Since January 2025, DomainTools Investigations tracked a long‑running super cluster of malware delivery domains (active since June 2023) and observed ~1,900 additional suspected domains from May–November 2025, bringing the cluster to roughly 5,000 domains characterized by spoofed software download sites targeting Chinese‑language users. The report also demonstrates an experimental agentic AI analysis pipeline that processed ~2,000 malware delivery websites in ~10 hours (1–10 minutes per domain) and highlights technical tradecraft such as anti‑automation JavaScript, multiple packers (VMProtect/UPX), certificate pinning, and numerous IOCs. #Kuailian #WhatsApp
Keypoints
- Researchers identified ~1,900 additional malware delivery domains from May–November 2025, adding to a super cluster active since 2023 and bringing the overall cluster estimate to ~5,000 domains.
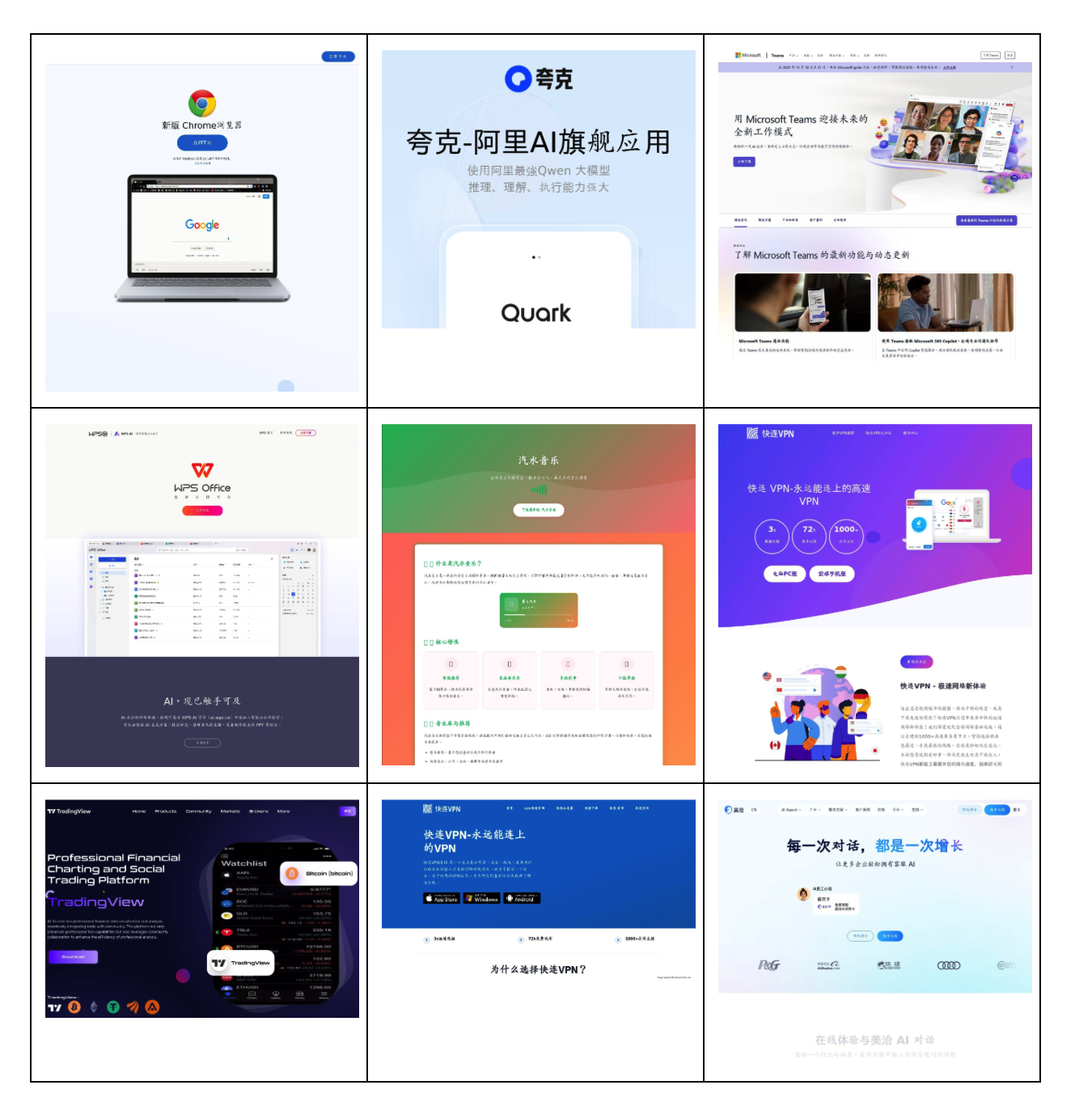
- The threat actor persistently spoofs popular software download pages (e.g., WhatsApp, Kuailian, Google, WPS, Chrome, imToken, AICoin) primarily targeting Chinese‑language users worldwide.
- Infrastructure evolved from consolidated hosting and a single registrar dominance to diversified, fragmented clusters with localized registrars (majority Chinese), randomized domain names, and shorter domain lifespans.
- Technical evasions observed include enhanced anti‑automation JavaScript (20+ signatures), multiple packers (VMProtect, ASPack, ASProtect, MPRESS, UPX), and certificate pinning on Cloudflare‑hosted domains.
- Binary analysis recovered ~47 unique binary samples and ~116 distinct executables/archives across processed domains; large downloads (100–250 MB) and packed droppers impeded traditional scanning workflows.
- An agentic AI architecture (orchestrator + specialized subagents) produced a ~10x throughput improvement over manual analysis, processing ~2,000 domains in ~10 hours with YARA rule generation and multi‑tool binary analysis integration.
MITRE Techniques
- [T1189 ] Drive‑by Compromise – Malware delivered through spoofed software download websites. Quote: ‘spoofing common software download websites as lures to deliver trojans and credential stealers.’
- [T1036 ] Masquerading – Domains and site content mimic legitimate vendor/download pages to appear authentic. Quote: ‘mimicking legitimate software download sites.’
- [T1105 ] Ingress Tool Transfer – Binaries and installers are hosted for direct download (HTTP URLs delivering executables and APKs). Quote: ‘serves an APK file that is packed and suspected of sideloading stealer malware.’
- [T1204 ] User Execution – Relies on users downloading and running installers/APKs supplied by spoofed sites. Quote: ‘spoofing common software download websites as lures to deliver trojans and credential stealers.’
- [T1027 ] Obfuscated Files or Information – Use of packers and protectors to hinder analysis (VMProtect, UPX, ASPack, ASProtect, MPRESS). Quote: ‘protected files with VMPprotect or UPX and other packers of suspected droppers.’
- [T1059.007 ] Command and Scripting Interpreter: JavaScript – Anti‑automation and evasive JavaScript on pages to detect and block automated analysis. Quote: ‘Enhanced anti-automation JavaScript (20+ unique evasion signatures).’
- [T1583 ] Acquire Infrastructure – Bulk domain registrations, registrar diversification, and use of privacy protection services to build and maintain the delivery infrastructure. Quote: ‘Registrar diversification: 8 unique registrars vs 3 previously’ and ‘shorter domain active lifespans (average 30 days vs 60 days).’
Indicators of Compromise
- [Registrant Email ] domain registration contacts used by the cluster – 1204504046[@]qq.com, 18589929790[@]163.com, and many more registrant emails.
- [SHA256 File Hash ] analyzed binary sample – 472d238bd8da7436d93e78a94c918e10961663be784e9985684179aaa7894e2b8ddb67e0b243814c4e2062182043e11e07c7d1b9a1f60ad58fd129e74e12ffc99 (one example hash listed).
- [Download URL ] examples of hosted malicious installers – http[:]//guge-cn[.]com[.]cn/ChromeSetup[.]exe, http[:]//xunlei-pc[.]com[.]cn/XunLeiWebSetup12[.]4[.]7[.]3858xl11[.]exe (multiple other download URLs documented).
- [Domain ] sample spoofed domains used as lures – dk-whatsapp[.]com[.]cn, kuailianwq[.]com[.]cn, and many additional domains across campaigns (total cluster ~5,000 domains).
- [Tracker IDs/Analytics ] embedded analytics and trackers observed on sites – Google Analytics codes (e.g., G-37ZJLQFQXW), GTM containers (e.g., GTM-5P954SP), and tracking endpoint https://tongji[.]mc52[.]com/.
- [File Names ] common delivered filenames seen in downloads – ChromeSetup.exe, SodaMusic-v2.7.0-official-win32_x64.exe, and other installer/archive filenames.
Read more: https://dti.domaintools.com/chinese-malware-delivery-domains-part-iv/