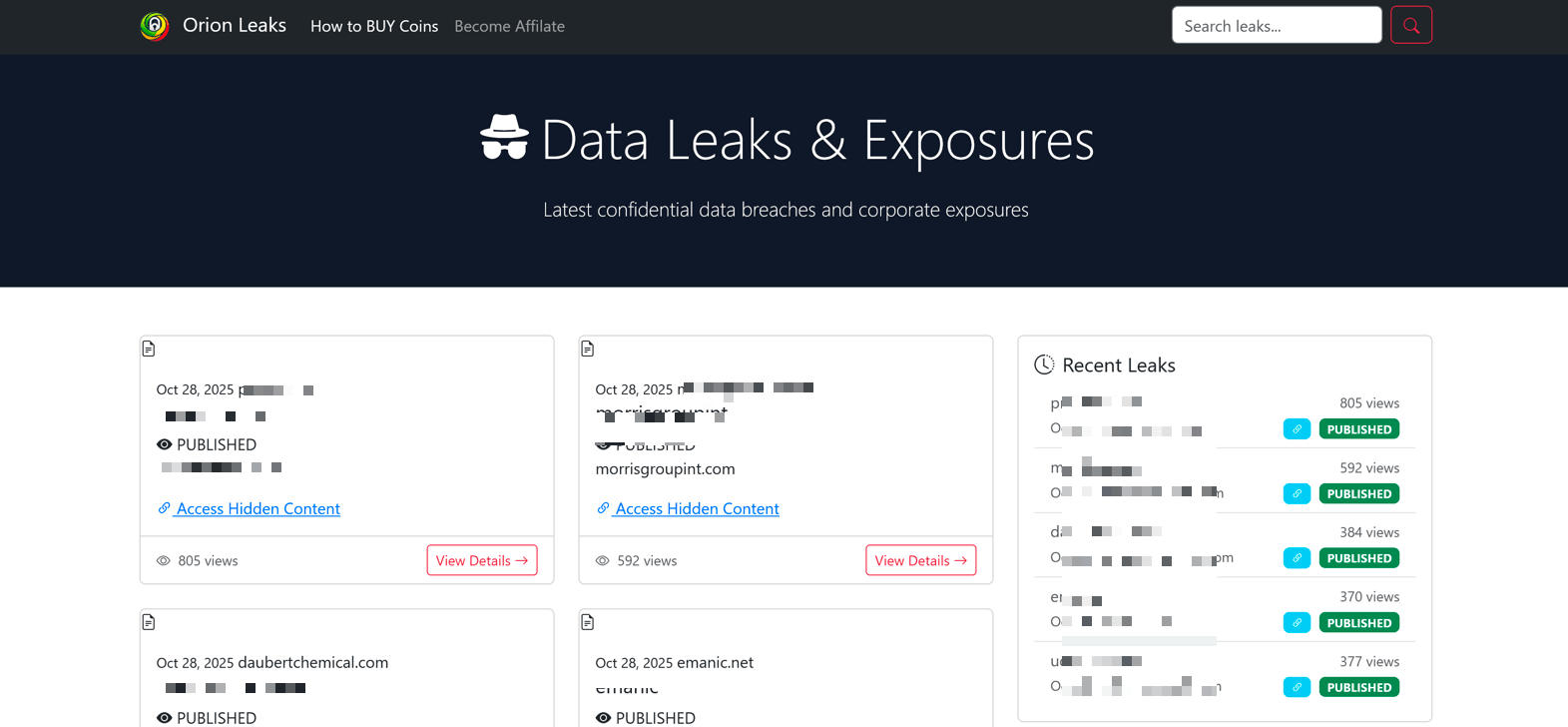
- Orion surfaced via a previously unknown Data Leak Site (DLS) that lists 13 alleged victims, but no independently verified intrusions or original ransomware tooling have been identified.
- The group’s public footprint is primarily leak-site activity and affiliate recruitment rather than demonstrated technical capability or RaaS panel features.
- Recruitment messaging emphasizes exclusivity, anonymity, and fast payouts, resembling access brokerage and data extortion schemes more than mature RaaS operations.
- Infrastructure and contact analysis link the Orion operator to prior Dark Web activity, including a TOX address with a history in access sales and recycled data leaks.
- Multiple victim entries overlap with previous disclosures by established groups such as LockBit and BlackCat (ALPHV), indicating reused or reshared leak material.
- Observed ties to Babuk2-related channels suggest Orion borrows reputation-driven extortion tactics and recycled identities rather than demonstrating unique intrusions.
- SOCRadar assesses Orion as a low-confidence, reputation-based extortion front that still poses reputational and operational risk through data amplification and pressure tactics.
MITRE Techniques
- [None ] No MITRE ATT&CK techniques were explicitly mentioned in the article.
Indicators of Compromise
- [TOX address] operator contact linked to DLS – TOX address used across Dark Web forums and channels (specific address not disclosed)
- [Data Leak Site domain] DLS hosting leak listings – previously unknown DLS detected by SOCRadar (domain not disclosed)
- [Victim listings] alleged victim names and sectors – 13 alleged victims listed with overlap in disclosures by LockBit and BlackCat (no specific organization names provided)
Read more: https://socradar.io/blog/dark-web-profile-orion-ransomware/