ESET discovered a previously undocumented China-aligned APT group, LongNosedGoblin, using Group Policy and cloud services to deploy a diverse C#/.NET toolset for cyberespionage against governmental entities in Southeast Asia and Japan. The toolset includes NosyHistorian (browser-history collection), NosyDoor (OneDrive-based backdoor with AppDomainManager injection), NosyStealer, NosyDownloader, NosyLogger, and supporting utilities. #LongNosedGoblin #NosyDoor
Keypoints
- LongNosedGoblin is a newly identified China-aligned APT active since at least September 2023, focused on cyberespionage against government entities in Southeast Asia and Japan.
- The group leverages Active Directory Group Policy for malware deployment and lateral movement across compromised networks.
- Primary toolset is custom and C#/.NET-centric, including NosyHistorian (collects browser history), NosyDoor (OneDrive C2 backdoor), NosyStealer, NosyDownloader, NosyLogger, ReverseSocks5, and an argument runner for FFmpeg-based recording.
- NosyHistorian gathers browser histories and uploads them to an internal SMB share to select high-value targets for follow-up compromise with NosyDoor.
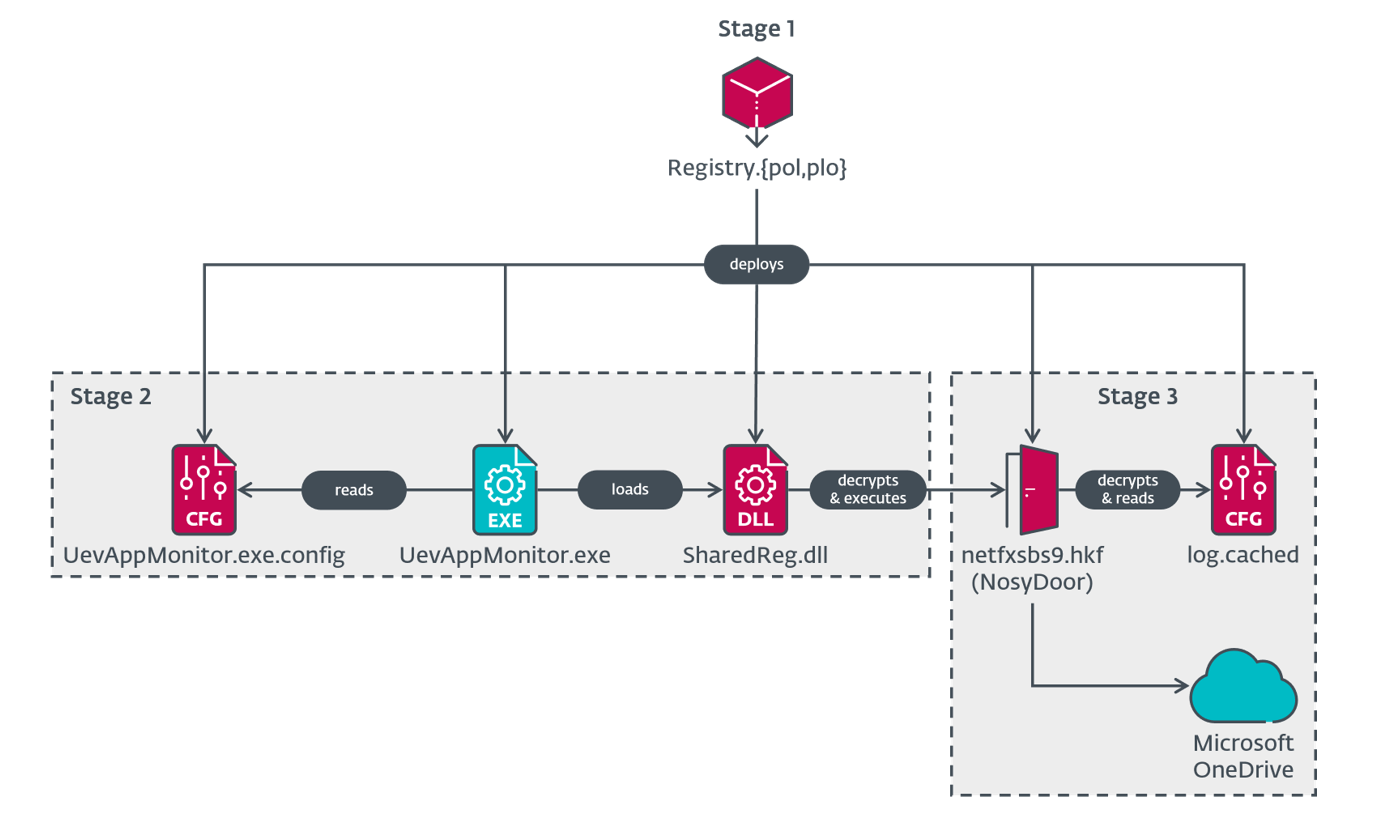
- NosyDoor uses a three-stage chain (dropper → AppDomainManager injection → backdoor), encrypts metadata with RSA, uses AES for payloads/commands, and stores commands/results on cloud storage (.max files on OneDrive).
- The group repeatedly bypasses AMSI, persists via scheduled tasks, uses living-off-the-land techniques (UevAppMonitor), and includes execution guardrails limiting activity to selected machines.
- Evidence suggests NosyDoor may be shared or sold to other China-aligned actors (variants using Yandex Disk and PDB hints like “Paid”), but LongNosedGoblin is distinguished by Group Policy abuse and its unique toolset.
MITRE Techniques
- [T1585.003 ] Establish Accounts: Cloud Accounts – Created cloud-based accounts and used cloud services for C2 and communication (‘LongNosedGoblin created accounts on cloud-based services for C&C communication.’)
- [T1588.001 ] Obtain Capabilities: Malware – Used and likely shared custom malware such as NosyDoor (‘LongNosedGoblin likely used shared malware that we named NosyDoor.’)
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – NosyDownloader executes obfuscated PowerShell command stages (‘NosyDownloader executes PowerShell commands.’)
- [T1059.003 ] Command and Scripting Interpreter: Windows Command Shell – NosyDoor can execute commands via cmd.exe as part of its command set (‘NosyDoor may execute commands via cmd.exe.’)
- [T1106 ] Native API – NosyStealer Stage 1 uses native API calls to load subsequent stages via LoadLibraryW (‘NosyStealer Stage 1 executes the next stage via the LoadLibraryW API.’)
- [T1053.005 ] Scheduled Task/Job: Scheduled Task – Multiple components persist using Windows scheduled tasks (OneDrive Reporting Task, Daily Check Task) (‘NosyDoor and NosyStealer are persisted using Windows scheduled tasks.’)
- [T1574.014 ] Hijack Execution Flow: AppDomainManager – NosyDoor Stage 2 uses AppDomainManager injection via UevAppMonitor.config to load malicious SharedReg.dll (‘AppDomainManager injection to run malicious code.’)
- [T1027.013 ] Obfuscated Files or Information: Encrypted/Encoded File – NosyDoor Stage 1 embeds and DES-encrypts files inside the dropper (‘Malicious files embedded in NosyDoor Stage 1 are encrypted via DES.’)
- [T1027.015 ] Obfuscated Files or Information: Compression – NosyDownloader final stage is compressed with gzip before execution (‘NosyDownloader Stage 4 is compressed using gzip.’)
- [T1622 ] Debugger Evasion – NosyLogger checks for debuggers and halts if one is present (‘NosyLogger does not operate if a debugger is present.’)
- [T1480 ] Execution Guardrails – Some NosyDoor droppers contain machine-name guardrails to limit execution to specific victims (‘Some samples of NosyDoor operate only on machines with specific names.’)
- [T1564.003 ] Hide Artifacts: Hidden Window – NosyDownloader launches a hidden PowerShell window to execute stages invisibly (‘NosyDownloader creates a PowerShell process with a hidden window.’)
- [T1562.001 ] Impair Defenses: Disable or Modify Tools – Multiple tools bypass or patch AMSI to evade detection (‘NosyDoor Stage 2, NosyStealer Stage 3, and NosyDownloader bypass AMSI.’)
- [T1036.005 ] Masquerading: Match Legitimate Name or Location – Malware files masquerade as legitimate configuration files (Registry.pol/History.ini) to blend into Group Policy cache (‘NosyHistorian Stage 1 was observed with the name Registry.pol, masquerading as a Registry Policy file.’)
- [T1218 ] Signed Binary Proxy Execution – Droppers use a legitimate UevAppMonitor.exe copied into Framework directory as a LOLBin to launch malicious config-driven code (‘NosyDoor Stage 1 executes the next stage by leveraging the legitimate UevAppMonitor.exe.’)
- [T1055 ] Process Injection – NosyStealer injects shellcode into pmp.exe or notepad.exe using CreateRemoteThread and SetThreadContext/ResumeThread (‘One observed NosyStealer Stage 2 injects Stage 3 to pmp.exe via CreateRemoteThread… the other injects to notepad.exe via SetThreadContext.’)
- [T1620 ] Reflective Code Loading – Donut reflective loader is used to load embedded PE files in memory for NosyStealer stages (‘Donut has been used to execute NosyStealer Stage 3 and Stage 4 in memory.’)
- [T1217 ] Browser Information Discovery – NosyHistorian collects browser histories from Chrome, Edge, and Firefox (‘NosyHistorian collects browser history from Google Chrome, Microsoft Edge, and Mozilla Firefox.’)
- [T1083 ] File and Directory Discovery – NosyDoor can enumerate directories and list files as part of commands (‘NosyDoor can list files and directories.’)
- [T1082 ] System Information Discovery – NosyDoor collects system metadata (IP, usernames, OS version, process info) for C2 beaconing (‘NosyDoor obtains system information as part of C&C beaconing.’)
- [T1056.001 ] Input Capture: Keylogging – NosyLogger captures keystrokes, window titles, and clipboard content (‘NosyLogger logs keystrokes.’)
- [T1125 ] Video Capture – An argument-runner was used to run FFmpeg to capture audio and video on victims (‘LongNosedGoblin has used video recording software, likely FFmpeg, to capture audio and video.’)
- [T1560 ] Archive Collected Data – Collected browser/profile data and keylogs are archived and/or encrypted prior to exfiltration (‘NosyLogger encrypts collected data via AES.’)
- [T1074.001 ] Data Staged: Local Data Staging – NosyLogger stages captured keystrokes to a local temp file before exfiltration decisions (‘NosyLogger stores pressed keys, window names, and clipboard content to a file at a hardcoded path.’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – Downloader components use HTTP(S) to retrieve payloads and interact with services (‘NosyDownloader uses HTTP to download further payload.’)
- [T1105 ] Ingress Tool Transfer – The malware downloads and runs subsequent payloads on victims (‘NosyDoor and NosyDownloader can download and run subsequent payloads.’)
- [T1102.002 ] Web Service: Bidirectional Communication – NosyDoor uses OneDrive and NosyStealer uses Google Docs/Drive for commanding and exfiltration (‘NosyDoor uses Microsoft OneDrive as its C&C server… NosyStealer uses Google Docs… and Google Drive to exfiltrate browser data.’)
- [T1573.001 ] Encrypted Channel: Symmetric Cryptography – Command outputs and payloads are encrypted with AES prior to upload to C2 (‘NosyDoor encrypts C&C command outputs via AES.’)
- [T1573.002 ] Encrypted Channel: Asymmetric Cryptography – NosyDoor encrypts metadata with RSA before sending to OneDrive (‘NosyDoor uses RSA to encrypt metadata that is sent to the C&C server.’)
- [T1567.002 ] Exfiltration Over Web Service: Exfiltration to Cloud Storage – NosyStealer and NosyDoor exfiltrate data to Google Drive and OneDrive respectively (‘NosyStealer exfiltrates browser data to Google Drive.’)
Indicators of Compromise
- [SHA-1 ] File hashes observed for multiple payloads and stages – 4E3F6E9D0F443F4C42974A0551EEE957B498DA3D (History.ini / NosyHistorian), 154A35DD4117DB760699C2092AFB307E94008506 (Registry.plo / NosyDoor dropper), and 32 more hashes.
- [Filename ] Malware and masqueraded filenames used in Group Policy and persistence – History.ini (NosyHistorian disguised as INI), Registry.pol / Registry.plo (NosyDoor dropper masquerading as Registry Policy), and other filenames like SharedReg.dll, log.cached.
- [IP address ] C2 and infrastructure endpoints seen in telemetry – 118.107.234[.]26 (www.sslvpnserver[.]com) used as a NosyDownloader C2, 118.107.234[.]29 (ReverseSocks5) and 4 other IPs used for C2/hosting.
- [Domain ] Domains tied to C2 and hosting – www.threadstub[.]com (103.159.132[.]30) and www.blazenewso[.]com (101.99.88[.]113) observed as NosyDownloader C2s, plus other related domains.
- [PDB path ] Build paths that link components and toolset development – E:CsharpSharpMiscGetBrowserHistoryobjDebugGetBrowserHistory.pdb (NosyHistorian), E:CsharpThomasServerThomasOneDriveobjReleaseOneDrive.pdb (NosyDoor).