In November 2025 a targeted spear-phishing campaign used Trend Micro–themed lures and malicious redirects to deliver browser exploits and a multi-stage payload chain against executives across defense, energy, chemical, cybersecurity, and ICT sectors. Trend Vision One detected and stopped the activity early in the kill chain, preventing final payload delivery; the activity is tracked as SHADOW-VOID-042 and shows overlap with campaigns linked to Void Rabisu. #TrendMicro #SHADOW-VOID-042
Keypoints
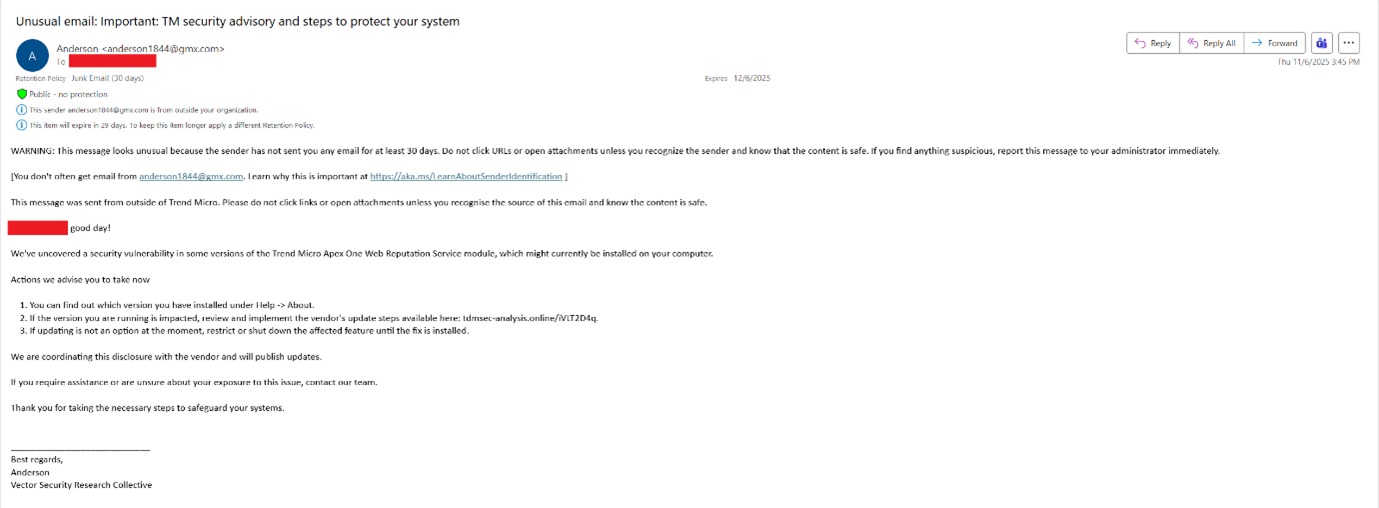
- In November 2025 spear-phishing emails impersonating Trend Micro urged targets to install a fake Apex One update and redirected victims through multiple pages to exploit landing sites.
- Trend Vision One detected and quarantined most malicious emails and blocked landing pages, stopping the infection chain before exploits or final payloads were observed in telemetry.
- The campaign used a multi-stage, machine-tailored loader sequence: JavaScript exploit(s) → shellcode → Stage 2 loader written to C:ProgramDataMicrosoftWindowsSystemProcessHost.exe → additional in-memory stage retrieval.
- One recovered JavaScript contained an exploit for CVE-2018-6065 (Chrome); two other exploit scripts were not retrieved and may have targeted selected victims with more recent zero-days.
- Shellcode generated a unique machine ID, encrypted it with AES-CBC, sent it to C2 via an HTTPS “get_module_hello” request, and received a custom encrypted binary for the target system.
- Due to similarities in infrastructure and TTPs, Trend links the November campaign with an October 2025 campaign and is tracking both under temporary intrusion set SHADOW-VOID-042 while further evidence is collected regarding Void Rabisu attribution.
MITRE Techniques
- [T1566 ] Spearphishing Link – Attackers sent tailored spear-phishing emails with Trend-themed lures containing links to malicious landing pages (‘spear-phishing emails featuring a Trend Micro-themed social engineering lure were sent to various industry verticals’).
- [T1189 ] Drive-by Compromise – Clicking the malicious link redirected targets multiple times and landed them on exploit pages impersonating services (‘After clicking on the link, the target gets redirected multiple times and ends on an HTML page impersonating CloudFlare’).
- [T1203 ] Exploitation for Client Execution – JavaScript on the landing page exploited a Chrome vulnerability (CVE-2018-6065) to achieve code execution in the browser (‘It contains code exploiting Chrome vulnerability CVE-2018-6065’).
- [T1105 ] Ingress Tool Transfer – The C2 responded with an encrypted binary that was decrypted and written to disk at a hardcoded path (Stage 2 was written to C:ProgramDataMicrosoftWindowsSystemProcessHost.exe) (‘The C&C server answers with an encrypted binary that is decrypted and written to hardcoded filepath C:ProgramDataMicrosoftWindowsSystemProcessHost.exe’).
- [T1071 ] Application Layer Protocol – C2 communication used HTTPS to send the encrypted machine fingerprint and receive the encrypted binary (‘sent to a first C&C server through an HTTPS request starting with “get_module_hello”‘).
- [T1053 ] Scheduled Task/Job – Persistence was established by creating a scheduled task to launch the Stage 2 executable at boot with SYSTEM privileges (‘A scheduled task is then created to launch such process with four arguments at every boot with SYSTEM privileges’).
- [T1055 ] Process Injection – A retrieved file was scanned for ‘MZ’/’PE’ headers and then loaded into memory and executed, indicating in-memory loading/injection (‘searches for “MZ” and “PE” headers in the retrieved file, loads it in memory, and jumps to its entry point’).
- [T1036 ] Masquerading/Impersonation – The campaign used a decoy website (TDMSEC) that mimicked Trend Micro’s corporate style to deceive targets (‘the look and feel of this website mimics the corporate style of Trend’s website to a certain extent’).
- [T1573 ] Encrypted Channel – The implant encrypted a generated unique ID with an 8-byte AES-CBC key before sending to C2, and the C2 returned an encrypted binary (‘Such unique ID is encrypted with a randomly generated 8-byte AES CBC encryption key’).
Indicators of Compromise
- [CVE ] JavaScript exploit – CVE-2018-6065 (Chrome exploit recovered in one JS file), and references to additional, unrecovered zero-day exploit scripts.
- [File path / filename ] Stage 2 loader – C:ProgramDataMicrosoftWindowsSystemProcessHost.exe (written by C2 as the customized Stage 2 binary).
- [HTTP request pattern ] C2 communication – HTTPS request beginning with “get_module_hello” used to send encrypted machine ID and retrieve encrypted binaries; C2 responses included an encrypted binary and, in one case, a 404 response for the next stage.
- [Domains / landing pages ] Decoy and impersonation hosts – a CloudFlare-impersonating landing page and a decoy site for “TDMSEC” that mimicked Trend Micro’s corporate style (used as fallback decoy when exploitation failed).
- [Malicious files ] Exploit and loader artifacts – a JavaScript exploit file containing CVE-2018-6065 exploit and two other JavaScript files (not retrieved) referenced as loaded by the landing page.
- [Email subject lines ] Phishing lure examples – “Ensure Browser Security: Address Critical Vulnerabilities” and HR-themed subjects like “Anonymous Concern About Workplace Environment” used in related October/November lures.
Read more: https://www.trendmicro.com/en_us/research/25/l/SHADOW-VOID-042.html