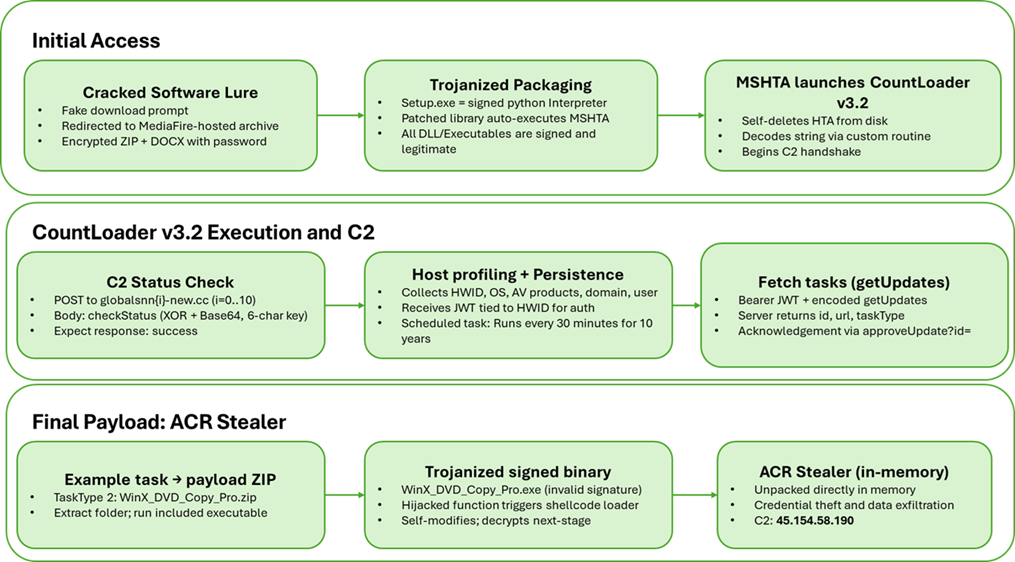
Howler Cell identified a multi-stage campaign distributing a new CountLoader v3.2 variant via cracked software sites that ultimately delivers an in-memory ACR Stealer payload. The loader expands capabilities (nine task types), employs MSHTA/PowerShell fileless execution, removable-media propagation, custom XOR+Base64 C2 encoding, and persistence via scheduled tasks. #CountLoader #ACRStealer
Keypoints
- Distribution through cracked-software download pages and MediaFire-hosted malicious archives containing a trojanized Python runtime and an HTA that launches CountLoader v3.2.
- CountLoader v3.2 increases functionality from six to nine task types, adding removable-media propagation, direct MSHTA/PowerShell in-memory execution, and other delivery methods.
- The loader uses custom encoding (XOR + Base64 with a prepended six-digit key) for C2 communications, obtains a JWT tied to the HWID, and uses it for authenticated task retrieval and acknowledgments.
- Persistence is achieved via scheduled tasks named like “GoogleTaskSystem136.0.7023.12” with a 30‑minute interval; behavior adapts if CrowdStrike Falcon is present.
- CountLoader supports diverse task actions including downloading/executing EXEs, extracting ZIPs and running Python modules, DLL execution via rundll32, MSI silent installs, removable-media LNK propagation, MSHTA launches, and in-memory PowerShell execution.
- The final payload is a trojanized, signed-looking WinX_DVD_Copy_Pro.exe that executes a shellcode loader to unpack and run ACR Stealer entirely in memory; C2 infrastructure is fronted by Cloudflare and hosted on commodity VPS ranges.
MITRE Techniques
- [T1204.001 ] User Execution: Malicious Link – Initial infection via fake download prompts and redirects to hosting (‘After the user clicks the fake download prompt, the site redirects them to a MediaFire link that hosts a malicious archive.’)
- [T1204.002 ] User Execution: Malicious File – Execution of trojanized Python runtime and obfuscated HTA contained in the downloaded archive (‘malicious archive containing trojanized Python library’ and ‘executes an obfuscated HTA script via MSHTA.’)
- [T1047 ] Windows Management Instrumentation – WMI is used to collect OS, user, and AV information for host profiling (‘WMI: Win32_OperatingSystem (Caption, Version), WScript.Network (ComputerName, UserName), Win32_Account (SID)’)
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – PowerShell used for downloading/executing payloads and in-memory execution (‘powershell.exe -Command “irm | iex”‘)
- [T1053.005 ] Scheduled Task/Job: Scheduled Task – Persistence via created scheduled task like “GoogleTaskSystem136.0.7023.12” + GUID to run MSHTA periodically (‘Creates persistence using Scheduled Task with name “GoogleTaskSystem136.0.7023.12” + ‘)
- [T1218.005 ] System Binary Proxy Execution: Mshta – MSHTA invoked to execute remote HTA payloads and as a task execution vector (‘mshta.exe ‘ and invoked as part of persistence/fallback execution)
- [T1218.007 ] System Binary Proxy Execution: Msiexec – MSI installers downloaded and silently installed as a task type (‘msiexec.exe /i “package.msi” /quiet /qn’)
- [T1218.011 ] System Binary Proxy Execution: Rundll32 – Downloaded DLLs executed via rundll32 with specified export names (‘rundll32 “module.dll”, ‘)
- [T1197 ] BITS Jobs – BITS used as one of the redundant download mechanisms (‘bitsadmin.exe /transfer “” /download /priority foreground “” “”‘)
- [T1518.001 ] Software Discovery: Security Software Discovery – AV enumeration via WMI to detect products such as CrowdStrike Falcon (‘WMI: rootSecurityCenter2 -> AntiVirusProduct (SELECT displayName)’)
- [T1087.002 ] Account Discovery: Domain Account – Tasks collect domain account details and Domain Admins membership for reconnaissance (‘Collects and exfiltrates extensive system/domain reconnaissance … Domain Admins members’)
- [T1069.002 ] Permission Groups Discovery: Domain Groups – Enumeration of user group memberships and permission groups for targeted reconnaissance (‘Collects and exfiltrates extensive system/domain reconnaissance (current user group memberships, Domain Admins members)’)
- [T1482 ] Domain Trust Discovery – Collection of domain/forest data as part of reconnaissance tasks (‘Collects and exfiltrates extensive system/domain reconnaissance (computer role, domain/forest data, current user group memberships)’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – C2 communications over HTTP POST to domains like globalsnn*-new.cc to check status and retrieve tasks (‘The script identifies an active C2 by sending POST requests to domains in the format globalsnn{i}-new[.]cc’)
- [T1132.001 ] Data Encoding: Standard Encoding – Use of Base64 in the C2 encoding routine (‘blob = base64.b64encode(bytes(packed)).decode(“ascii”)’)
- [T1132.002 ] Data Encoding: Non-Standard Encoding – Custom XOR + prepended key scheme to obfuscate C2 traffic (‘a random six-digit key is generated and used as an XOR key to encode the Base64 representation of the plaintext.’)
- [T1091 ] Replication Through Removable Media – Propagation via removable media by creating malicious LNKs that launch MSHTA to re-infect hosts (‘Propagates via removable media by creating malicious LNK shortcuts next to hidden originals; the shortcut executes the original file and then launches the malware via mshta with a C2 parameter.’)
- [T1041 ] Exfiltration Over C2 Channel – Exfiltration of host reconnaissance and task results to C2 endpoints (‘Posts the collected information to C2 tagging it with the task’s id.’ and use of C2 POST endpoints for data exchange)
Indicators of Compromise
- [File Hash ] CountLoader and final payload samples – eac4f6a197b4a738c2294419fda97958b45faee3475b70b6ce113348b73eab3b, d261394ea0012f6eaddc21a2091db8a7d982d919f18d3ee6962dc4bb935d5759, and 10 more hashes
- [IP Address ] C2 server addresses observed – 45[.]154[.]58[.]190 (ACR Stealer C2), 172[.]67[.]173[.]229 (infrastructure fronting)
- [Domain ] Malicious C2 and distribution domains – globalsnn2-new[.]cc, alphazero1-endscape[.]cc, and 9 more related domains
- [File Name ] Malicious binaries/archives used in campaign – WinX_DVD_Copy_Pro.exe (trojanized signed binary), Setup.exe (renamed Python interpreter used for sideloading)
Read more: https://www.cyderes.com/howler-cell/acr-stealer-rides-on-upgraded-countloader