A kernel-mode malicious driver (ProjectConfiguration.sys) signed with a leaked certificate was used to inject a new ToneShell backdoor into system processes and to protect malicious files, registry keys, and user-mode processes. This activity is attributed to the HoneyMyte APT and uses ToneShell connecting to avocadomechanism[.]com and potherbreference[.]com for C2 communication. #ToneShell #HoneyMyte
Keypoints
- Attackers deployed a signed kernel-mode mini-filter driver (ProjectConfiguration.sys) that registers with the Filter Manager and intercepts file and registry operations to prevent removal or detection.
- The malicious driver contains embedded user-mode shellcodes and injects a small svchost stub followed by the ToneShell backdoor into a protected svchost process.
- ToneShell in this campaign provides a reverse shell and file upload/download capabilities, communicating over raw TCP on port 443 with fake TLS headers to avocadomechanism[.]com and potherbreference[.]com.
- The driver protects registry keys and processes by registering registry callbacks, ObRegisterCallbacks, and PsSetCreateProcessNotifyRoutine, and by altering WdFilter altitude to evade Microsoft Defender.
- API calls are resolved dynamically via a hashing algorithm and the driver locates kernel modules using ZwQuerySystemInformation to obscure its behavior.
- Victims were primarily government organizations in Southeast and East Asia (notably Myanmar and Thailand) and many had prior HoneyMyte tools like ToneDisk and PlugX present.
MITRE Techniques
- [T1215 ] Kernel Modules and Extensions – The attacker deployed a signed kernel-mode mini-filter driver that registers with the Filter Manager to intercept I/O and hide artifacts (‘registers as a mini-filter driver on infected machines’).
- [T1055 ] Process Injection – The driver injects user-mode payloads and the ToneShell backdoor into a spawned svchost process (‘inject a backdoor Trojan into the system processes’ / ‘injects the backdoor code into user-mode processes’).
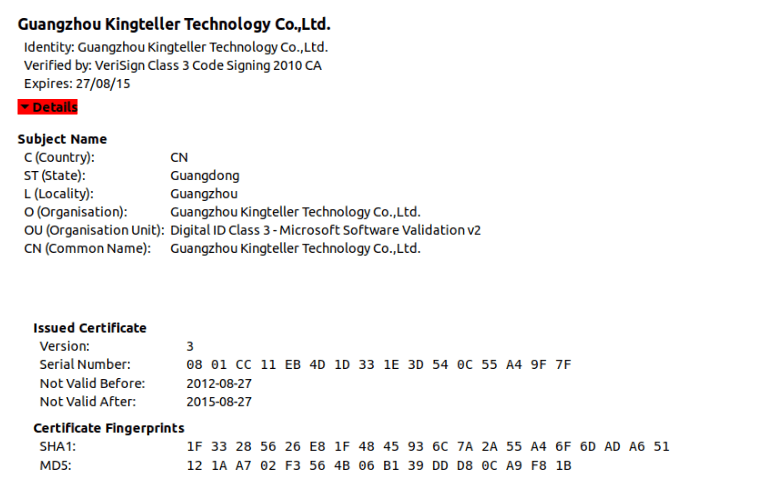
- [T1553.002 ] Code Signing – The driver and other malicious files were signed with an old/stolen digital certificate from Guangzhou Kingteller Technology Co., Ltd. (serial ’08 01 CC 11 EB 4D 1D 33 1E 3D 54 0C 55 A4 9F 7F’) (‘signed with a digital certificate from Guangzhou Kingteller Technology Co., Ltd.’).
- [T1027 ] Obfuscated Files or Information – Attackers used dynamic API resolution from hash values and embedded shellcode to hide behavior (‘dynamic resolution of the required API addresses from hash values’).
- [T1112 ] Modify Registry – The malware builds and protects registry paths and tampers with registry entries including changing WdFilter’s altitude to prevent it from loading (‘tamper with the altitude assigned to WdFilter, … changes it to 0’).
- [T1562.001 ] Disable or Modify Tools – By setting WdFilter altitude to 0 the malware prevents Microsoft Defender’s filter from being loaded, effectively disabling a security control (‘effectively preventing WdFilter from being loaded into the I/O stack’).
- [T1071.004 ] Application Layer Protocol: Custom Command and Control Protocol – ToneShell communicates over raw TCP on port 443 and disguises traffic with fake TLS headers (”ToneShell communicates with its C2 over raw TCP on port 443 while disguising traffic using fake TLS headers”).
- [T1543.003 ] Create or Modify System Process: Windows Service – The driver creates a registry service entry and uses the name ProjectConfiguration for its service registration (‘The registry key created for the driver’s service uses the same name, ProjectConfiguration’).
Indicators of Compromise
- [File hash ] driver and related samples – 36f121046192b7cac3e4bec491e8f1b5, fe091e41ba6450bcf6a61a2023fe6c83, and 1 more hash
- [File name ] malicious driver and related modules – ProjectConfiguration.sys, AppvVStram_.sys
- [Domain ] ToneShell C2 servers – avocadomechanism[.]com, potherbreference[.]com
- [Certificate ] code-signing certificate – Guangzhou Kingteller Technology Co., Ltd., serial number 08 01 CC 11 EB 4D 1D 33 1E 3D 54 0C 55 A4 9F 7F
- [Registry keys ] protected/used by driver – ProjectConfiguration, ProjectConfigurationInstances, ProjectConfiguration Instance
Read more: https://securelist.com/honeymyte-kernel-mode-rootkit/118590/