This report describes a configuration extraction pipeline for a lightweight Linux backdoor derived from TinySHell that provides silent, persistent remote access while hiding identifiable metadata. The extractor embeds FLARE capa rules to locate an RC4 decryption routine and combines Capstone and LIEF to reconstruct stack-based RC4 keys and decrypt configuration blobs (including the C2 address) stored in the .rdata section. #TinySHell #FLAREcapa
Keypoints
- The analyzed backdoor is a stripped ELF derived from TinySHell, designed for silent, persistent remote access and long-term espionage.
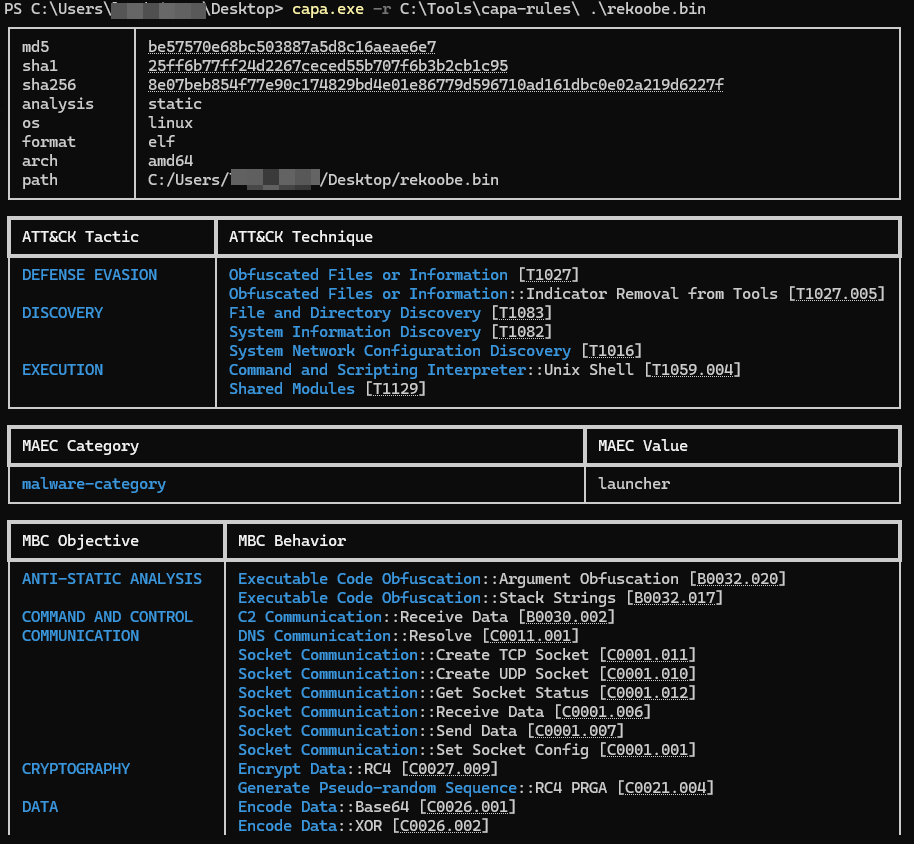
- A public sample (SHA256: 8e07beb854f77e90c174829bd4e01e86779d596710ad161dbc0e02a219d6227f) from Malware Bazaar was used to demonstrate the extraction process.
- The malware obfuscates strings using RC4; a single RC4 routine is reused to protect configuration data and feature flags.
- The extractor embeds a minimal subset of FLARE capa rules to reliably locate the RC4 PRGA function in the stripped binary.
- Capstone is used to trace instructions and reconstruct stack-built RC4 keys, while LIEF extracts contiguous encrypted blobs from the .rdata section.
- Decrypted configuration strings follow the format “:;;;;” allowing straightforward parsing of the C2 indicator.
- The complete extractor code is published on the project’s GitHub repository and the approach emphasizes a lightweight, focused static-analysis pipeline.
MITRE Techniques
- [T1027 ] Obfuscated Files or Information – RC4 is used to conceal configuration strings and metadata (‘obfuscates its string using RC4 encryption.’)
- [T1071 ] Application Layer Protocol – The backdoor communicates with a command-and-control server using a custom authentication protocol (‘connects to its command-and-control server using a custom authentication protocol’)
- [T1059.004 ] Command and Scripting Interpreter: Unix Shell – The backdoor can execute commands or spawn a remote shell on compromised Linux hosts (‘capable of executing commands or spawning a remote shell.’)
- [T1573 ] Encrypted Channel – Configuration and communications use custom/authenticated methods and encrypted blobs to hinder analysis (‘obfuscated configuration blobs—stored contiguously in the .rdata section’)
Indicators of Compromise
- [File hash ] sample used for analysis – 8e07beb854f77e90c174829bd4e01e86779d596710ad161dbc0e02a219d6227f
- [Binary section ] storage location for encrypted blobs – .rdata section (encrypted configuration strings stored contiguously)
- [Function address ] identified RC4 routine – example RC4 function address 0x402c81 (used as the detection target in capa/IDA)
- [Configuration pattern ] decrypted config format – “:;;;;” (used to extract the C2 indicator)