MITRE identified nine new threat groups tied to the most abused vulnerabilities from August–October 2025 and researchers compiled IoC lists (originally 126 domains, reduced to 108 suspicious/malicious after analysis) plus 31 IPs and 5 email addresses for deeper investigation. The analysis uncovered pre-malicious domain detections, extensive historical DNS/IP resolutions, and network traffic linking 1,839 potential victim IPs to IoC infrastructure. #AppleJeus #LazarusGroup
Keypoints
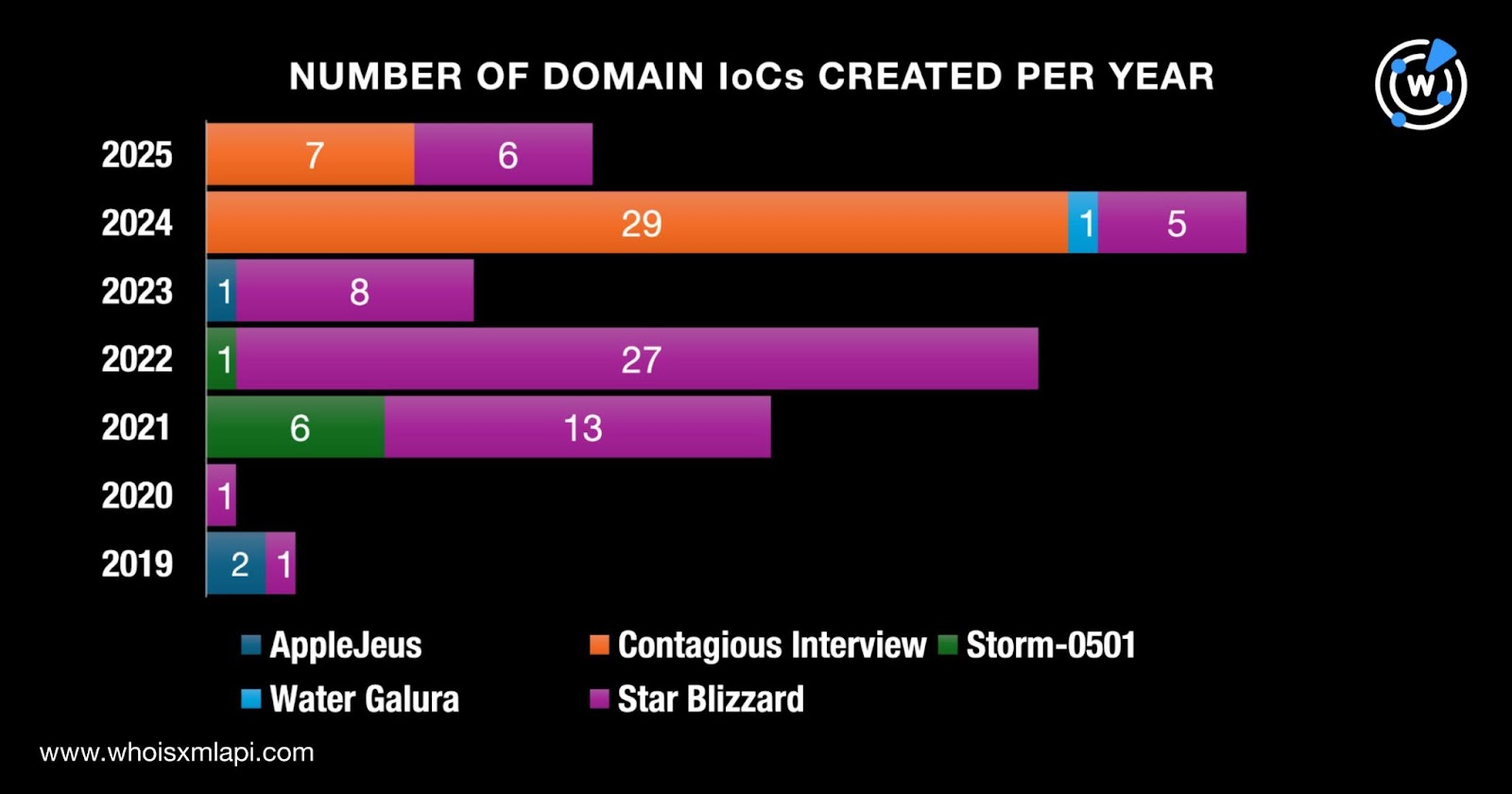
- MITRE named nine new groups: six Enterprise, two Mobile, and one ICS group, with IoC data collected for several (notably AppleJeus, Contagious Interview, Storm-0501, Water Galura, Star Blizzard, MuddyWater, UNC3886, Medusa Group, and Lazarus Group).
- Researchers compiled 126 domain IoCs for five groups but, after WHOIS/Threat Intelligence checks, 108 domains were deemed suspicious or malicious and were the focus of analysis.
- The investigation also analyzed 31 IP-address IoCs and five email-address IoCs; network telemetry showed 1,839 unique potential victim IPs communicating with four IoC IPs between 9 Sep–13 Nov 2025.
- First Watch Malicious Domains feed flagged two Contagious Interview domains as likely malicious 10 days before they were reported as IoCs (complexassess[.]com, intro-crypto-assess[.]com).
- DNS Chronicle and WHOIS history queries revealed extensive historical domain-to-IP and IP-to-domain resolutions (e.g., 97 domains with 2,022 resolutions; 19 IPs with 5,451 resolutions) and domain registrations spanning 2019–2025 across 23 registrars.
- Hunting expanded artifacts: 78 email-connected domains were discovered (11 linked to known attacks), eight additional IPs were found (seven weaponized), and samples of additional artifacts are available for download.
MITRE Techniques
- [T0000 ] None mentioned – ‘The article did not list MITRE technique IDs or names.’
Indicators of Compromise
- [Domain ] Domains analyzed as IoCs across multiple groups – complexassess[.]com, cloud-docs[.]com, and 106 more domains (108 total analyzed)
- [IP address ] IP-address IoCs tied to groups and historical resolutions – 84[.]49[.]242[.]125, 148[.]251[.]204[.]131, and 29 more IP addresses (31 total)
- [Email address ] Email-address IoCs collected for Medusa Group (not active for domain registration) – key[.]medusa[.]serviceteam@protonmail[.]com, MedusaSupport@cock[.]li, and 3 other email addresses (5 total)
Read more: https://circleid.com/posts/dns-spotlight-new-mitre-attck-group-entrants-as-of-october-2025