A critical Remote Code Execution (RCE) vulnerability (CVE-2025-66478) in Next.js App Router arises from an upstream flaw in the React Server Components (RSC) protocol (CVE-2025-55182), allowing unauthenticated attackers to send crafted RSC requests that execute arbitrary code on vulnerable servers. Wazuh can detect exposed systems by identifying vulnerable package versions, monitoring execution via Auditd, and generating alerts to help teams remediate or verify patches. #CVE-2025-66478 #Nextjs
Keypoints
- The vulnerability CVE-2025-66478 (CVSS 10.0) enables remote code execution in Next.js applications using the App Router and affected React RSC protocol implementations.
- The underlying RSC protocol flaw is tracked as CVE-2025-55182 and affects React 19.x and frameworks/plugins that implement RSC (e.g., React Router RSC mode, Vite RSC plugin, Parcel RSC plugin, RedwoodSDK, Waku).
- Affected Next.js versions include 15.x, 16.x, and certain 14.3.0-canary.77+ releases; affected React package versions include 19.0, 19.1.0, 19.1.1, and 19.2.0.
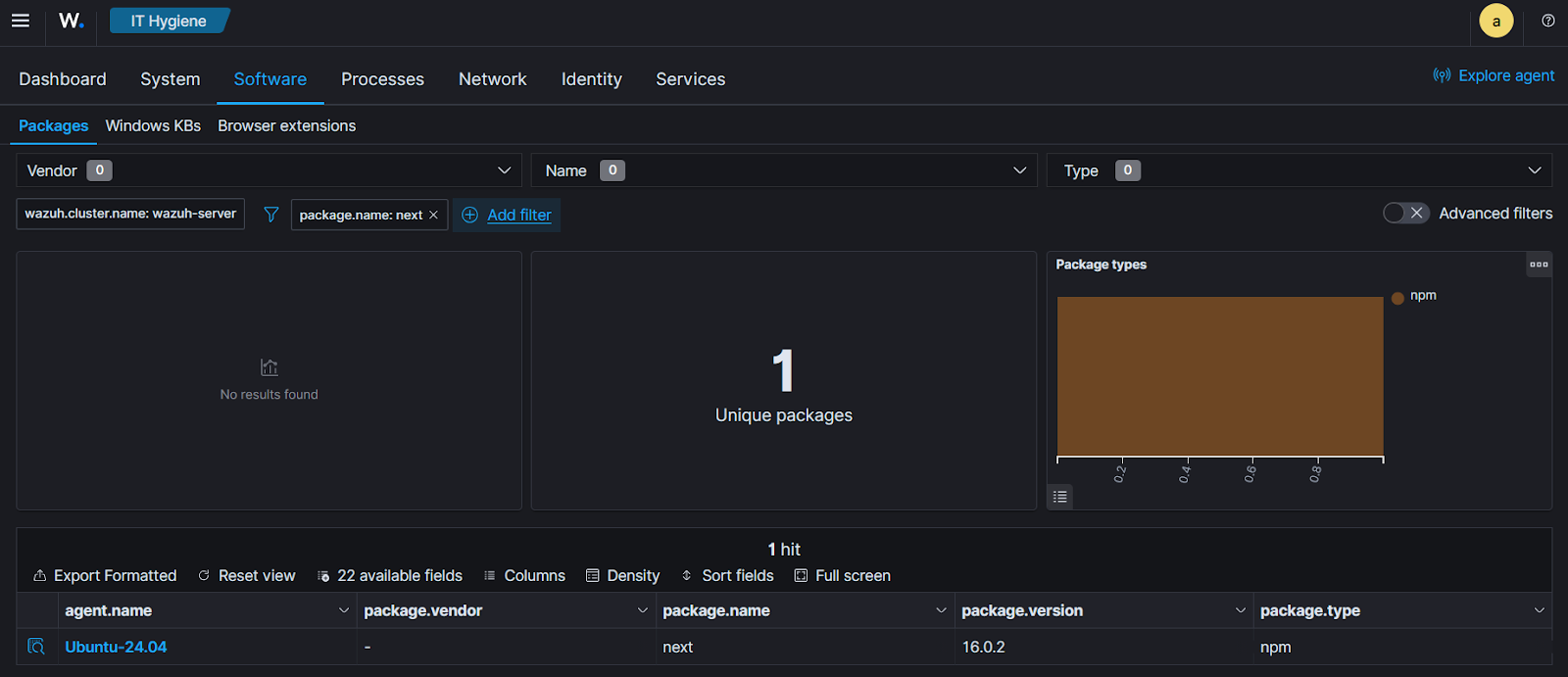
- Wazuh detects exposure by matching installed packages against its CTI feed (CVE references) and uses Syscollector and Vulnerability Detection modules to generate actionable alerts.
- Mitigation requires upgrading Next.js and React to specified patched versions or downgrading from affected canary releases; Wazuh can verify remediation by updating vulnerability status from Active to Solved.
<liA successful exploit allows unauthenticated attackers to run arbitrary commands, read files (demonstrated via PoC reading /etc/exploit), and potentially deploy payloads or move laterally.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – Used when attackers send crafted RSC requests to a vulnerable Next.js application to trigger RCE (‘An attacker who can send crafted, malicious RSC requests to a vulnerable application may execute arbitrary code on the server.’)
- [T1059] Command and Scripting Interpreter – After exploitation, adversaries execute system commands and scripts on the compromised host (e.g., reading /etc/exploit, running ‘uname -a’) (‘…may execute arbitrary code on the server… run commands, deploy payloads…’).
- [T1021] Remote Services – Successful exploitation can enable remote control and lateral movement within the network by granting attackers system-level access (‘…take full control of the system… lateral movement within the network.’)
Indicators of Compromise
- [Vulnerability ID ] referenced CVEs – CVE-2025-66478, CVE-2025-55182
- [Repository / URL ] PoC exploit repository – https://github.com/msanft/CVE-2025-55182
- [File path / filename ] files created or read during exploitation – /etc/exploit (contains exploit confirmation text), /home/vagrant/CVE-2025-55182/test-server
- [Package / Version ] vulnerable software versions detected – next 16.0.2, next 16.0.6, React 19.0 and 19.1.0 (and other 2 affected React versions)
- [Network endpoint ] exploit target address placeholder used in commands – http://:3000 (used with python3 poc.py to execute remote commands)
Read more: https://wazuh.com/blog/detecting-next-js-cve-2025-66478-rce-vulnerability-with-wazuh/