Seqrite Labs identified Operation FrostBeacon, a multi-cluster campaign delivering Cobalt Strike beacons to Russian B2B organizations via malicious archives and weaponized Word documents. The attackers use LNK/HTA and CVE-2017-0199/CVE-2017-11882 chains with multi-layered obfuscated PowerShell loaders and Russian-controlled C2 infrastructure to execute in-memory shellcode. #OperationFrostBeacon #CobaltStrike
Keypoints
- Operation FrostBeacon targets B2B enterprises in the Russian Federation, focusing on finance and legal departments responsible for payments, contracts, and reconciliation.
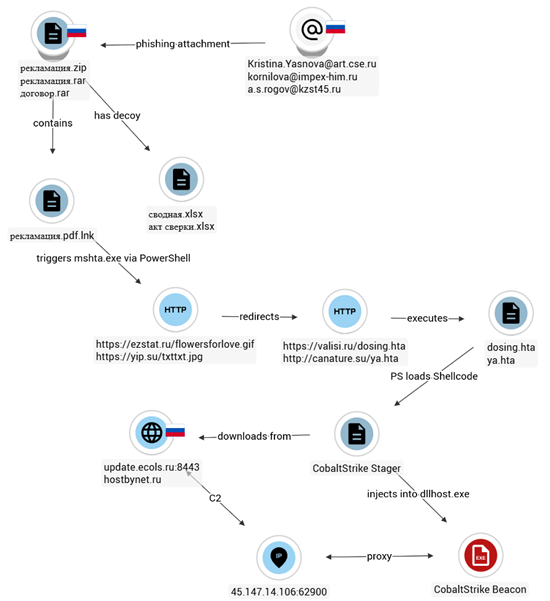
- The campaign uses two parallel infection clusters: a ZIP/LNK archive path that triggers mshta/HTA loaders, and a DOCX path that exploits CVE-2017-0199 (often chained to CVE-2017-11882).
- Both clusters converge on a remote HTA that reconstructs a gzip/Base64 PowerShell loader which decodes, XOR-decrypts, and executes Cobalt Strike shellcode entirely in memory.
- Deployed Cobalt Strike beacons use HTTPS stagers, a customized malleable C2 profile, proxy credentials, and process injection (NtMapViewOfSection) to blend with legitimate web traffic and evade detection.
- Attack infrastructure includes numerous Russian-registered domains (e.g., update.ecols.ru, ezstat.ru, valisi.ru) and proxy IPs (45.147.14.106:62900, 45.145.91.164:64830) used as C2/redirectors.
- IOCs include multiple HTA, RTF, DOCX, LNK filenames and dozens of file hashes and URLs; the activity is assessed as financially motivated and linked to a Russian-speaking cybercrime actor.
MITRE Techniques
- [T1566.001 ] Spearphishing Attachment – Phishing emails delivered ZIP and DOCX attachments as the initial access vector. (‘The infection chain begins with the distribution of an archive via phishing email attachment.’)
- [T1204.002 ] User Execution: Malicious File – Victim interaction (double-click) on LNK/DOCX files triggers the malicious chain. (‘When the user double-clicks the file, it triggers the following command via cmd.exe’).
- [T1221 ] Template Injection – DOCX files reference external templates to load remote HTA payloads via CVE-2017-0199. (‘the word/settings.xml.rels file contained an attachedTemplate relationship referencing an external template hosted at aquacomplect[.]ru’)
- [T1059.003 ] Command & Scripting Interpreter: PowerShell – Obfuscated PowerShell is used to fetch, decode, xor-decrypt, and execute shellcode in memory. (‘the HTA reconstructs multiple Base64-encoded blocks into a gzip-compressed PowerShell script’)
- [T1027 ] Obfuscated/Encrypted Files or Information – Multi-layered gzip/Base64 and XOR obfuscation used to hide payloads. (‘three-layer obfuscation sequence… gzip-compressed Base64 string… Base64-encoded blob… performs a byte-wise XOR operation’)
- [T1140 ] Deobfuscate/Decode Files or Information – The loader performs Base64 and gzip decoding and XOR to reveal shellcode. (‘When decoded and decompressed, it yields the second-stage PowerShell script… After decoding, the script performs a byte-wise XOR operation’)
- [T1055 ] Process Injection – Final beacon/stager uses process injection and NtMapViewOfSection for in-memory execution. (‘ProcInject_AllocationMethod’: ‘NtMapViewOfSection’ and process injection uses NtMapViewOfSection’)
- [T1082 ] System Information Discovery – The payload gathers host information as part of discovery activities. (‘The stager configuration… and the disassembly is a Windows x86 shellcode which… dynamically resolves Win32 APIs’)
- [T1016 ] System Network Configuration Discovery – Malware enumerates network configuration to support C2 communications. (‘establishes an HTTP-based command-and-control channel masquerading as normal web traffic’)
- [T1105 ] Ingress Tool Transfer – Secondary payloads and staged beacons are downloaded from remote C2/stager URLs (e.g., update.ecols.ru). (‘This portion represents a Cobalt Strike stager masquerading as a JS CDN download’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – C2 uses HTTPS/HTTP GET/POST with disguised headers and paths resembling jQuery files. (‘Cobalt Strike stager masquerading as a JS CDN download… URL: hxxps://update.ecols.ru/jquery-3.3.1.slim.min.js’)
- [T1090 ] Proxy / Redirector Usage – Attackers use proxies and redirector domains to route traffic and hide C2. (‘Proxy_Config’: ‘hxxp://45.147.14.106:62900’, … multiple Russian-controlled domains configured as command-and-control endpoints’)
Indicators of Compromise
- [File Hash ] example malicious archive and LNK – 7096141a5b480e793e9a890b84ebaee2 (рекламация.zip), 16ae36df5bee92d8c4cae8e17583a2c9 (рекламация.pdf.lnk), and many other hashes (dozens more).
- [File Names ] representative lures and loaders – рекламация.zip, рекламация.pdf.lnk, dosing.hta (remote HTA loader) and other HTA/RTF/DOCX lures.
- [URLs/Trigger URLs ] initial redirectors and HTA hosts – hxxps://ezstat[.]ru/flowersforlove.gif (redirector), hxxps://valisi[.]ru/dosing.hta (HTA payload) and numerous similar trigger URLs.
- [C2 Domains ] stager/beacon endpoints – update.ecols[.]ru (Cobalt Strike stager), incident.zilab[.]ru and ezstat[.]ru, plus 20+ additional Russian-registered domains observed.
- [Proxy IPs ] hard-coded proxy used by beacon – 45.147.14.106:62900 (AS49505 JSC Selectel RU), 45.145.91.164:64830 and related proxy endpoints.
- [Email Addresses ] phishing sender examples – Kristina.Yasnova@art[.]cse[.]ru, a.s.rogov@kzst45[.]ru used in phishing templates.
- [Beacon/Stage Hashes ] Cobalt Strike payload examples – f87227dad7bedf66bf1a1b97aa36bf62 (Cobalt stager/beacon sample), plus several other beacon hashes collected.