VoidLink is an advanced, modular Linux command-and-control framework designed for long-term stealthy access in cloud and container environments, featuring a Zig-written core, a web-based C2 dashboard, and a BOF-like plugin API. It includes 30+ plugins (credential harvesting, container escape, persistence), multiple rootkit techniques (LD_PRELOAD, LKM, eBPF), adaptive OPSEC, and multi-protocol C2 capabilities. #VoidLink #Kubernetes
Keypoints
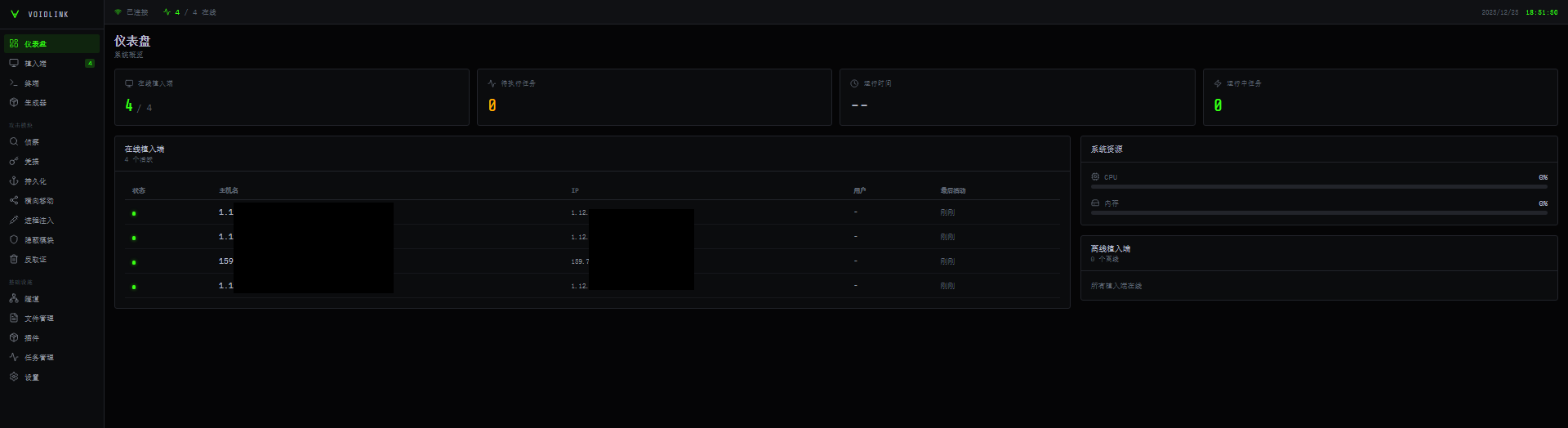
- VoidLink is a cloud-first, modular Linux C2 framework with a web-based dashboard and on-demand implant builder that can generate customized variants and change parameters at runtime.
- The implant is written in Zig, detects cloud providers (AWS, GCP, Azure, Alibaba, Tencent) and container environments (Docker, Kubernetes), and collects cloud- and developer-related credentials and metadata.
- Its plugin ecosystem (37+ default plugins) provides reconnaissance, credential harvesting, persistence (systemd, cron, LD_PRELOAD), container escape, lateral movement, and anti-forensics capabilities.
- VoidLink implements kernel- and user-mode rootkits, selecting LD_PRELOAD, LKM, or eBPF-based techniques based on the host kernel and environment to hide processes, files, and network sockets.
- Adaptive stealth and OPSEC features include runtime code encryption, environment profiling to calculate risk scores, anti-debugging, self-deletion on tamper, and selective slowdown of actions in monitored environments.
- Network communications support multiple transports (HTTP/1.1, HTTP/2, WebSocket, DNS, ICMP) via a unified VoidStream protocol and include advanced HTTP camouflage and potential mesh (P2P) C2 functionality.
- The framework shows rapid development, extensive documentation, and likely Chinese-affiliated authorship, suggesting potential commercial distribution or targeted use; defenders should secure Linux, cloud, and container environments accordingly.
MITRE Techniques
- [T1053.005 ] Scheduled Task/Job: Cron – Used to establish persistence via cron jobs. Quote: (‘cron_persist_v3.oPersistence component that installs or alters cron jobs for persistence.’)
- [T1543 ] Create or Modify System Process – systemd services – Used to achieve persistence by creating or modifying systemd service definitions. Quote: (‘systemd_persist_v3.oPersistence plugin that creates or modifies systemd service definitions so the implant is launched automatically on startup.’)
- [T1574 ] Hijack Execution Flow – LD_PRELOAD / eBPF / LKM – The framework abuses dynamic linker hooks and kernel-level hooking (LD_PRELOAD, eBPF, LKM) to hide or persist code. Quote: (‘It includes rootkit-style capabilities (LD_PRELOAD, LKM, and eBPF)’)
- [T1068 ] Exploitation for Privilege Escalation – Dirty Pipe exploit – Implements a known local kernel exploit to escalate privileges. Quote: (‘exploit_dirty_pipe_v3.oPrivilege-escalation module that implements a Dirty Pipe’)”
- [T1552.001 ] Credentials in Files – SSH and key harvesting – Plugins collect SSH private keys and configuration data for later use or exfiltration. Quote: (‘ssh_harvester_stealth_v3.oPlugin that collects SSH private keys and configuration data from the host for later use or exfiltration.’)
- [T1555.001 ] Credentials from Web Browsers – Browser credential theft – A plugin extracts stored browser credentials, cookies, and similar artifacts. Quote: (‘browser_stealer_v3.oBrowser data theft plugin that targets Chrome and Firefox to extract stored credentials, cookies, and similar artifacts.’)
- [T1055 ] Process Injection – Process injection – Post-exploitation features include process injection capabilities for stealthy code execution. Quote: (‘Attack section organizes post-exploitation activity such as … process injection’)”
- [T1071.001 ] Application Layer Protocol: Web Protocols – C2 over HTTP/HTTPS/WebSocket/DNS/ICMP – VoidLink uses multiple application-layer transports and an HTTP camouflage layer for C2 communications. Quote: (‘supports multiple transport protocols: HTTP/1.1, HTTP/2, WebSocket, DNS, and ICMP.’)
- [T1041 ] Exfiltration Over C2 Channel – Data exfiltration via C2 channels – Exfiltrated files and requests are hidden in PNG-like blobs or as website content across supported transports. Quote: (‘Requests, as well as exfiltrated files, can be hidden in various ways, including via PNG-like blobs, standard website content (JS/CSS/HTML), or by mimicking API traffic.’)
- [T1070 ] Indicator Removal on Host – Anti-forensics and log wiping – Modules clean command histories, login records, system logs, overwrite files, and timestomp to frustrate forensic recovery. Quote: (‘The malware cleans command histories, login records, system logs, and dropped files, all while ensuring that files are not only unlinked from the file system but also overwritten with random data to prevent forensic recovery.’)”
Indicators of Compromise
- [SHA256 Hash ] Stage and implant binaries – 070aa5b3516d331e9d1876f3b8994fc8c18e2b1b9f15096e6c790de8cdadb3fc9, 113025f83ee515b299632d267f94b37c71115b22447a0425ac7baed4bf60b95cd, and 7 more hashes.
- [SHA256 Hash ] VoidLink implant examples – 05eac3663d47a29da0d32f67e10d161f831138e10958dcd88b9dc97038948f69, 15cb93d38b0a4bd931434a501d8308739326ce482da5158eb657b0af0fa7ba49, and other implant hashes.
- [File names ] Plugin object files (ELF .o) – ssh_harvester_stealth_v3.o, docker_escape_v3.o, and 35 more plugin object filenames (total ~37 default plugins).
- [File names ] Persistence and exploit artifacts – systemd_persist_v3.o, exploit_dirty_pipe_v3.o (used for systemd persistence and Dirty Pipe privilege escalation respectively).
Read more: https://research.checkpoint.com/2026/voidlink-the-cloud-native-malware-framework/