Phantom 3.5 is distributed via a fake “Adobe 11.7.7 installer” that downloads an obfuscated PowerShell payload (floor.ps1) from hxxp[:]//positivepay-messages.com/file/floor[.]ps1, decrypts an RC4/base64 payload and injects a reconstructed .NET stealer into Aspnet_compiler.exe using a BLACKHAWK.dll injector. The stealer harvests browser master keys, cookies, wallets, credentials, screenshots, keylogs and other PII, uses anti-analysis and Heaven’s Gate techniques to evade detection, persists via Run registry entries, and exfiltrates data over SMTP/FTP/Telegram. #Phantom #BLACKHAWK
Keypoints
- Initial vector: a fake installer file “Adobe 11.7.7 installer” submitted to VirusTotal that downloads a PowerShell downloader from hxxp[:]//positivepay-messages.com/file/floor[.]ps1.
- Execution chain: obfuscated .xml with embedded JavaScript launches PowerShell with hidden/bypass flags, which retrieves and RC4/base64-decodes a secondary payload executed in-memory.
- Injector: a decoded .NET DLL named BLACKHAWK.dll is loaded into the CLR and injects a PE payload into Aspnet_compiler.exe memory (process injection) to evade detection.
- Anti-analysis and self-removal: the stealer contains extensive anti-analysis checks (112 hardcoded usernames), a SelfDestruct ‘Melt’ routine that writes a batch to kill and delete the process, and uses sandbox/analysis detection.
- Credential theft: extracts browser AES master keys, cookies, saved logins, credit cards, crypto wallet data, Wi‑Fi passwords, FileZilla/Discord/Outlook credentials, and arbitrary files from the system.
- Evasion and persistence: implements Heaven’s Gate to bypass user-mode hooks, allocates and executes shellcode in unmanaged memory, and creates Run registry entries for persistence.
- Data exfiltration and capabilities: captures screenshots and keylogs, stages data in temp files (deleted after use) and exfiltrates via SMTP/FTP/Telegram; many artifacts and hashes were observed and logged.
MITRE Techniques
- [T1059.001 ] PowerShell – Used to execute the downloaded script with hidden and bypass flags: ‘It executes the script using PowerShell with hidden attribute and bypassing PowerShell feature that consents to the user before executing any script.’
- [T1105 ] Ingress Tool Transfer – Downloaded secondary payload from a remote URL: ‘it contacts the URL hxxp[:]//positivepay-messages.com/file/floor[.]ps1 and downloads the file floor.ps1.’
- [T1055 ] Process Injection – Injects a PE payload into Aspnet_compiler.exe using typical APIs: ‘WriteProcessMemory, VirtualAllocEx, ResumeThread,… malwares typically uses these functions to perform Process Injection.’
- [T1027 ] Obfuscated Files or Information – Multiple layers of obfuscation and encryption (obfuscated XML/JS, RC4, base64) to hide payloads: ‘The file is an obfuscated .xml file with a JavaScript embedded within.’
- [T1547.001 ] Registry Run Keys/Startup Folder – Creates Run registry entry for persistence: ‘the stealer creates a Run entry for persistence.’
- [T1497.001 ] Virtualization/Sandbox Detection – Anti-analysis checks for known usernames and environment indicators: ‘it matches the user name against a list of usernames.’
- [T1056.001 ] Input Capture: Keylogging – Captures keystrokes and segments words by tab/space/return: ‘It captures the keypresses, differentiates each word by tracking ‘tab’, ‘space’, ‘return’ keys and saves it to a file.’
- [T1113 ] Screen Capture – Periodically captures screenshots of the user session: ‘it also takes a screenshot every 1000ms interval.’
- [T1041 ] Exfiltration Over C2 Channel (Email/Other protocols) – Uses SMTP, FTP, Telegram and Discord channels to upload and send stolen data: ‘it uses various channels like SMTP, FTP protocols. It also uses Telegram to upload the collected information as well as send logs through Discord and Telegram.’
- [T1555.003 ] Credentials from Web Browsers – Extracts browser master keys, cookies, wallets and saved credentials from Chromium/Edge/Firefox: ‘the stealer extracts AES masterkey and app-bound private keys used for encryption of data in browsers like Chromium, Edge, etc.’
Indicators of Compromise
- [File name / Hash ] Installer and payload hashes – Adobe 11.7.7 Installer (01B397CBD39F7DD310CC1252B19DE411), floor.ps1 (CCCDCBF3C3B6C16AB4743A1289327439), and 3 more hashes.
- [DLL / Hash ] Injectors and components – BLACKHAWK.dll (2BE5F6AFA114EE5607D88BC5AEEC4D32), RC4 decrypted script (F39EFF2188EE90A9CB48CE90A09FEFB3).
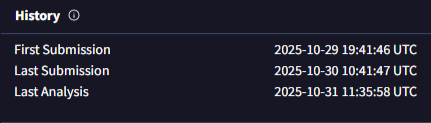
- [Malware sample hash ] Stealer sample – Phantom 3.5 stealer (MD5 052777DBDE7D784903467ED572F7AAD7) – memory-reconstructed PE matched VirusTotal first-seen dates.
- [URL / Domain ] Downloader URL – hxxp[:]//positivepay-messages.com/file/floor[.]ps1 (domain: positivepay-messages.com) used to fetch floor.ps1.
- [Executable name ] Process used for injection – Aspnet_compiler.exe observed being created and used as the host process for injected payload.
Read more: https://labs.k7computing.com/index.php/phantom-3-5-initial-vector-analysis-forensics/