Two compromised email accounts belonging to Italian public administration users have been used since December 8 to send mass phishing messages with malicious PDF attachments that redirect victims to a Figma page requesting login. The campaign likely aims to harvest real email identities or stage a second-phase follow-up using trust in a legitimate service. #CERT-AGID #Figma
Keypoints
- Campaign active since December 8, abusing compromised email accounts from the Italian Public Administration to send mass messages to other PA users.
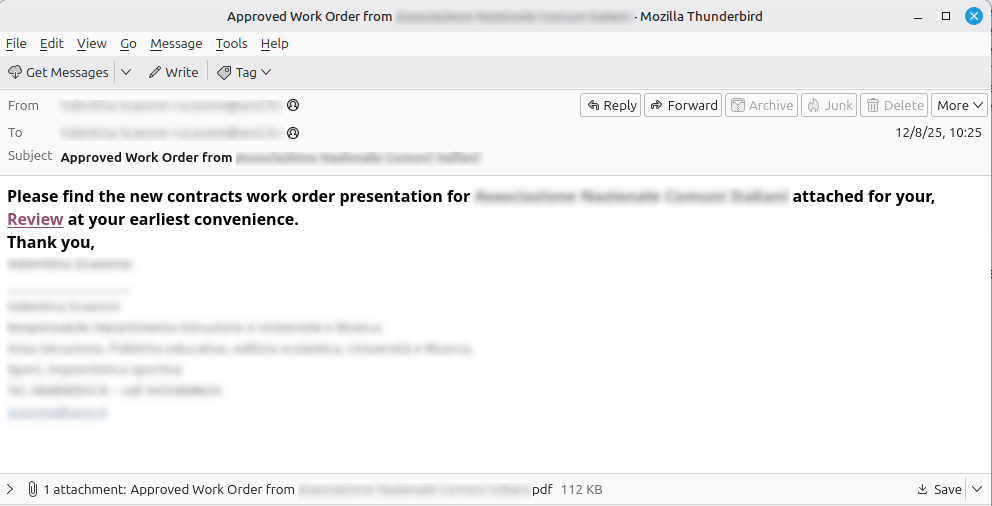
- Emails are sent with recipients hidden in BCC and typically contain English subject/body (occasionally Italian) and a malicious PDF attachment prompting action.
- Opening the PDF displays a notification with a “REVIEW DOCUMENTS” button that directs victims to a real Figma page asking for email or Google authentication.
- After login on Figma, the user is placed “pending approval”; the campaign’s next steps are not confirmed but may include credential harvesting, delivery of additional malicious content, or tailored follow-up emails.
- Two PA administrations have confirmed compromised accounts so far; additional public administrations may be affected.
- CERT-AGID notified affected administrations, reported malicious links via Figma’s “Report Abuse,” and distributed PDF hashes to accredited organizations via the Flusso IoC.
- The CERT-AGID has shared IoCs with accredited organizations and provided a downloadable IoC package for further details.
MITRE Techniques
- [T1078 ] Valid Accounts – The campaign “exploits compromised email accounts of users belonging to the Public Administration” (‘the malicious campaign that exploits compromised email accounts of users belonging to the Public Administration’).
- [T1566.001 ] Phishing: Spearphishing Attachment – Attackers send emails with a PDF attachment that prompts the user to click (“On opening the PDF the victim sees… invites to click the button “REVIEW DOCUMENTS””) to initiate the phishing flow.
- [T1566.003 ] Phishing: Spearphishing via Service – The PDF redirects victims to a legitimate Figma page to request authentication, leveraging a legitimate cloud service to phish credentials (“Clicking the button in the PDF, the user is directed to a real Figma page, where they are asked to sign in with an email account or Google authentication”).
- [T1204.001 ] User Execution: Malicious File – The attack requires the user to open a malicious PDF, which triggers the subsequent redirection and social-engineering steps (“On opening the PDF the victim visualizes a screen announcing receipt of a new document and invites clicking ‘REVIEW DOCUMENTS’”).
- [T1204.002 ] User Execution: Malicious Link – The victim must click a link/button inside the PDF that leads to the Figma page (“invites to click the button ‘REVIEW DOCUMENTS’”).
- [T1589 ] Gather Victim Identity Information – The actor may be collecting emailed identities and full names from users who request access to the Figma file (“the attacker could simply want to collect information on users who request access to the Figma file, thus obtaining real email addresses and full names”).
Indicators of Compromise
- [Domain ] Legitimate service abused as phishing landing page – figma.com (campaign redirects victims to a real Figma page), and malicious link reports submitted via Figma “Report Abuse” (download IoC link referenced).
- [File hashes ] Malicious PDF attachments – PDF hashes were distributed by CERT-AGID to accredited PA via the Flusso IoC (specific hashes not listed in the public article; IoC package available for accredited organizations).
- [Email addresses ] Compromised sender accounts – two public administration email accounts confirmed compromised (specific addresses not published), and other PA accounts possibly affected.
- [File names ] Malicious PDF attachments prompting “REVIEW DOCUMENTS” – unnamed PDF attachments used in the campaign (exact filenames not published) and related PDF artifacts referenced in the IoC feed.