Cloud Atlas continues to target organizations in Russia and Belarus using phishing emails that exploit CVE-2018-0802 in Microsoft Office to deliver an HTA which installs a chain of VBScript- and PowerShell-based backdoors (VBShower, VBCloud, PowerShower) and the CloudAtlas implant. The group uses DLL hijacking with legitimate VLC as a loader, cloud services (WebDAV) for C2 and payload distribution, and plugins for file theft and credential/cookie extraction. #CloudAtlas #VBShower
Keypoints
- Initial access is achieved via phishing DOC(X)/RTF attachments exploiting CVE-2018-0802 to download and execute an HTA that drops multiple VBS components.
- The VBShower loader installs multiple backdoors (PowerShower, VBCloud, CloudAtlas) and runs payloads directly in-process, with updated behavior compared to 2024 variants.
- VBCloud uses an RC4 (PRGA) launcher and modular FileGrabber payloads with detailed inclusion/exclusion rules to exfiltrate documents, while PowerShower runs Base64-encoded PowerShell payloads.
- CloudAtlas persists via a DLL hijacking chain using VLC as a loader; the malicious DLL decrypts and loads an AES-256-CBC-encrypted backdoor, which uses WebDAV cloud directories for beacons and payloads.
- Plugins include FileGrabber (steal files with metadata), PasswordStealer (extract browser cookies/passwords via bundled tools), and InfoCollector (process, product, device, drive and command execution data collection).
- Operators create scheduled tasks and registry tweaks for persistence and stealth (e.g., MicrosoftEdgeUpdateTask, MicrosoftAdobeUpdateTaskMachine, off-screen console window positions).
- Observed victims in early 2025 are located in Russia and Belarus across telecommunications, construction, government, and industrial sectors; detailed IOCs (hashes, domains, filenames) are published in the report.
MITRE Techniques
- [T1566.001 ] Phishing: Spearphishing Attachment – used to deliver malicious DOC/RTF attachments: ‘The starting point is typically a phishing email with a malicious DOC(X) attachment.’
- [T1203 ] Exploitation for Client Execution – exploiting Office Equation Editor vulnerability to execute code: ‘exploits an old vulnerability in the Microsoft Office Equation Editor process (CVE-2018-0802) to download and execute malicious code.’
- [T1105 ] Ingress Tool Transfer – downloading additional components and archives from attacker-controlled servers: ‘The script downloads a ZIP archive from the hardcoded URL and unpacks it into the %Public% directory.’
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – PowerShell used to run encoded payloads and backdoor logic: ‘launch the PowerShell interpreter with another script encoded in Base64.’
- [T1059.005 ] Command and Scripting Interpreter: Visual Basic – VBS/HTA components used as primary loader and payload scripts: ‘The malicious HTA file extracts and creates several VBS files on disk that are parts of the VBShower backdoor.’
- [T1053.005 ] Scheduled Task/Job: Scheduled Task – creation of scheduled tasks for persistence and execution: ‘creates a scheduler task named “MicrosoftEdgeUpdateTask” to run the following command line’ and ‘Creates a “MicrosoftAdobeUpdateTaskMachine” scheduler task’.
- [T1574.001 ] Hijack Execution Flow: DLL Search Order Hijacking – DLL hijacking via VLC to load a malicious library which decrypts and runs the backdoor: ‘a DLL hijacking attack, where VLC acts as a loader, and the b.xml file is an encrypted body…’
- [T1567 ] Exfiltration Over Web Service – use of cloud services and WebDAV for C2, beacons, payload retrieval and data exfiltration: ‘the backdoor starts interacting with the C2 server, which is a cloud service, via WebDAV.’
- [T1539 ] Steal Web Session Cookie – stealing browser cookies and credentials using a plugin and external utilities: ‘This plugin is used to steal cookies and credentials from browsers.’
- [T1555.003 ] Credentials from Web Browsers – extracting saved browser passwords via bundled scripts/tools (get_browser_pass.py and pytest.dll): ‘get_browser_pass.py to extract saved credentials from browsers… the file “C:ProgramDatapypytest.dll” … used to extract credentials from Yandex Browser.’
- [T1005 ] Data from Local System – file theft via FileGrabber plugins that collect and exfiltrate files and metadata from local disks and network shares: ‘FileGrabber is the most commonly used plugin. As the name suggests, it is designed to steal files from an infected system.’
- [T1057 ] Process Discovery – the malware collects running process information including creation time and command line: ‘The script collects information about running processes, including their creation time, caption, and command line.’
- [T1082 ] System Information Discovery – InfoCollector and other components gather system, product and drive information for reconnaissance: ‘This plugin is used to collect information about the infected system.’
Indicators of Compromise
- [File Hash ] example malicious file hashes referenced in the report – 0D309C25A835BAF3B0C392AC87504D9E (протокол (08.05.2025).doc), E9F60941A7CED1A91643AF9D8B92A36D (VBCloud::Payload (FileGrabber)), and numerous other hashes published in the report.
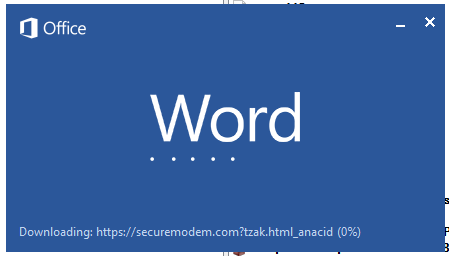
- [Domain ] attacker-controlled infrastructure and template hosting – securemodem[.]com (example URL hxxps://securemodem[.]com?tzak.html_anacid), billet-ru[.]net, and many additional domains listed in the indicators section.
- [Filename / Path ] dropped or used filenames and paths – %LOCALAPPDATA%vlcvlc.exe and %LOCALAPPDATA%vlcchambranle (encrypted payload file), %APPDATA%AdobeAdobeMon.ps1 and upgrade.mds (encrypted VBCloud body).
- [Binary / DLL ] malicious libraries and components observed on hosts – pytest.dll (C:ProgramDatapypytest.dll used by get_browser_pass.py), libvnc_plugin.dll, chambranle (encrypted payload), and system_check.exe referenced in hashes.
Read more: https://securelist.com/cloud-atlas-h1-2025-campaign/118517/