Episode 4 of the Charming Kitten / APT35 leak shows Iranian cyber operations run like a bureaucratic procurement system, with spreadsheets linking domain registrations, VPS rentals, ProtonMail identities, and Cryptomus payments that tie requests, invoices, and live infrastructure together. The same administrative apparatus mapped in the ledgers also supported Moses Staff’s leak-and-defacement campaigns—domains such as moses-staff.io, linked ProtonMail addresses, IP allocations, and bitcoin wallets were documented—exposing operational hygiene failures and reusable supply-chain patterns. #APT35 #MosesStaff
Keypoints
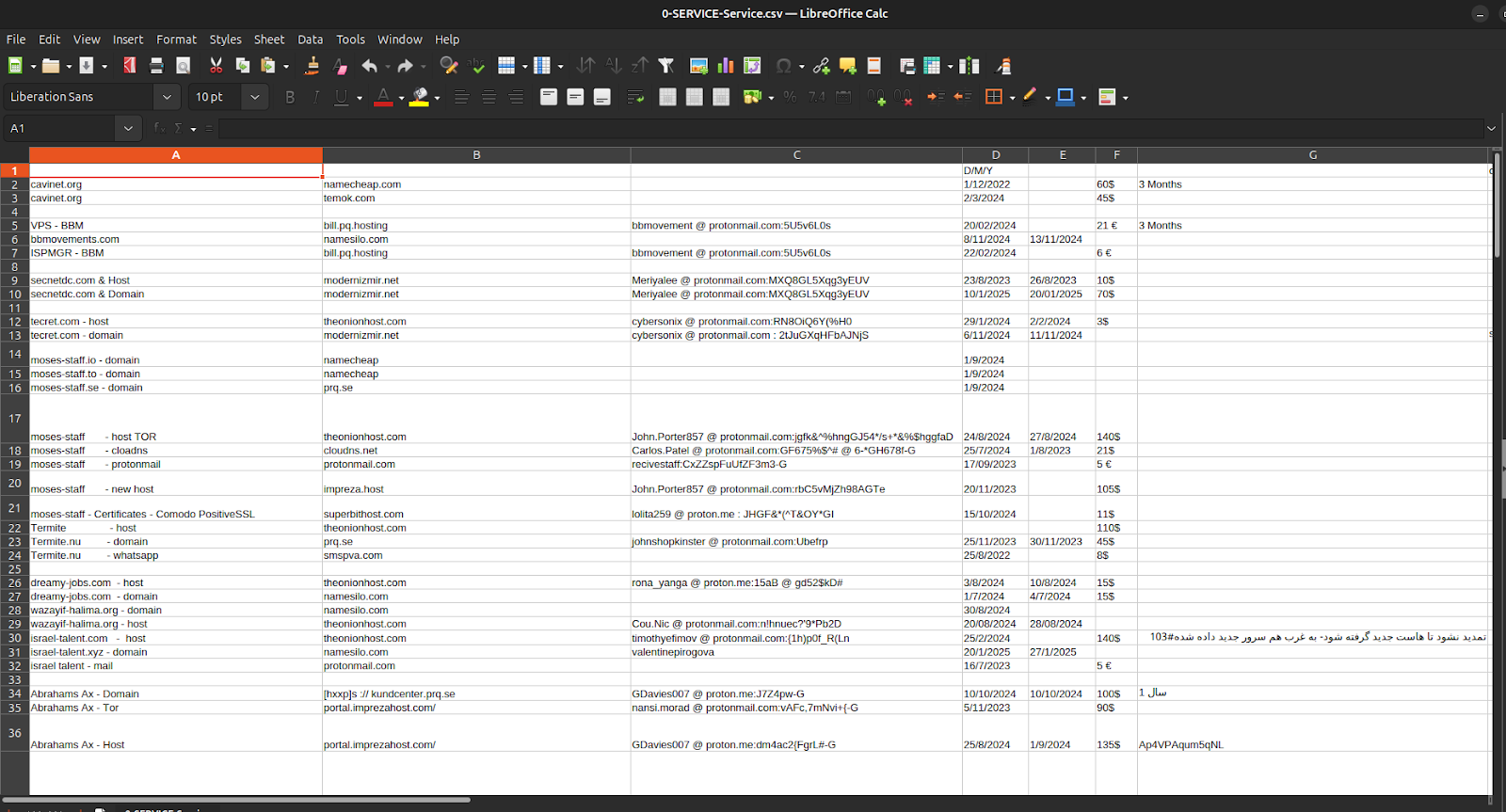
- Episode 4’s leaked spreadsheets expose APT35’s procurement workflow: domains, VPS rentals, credentials, ticket numbers, and crypto receipts are recorded and cross-referenced.
- Operational hygiene lapses left live servers, cleartext credentials, and wallet/payment artifacts exposed for weeks, enabling attribution and forensic linkage.
- The same administrative machine behind Charming Kitten also provisioned Moses Staff infrastructure, collapsing the hacktivist façade into a state-run production line.
- Financial patterns show small, repeated micro-payments (≈€12–€18) funneled through Cryptomus and resellers (EDIS, Impreza) to evade compliance and enable persistence.
- Domain clusters and disposable ProtonMail aliases are single-use, tightly compartmentalized tools that map to specific procurement and campaign timelines.
- The dump produces durable IOCs—domains, bitcoin addresses, IP allocations, ProtonMail accounts, hosting SKUs—that link procurement to deployment and enable disruption points.
MITRE Techniques
- [T1595 ] Active Scanning – Operators stage VPS nodes to probe target systems and deliver phishing infrastructure. [‘Operators stage VPS nodes to probe target systems and deliver phishing infrastructure.’]
- [T1598 ] Phishing for Information – Job-themed domains (e.g., israel-talent.com, dreamy-jobs.com) were used as credential-harvest pages. [‘Domains such as dreamy-jobs.com, israel-talent.com, and wazayif-halima.org are designed to lure specific industries for credential harvesting.’]
- [T1566 ] Phishing – Job-themed credential-harvest pages deployed on low-cost VPS instances acquired through EDIS and Impreza. [‘Job-themed, credential-harvest pages deployed on low-cost VPS nodes purchased through EDIS and Impreza Host.’]
- [T1078 ] Valid Accounts – Harvested credentials were intended to be used for subsequent access attempts and lateral movement. [‘Harvested credentials fed into further access attempts, often timed shortly after domain activation.’]
- [T1204 ] User Execution – Phishing pages and lure documents required victim interaction to capture credentials or deliver payloads. [‘Operators deploy phishing pages requiring victim interaction (login forms, document lures).’]
- [T1098 ] Account Manipulation – Use of harvested credentials to maintain footholds where applicable. [‘Use of harvested credentials to maintain foothold where applicable.’]
- [T1136 ] Create Account – Single-purpose ProtonMail inboxes created for procurement and operational tasks. [‘Single-purpose ProtonMail inboxes created for procurement (operational persistence at the infrastructure layer).’]
- [T1068 ] Exploitation for Privilege Escalation – Implied by references to historical targeting of Microsoft Exchange and Ivanti appliances (not a focus of the dump but part of broader tradecraft). [‘(Not a focus of the dump, but implied in reference to Charming Kitten’s broader history of targeting Microsoft Exchange and Ivanti appliances.)’]
- [T1036 ] Masquerading – Use of aliases and job-themed domains to impersonate legitimate organizations and individuals. [‘Use of aliases that imitate Israeli, Russian, European, and American names; job-themed domains; fake recruitment brands.’]
- [T1070.004 ] File Deletion – Disposable ProtonMail identities and one-time use personas are deleted or abandoned to evade linkage. [‘Use of single-use ProtonMail identities deleted or abandoned immediately after procurement.’]
- [T1112 ] Modify Registry – Referenced as historical Moses Staff post-exploitation activity (not directly in the dump). [‘(Not directly in the dump, but historically used in Moses Staff post-exploitation phases.)’]
- [T1027 ] Obfuscated/Encrypted Files – Use of TOR mirrors, private WHOIS, and encrypted communications to obscure infrastructure and content. [‘TOR mirrors, private WHOIS, and encrypted communication channels.’]
- [T1564.003 ] Hidden Artifacts: Disposable Email Identities – Strict one-time usage of procurement emails to prevent cross-cluster linkage. [‘Strict one-time usage of procurement emails to prevent cross-cluster linkage.’]
- [T1056 ] Input Capture – Credential-harvesting login portals deployed on purchased domains to capture victim credentials. [‘Credential-harvesting login portals deployed on purchased domains.’]
- [T1110 ] Brute Force – Occasional brute-force activity documented in public Moses Staff reporting (supplementary to credential harvesting). [‘Occasional activity against Israeli organizations (documented in public reporting of Moses Staff operations).’]
- [T1087 ] Account Discovery – Scanning and probing to find valid accounts after credential harvesting. [‘Infrastructure scans for valid credentials through job-themed lures.’]
- [T1046 ] Network Service Scanning – EDIS-hosted servers used to probe networks and discover services prior to intrusion. [‘EDIS-hosted servers used to probe Israeli networks prior to planned intrusions.’]
- [T1021 ] Remote Services – Use of harvested credentials to access VPN portals, cloud dashboards, and remote services. [‘Use of harvested valid accounts through VPN portals and cloud dashboards.’]
- [T1530 ] Data from Cloud Storage – Compromise and collection from cloud/email providers and cloud storage. [‘Compromises of cloud/email providers in the civilian tier.’]
- [T1114 ] Email Collection – Phished credentials used to access mailboxes and collect sensitive communications. [‘Phished credentials provide mailbox access enabling data theft.’]
- [T1071 ] Application Layer Protocol – C2 nodes hosted on low-tier VPS servers using HTTP(S) application-layer protocols. [‘C2 nodes hosted on low-tier VPS servers via HTTP(S).’]
- [T1105 ] Ingress Tool Transfer – Payloads and tools staged on purchased domains and KVM BASIC VPS instances. [‘Payloads staged on purchased domains and KVM BASIC VPS instances.’]
- [T1568.002 ] Dynamic DNS – Rapid host rotation and CloudDNS nodes around Moses Staff mirrors for resilience. [‘Operators rotate hosts rapidly; CloudDNS references seen around Moses Staff mirrors.’]
- [T1048 ] Exfiltration Over Alternative Protocol – Use of TOR mirrors and alternative channels for data leakage and anonymity. [‘TOR mirrors used for anonymity during leaks.’]
- [T1567.002 ] Exfiltration to Web Services – Leak sites (moses-staff.io /.se /.to) used to publish stolen data. [‘Leak sites operated under moses-staff.io, .se, .to.’]
- [T1491 ] Defacement / Psychological Operations – Public leak sites and defacements used to intimidate and humiliate Israeli targets. [‘Public leak sites intended to intimidate Israeli institutions.’]
- [T1485 ] Data Destruction – Moses Staff’s destructive toolchain and destructive intrusions historically used against Israeli targets. [‘Moses Staff’s destructive toolchain, already known in historical operations.’]
- [T1585.001 ] Establish Accounts: Email Accounts – Creation of single-use ProtonMail addresses for procurement and registration. [‘Single-use ProtonMail addresses for procurement.’]
- [T1583.003 ] Domain Registration – Clusters of disposable domains purchased and managed for campaigns and credential harvesting. [‘Clusters of domains purchased for credential harvesting and campaign staging.’]
- [T1583.001 ] Acquire Infrastructure: Virtual Private Servers – Routine procurement of VPS instances (EDIS, Impreza, Bulgaria-based sellers) to host phishing/C2. [‘Routine procurement from EDIS, Impreza Host, Bulgarian VPS sellers.’]
- [T1586.002 ] Compromise Accounts: Webmail – Webmail compromises used to harvest credentials and expand access. [‘Credential theft from phishing operations.’]
- [T1586 ] Obfuscation via Payment Providers – Use of Cryptomus and payment fragmentation to obscure transaction provenance. [‘Cryptomus used to anonymize infrastructure transactions.’]
- [T1587 ] Develop Capabilities – Infrastructure provisioning using micro-crypto payments as a repeatable capability. [‘Infrastructure provisioning using micro-crypto payments in a repeatable pattern.’]
- [T1599 ] Network Boundary Bridging – Paying through crypto and using global VPS hosts to evade regional filtering and maintain persistence. [‘By paying through crypto and using global VPS hosting, operators evade regional filtering.’]
Indicators of Compromise
- [Domain ] operational and leak infrastructure – moses-staff.io, israel-talent.com, and 11 more domains (e.g., bbmovements.com, tecret.com, dreamy-jobs.com).
- [Moses Staff Domains ] public leak/broadcast sites – moses-staff.io, moses-staff.se, moses-staff.to.
- [Email Addresses ] procurement and cover identities – [email protected], [email protected], and 50+ ProtonMail identities recorded in ledgers.
- [Bitcoin Wallets ] payment/collection addresses linking invoices to hosting – 1K93styPFkDGsTYNjgqaDN6xWy5NmUDLhh, 3F2KWMSkjFdskQ2gV6pm4NA7JH2dx3jfCA, and ~30+ other wallet addresses listed.
- [IP Addresses / Ranges ] routable infrastructure and VPS allocations – example routable hosts 185.103.130[.]16/30, 185.212.193[.]240/29 and public IPs 128.199.237.132, 212.175.168.58 (plus other /29–/30 allocations).
- [Aliases / Cover Names ] one-time personas tied to procurement – Maja Bosman, Levis Cross, and multiple other single-use cover names.
- [Hosting Providers / AS Identifiers ] providers and infrastructure hosts referenced – EDIS Global (Limassol, Cyprus / ID 57169), Impreza Host, and CloudDNS nodes tied to AS203391 (plus AS16509, AS21340 references).