Threat actors are exploiting NoteGPT to host malicious files and lure recipients with OneDrive-branded phishing emails that redirect users to credential-harvesting pages. The campaign spoofs a trusted sender and uses a NoteGPT link that ultimately leads to a fake Microsoft login (arc[.]stylized[.]it[.]com) to capture professional credentials. #NoteGPT #OneDrive
Keypoints
- Cofense Phishing Defense Center identified a phishing campaign that leverages NoteGPT and Microsoft branding to steal credentials.
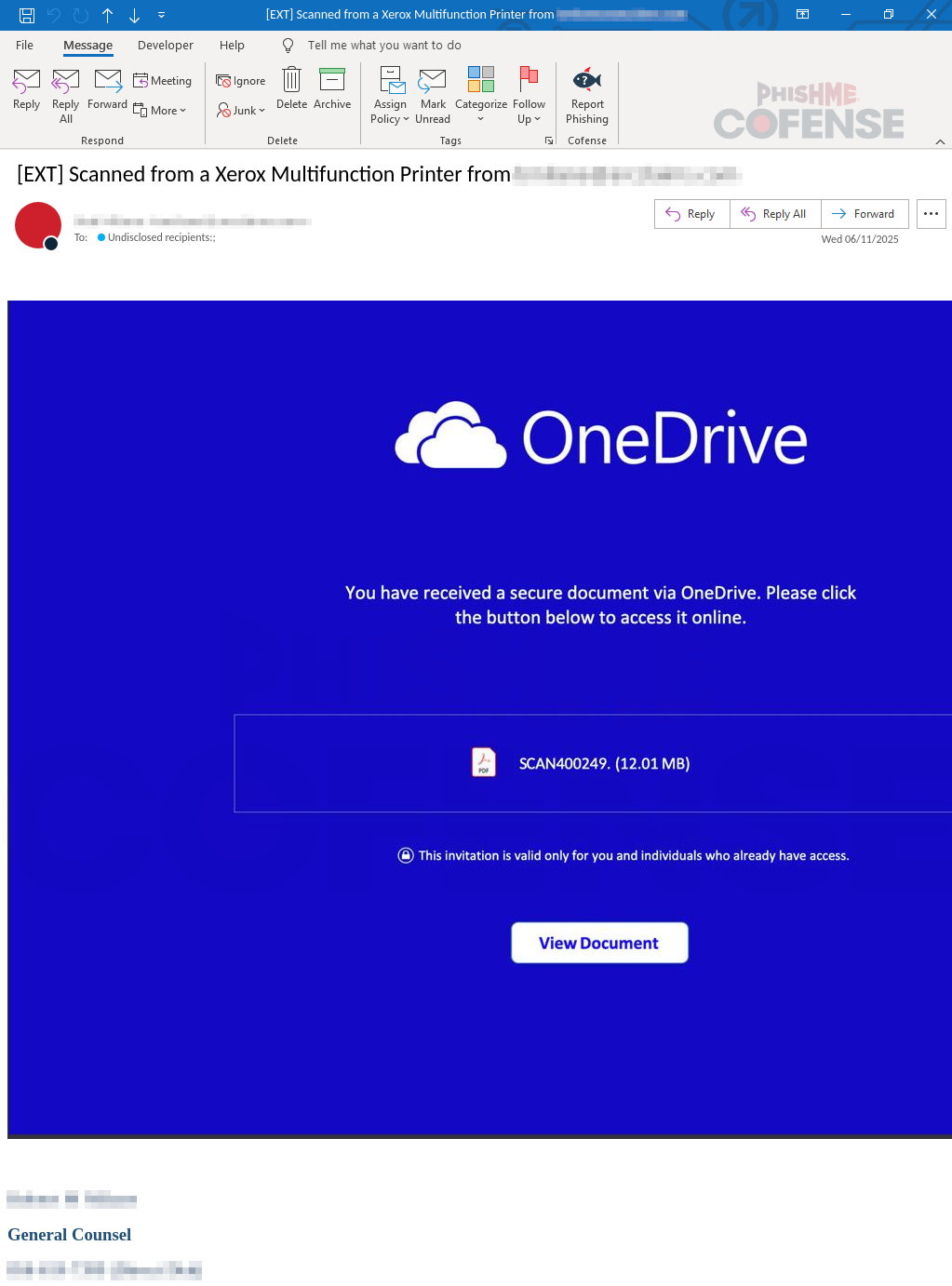
- Emails impersonate a company General Counsel and claim a “secured document” was shared via OneDrive to build trust.
- Clicking “View Document” redirects victims to a NoteGPT page that hosts the malicious content instead of a OneDrive file.
- The NoteGPT page contains a “Get your files here” button that forwards users to a fake Microsoft login designed to harvest credentials.
- The final phishing URL observed is arc[.]stylized[.]it[.]com, a clear indicator of a malicious site masquerading as Microsoft.
- Attackers exploit the legitimacy of NoteGPT to bypass domain blocks and lower user suspicion; Cofense recommends verifying senders and links and offers managed phishing detection and response services.
MITRE Techniques
- [T1566.002 ] Spearphishing Link – Use of deceptive email with a link that redirects to NoteGPT and then to a credential harvesting page; ‘The Cofense Phishing Defense Center (PDC) recently identified a new phishing campaign utilizing NoteGPT and Microsoft branding.’
- [T1204.002 ] User Execution: Malicious Link – Victims are induced to click a “View Document” button which triggers the redirect chain; ‘When a user clicks “View Document,” they are unexpectedly redirected to a NoteGPT page instead of a OneDrive document.’
- [T1078 ] Valid Accounts – Attackers aim to obtain professional credentials via a fake login to later use legitimate account access; ‘The goal? To steal a recipient’s professional credentials by just clicking the button from the received email.’
Indicators of Compromise
- [Domain ] Malicious redirect and hosting – arc[.]stylized[.]it[.]com (malicious phishing login URL), NoteGPT (platform used to host and serve the malicious note)
- [Email Address ] Spoofed sender used to appear legitimate – spoofed address mimicking a company General Counsel (no specific address provided)
Read more: https://cofense.com/blog/phishers-get-creative-the-notegpt-twist-you-didn-t-see-coming