The article describes a critical CentreStack/Triofox vulnerability where a static, predictable machine key allowed attackers to decrypt and forge encrypted access tickets to retrieve sensitive files like web.config. Huntress observed exploitation attempts (CVE-2025-11371) from IP 147.124.216[.]205 and recommends immediate patching to version 16.12.10420.56791 and rotation of the machineKey. #Gladinet #CentreStack
Keypoints
- CentreStack/Triofox use a custom HTTP handler filesvr.dn that accepts an encrypted “Access Ticket” via the t query parameter to authorize file downloads.
- System encryption keys are derived from two static 100‑byte strings returned by GladCtrl64.dll, making the AES key and IV constant across restarts.
- Attackers who obtain the static keys can decrypt existing tickets or encrypt new ones to impersonate users and access arbitrary files (e.g., web.config).
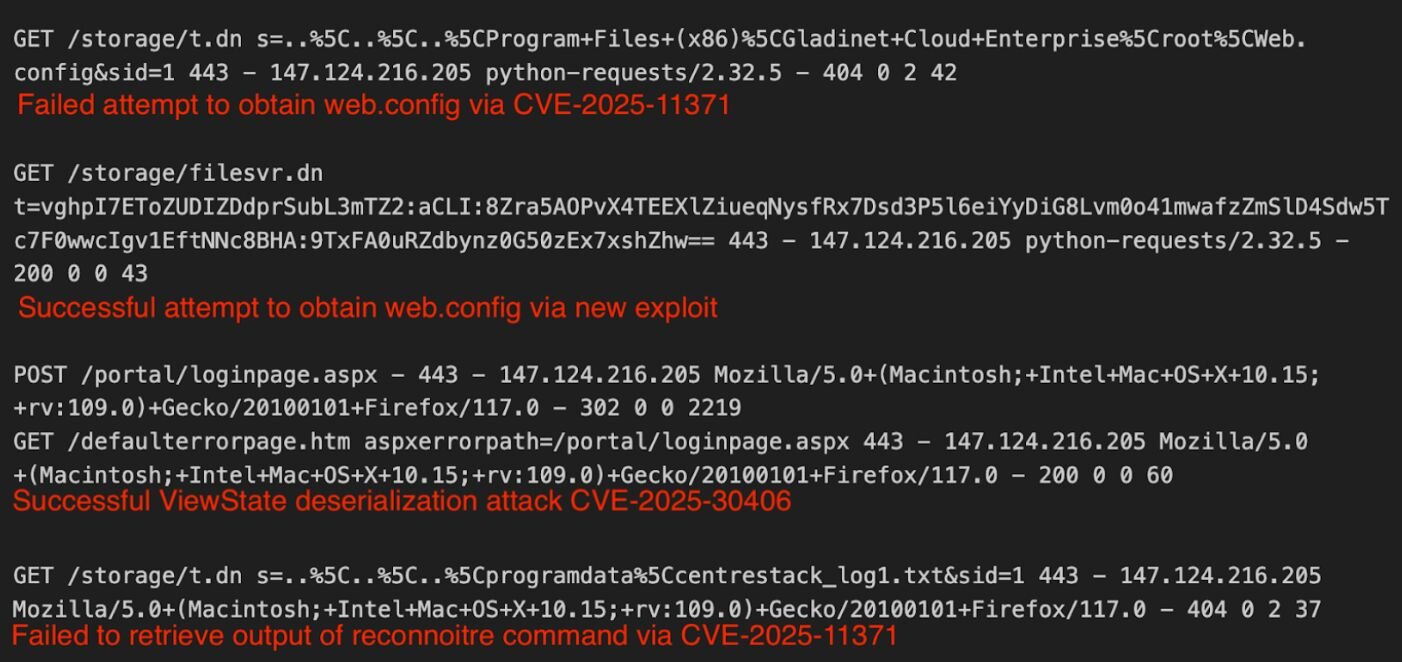
- Huntress decrypted example tickets showing retrieval of C:Program Files (x86)Gladinet Cloud Enterpriserootweb.config and observed the attacker set a timestamp year of 9999 to create non‑expiring tickets.
- Once the web.config (machineKey) was obtained, the actor attempted a ViewState deserialization attack but the payload execution output was not successfully retrieved.
- Gladinet released a security update (build 16.12.10420.56791 on Nov 29); customers are advised to update immediately and rotate machineKey, and Huntress is monitoring related activity.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Exploited CentreStack’s filesvr.dn handler to retrieve sensitive configuration (web.config) and machine keys (‘the threat actor … attempted to use the exploit (CVE-2025-11371) followed by the new exploit to obtain the web.config file containing the machine key.’)
- [T1552.001 ] Credentials in Files – Retrieved machine keys stored in the application’s web.config which can be used to craft or decrypt tickets (‘C:Program Files (x86)Gladinet Cloud Enterpriserootweb.config’ and ‘the attacker was able to obtain the keys, they performed a viewstate deserialization attack’)
- [T1078 ] Valid Accounts – Forged or provided Username and Password fields in the decrypted ticket to initialize an impersonation context and access the file system as that user (‘it initializes an Impersonation context using the Username and Password from the ticket. If valid credentials are provided, the server accesses the file system as that specific user.’)
- [T1203 ] Exploitation for Client Execution – Leveraged ViewState deserialization (using keys from web.config) to attempt remote code execution following retrieval of the machineKey (‘They can be leveraged to abuse the ASPX ViewState … The machine keys open the door for a very standard and well-researched attack technique with ViewState deserialization.’)
Indicators of Compromise
- [URL/Request ] Encrypted GET requests to the filesvr.dn handler used to request web.config and other files – /storage/filesvr.dn?t=vghpI7EToZUDIZDdprSubL3mTZ2, /storage/filesvr.dn?t=vghpI7EToZUDIZDdprSubL3mTZ2:aCLI:8Zra5AOPvX4TEEXlZiueqNysfRx7Dsd3P5l6eiYyDiG8Lvm0o41m:ZDplEYEsO5ksZajiXcsumkDyUgpV5VLxL%7C372varAu (and other similar ticket strings)
- [Token/String ] Encrypted ticket identifier component (useful for log scanning) – vghpI7EToZUDIZDdprSubL3mTZ2 (recommended as the most reliable substring to search for)
- [IP Address ] Observed attacker source IP – 147.124.216[.]205 (observed in exploitation attempts)
- [File Path / Filename ] Targeted configuration file and key location on affected servers – C:Program Files (x86)Gladinet Cloud Enterpriserootweb.config (contains machineKey)
- [Software Version ] Affected/mitigated build identifier – CentreStack/Triofox build 16.12.10420.56791 (update released Nov 29)