React2Shell (CVE-2025-55182) is a critical unauthenticated remote code execution vulnerability in React Server Components that allows arbitrary server-side code execution via a single crafted HTTP request, with public PoCs and near-100% success rates against default configurations. Sysdig TRT released Falco runtime detection rules and recommends immediate patching to fixed React and Next.js versions while WAF rules and runtime detections are used as temporary mitigations. #React2Shell #CVE202555182
Keypoints
- React2Shell (CVE-2025-55182) is an unauthenticated RCE in the React Server Components (RSC) Flight protocol that results from unsafe deserialization of HTTP payloads.
- Affected packages include react-server-dom-parcel, react-server-dom-turbopack, and react-server-dom-webpack in versions 19.0.0, 19.1.0, 19.1.1, and 19.2.0, and many frameworks that support RSC (e.g., Next.js, React Router, Vite RSC).
- Next.js is tracked as CVE-2025-66478 for downstream exposure; standard create-next-app production builds are vulnerable by default.
- Exploitation enables unauthenticated arbitrary code execution leading to data exfiltration, persistence (backdoors/web shells), lateral movement, and malware/ransomware deployment.
- Public proof-of-concept exploits exist and researchers report almost 100% success against default configurations, making mass exploitation likely.
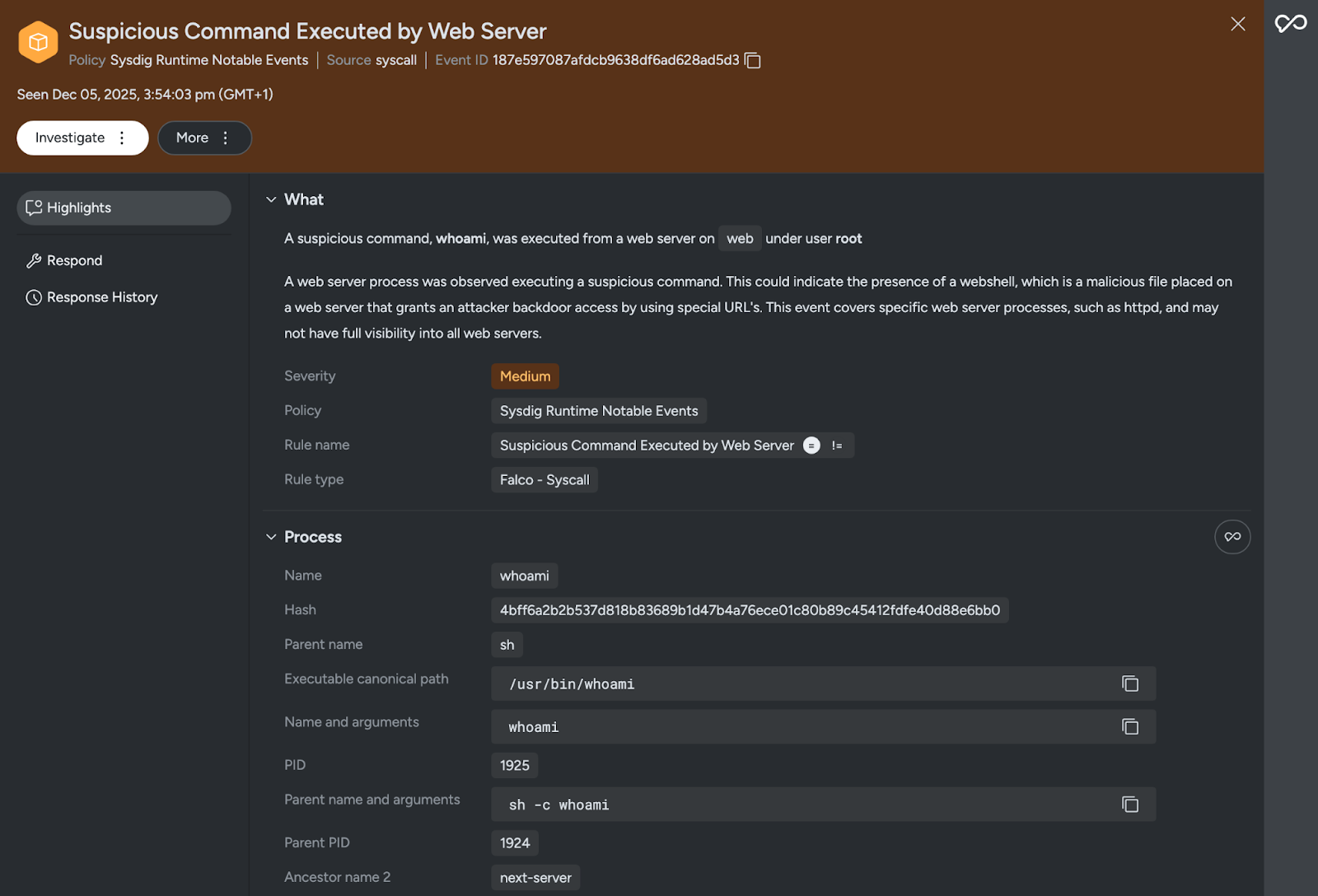
- Sysdig TRT published a Falco rule (“Detecting React2Shell Remote Code Execution”) and reinforced “Suspicious Command Executed by Web Server” detections; WAF providers (Cloudflare, Google Cloud Armor, Vercel, Firebase) have deployed temporary protections.
- Patching is the only complete remediation: update RSC packages to 19.0.1/19.1.2/19.2.1 and Next.js to the listed fixed releases; deploy runtime detections and WAFs until patched.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Exploited the public-facing React Server Components via a crafted HTTP request to achieve unauthenticated RCE. Quote relevant content using bracket (‘allows for potentially malicious code execution with a single crafted HTTP request.’)
- [T1059 ] Command and Scripting Interpreter – Attackers execute arbitrary shell commands on the compromised server (detected by Falco rules that look for spawned minimal unix commands). Quote relevant content using bracket (‘suspicious commands spawned by web servers, raising alerts for Remote Command Execution’)
- [T1105 ] Ingress Tool Transfer – After gaining execution, attackers can deploy backdoors or web shells and transfer additional tools to the server. Quote relevant content using bracket (‘Establish persistence by deploying backdoors or web shells.’)
- [T1021 ] Remote Services – Attackers can move laterally by pivoting to internal systems following initial compromise. Quote relevant content using bracket (‘Move laterally by pivoting to internal systems.’)
- [T1041 ] Exfiltration Over C2 Channel – Compromised servers can be used to exfiltrate secrets, credentials, and user information post-exploitation. Quote relevant content using bracket (‘Exfiltrate data by accessing secrets, credentials, and user information.’)
- [T1505 ] Server Software Component – Attackers can leverage the server application to persist (e.g., web shells) and modify server-side components. Quote relevant content using bracket (‘Establish persistence by deploying backdoors or web shells.’)
Indicators of Compromise
- [Package/Version] vulnerable RSC packages and versions – react-server-dom-parcel 19.0.0, react-server-dom-webpack 19.2.0 (and react-server-dom-turbopack 19.1.0/19.1.1), plus other affected 19.x releases.
- [Application/Framework version] vulnerable framework releases – Next.js 15.0.4 through 16.0.6 and canaries from 14.3.0-canary.77 (and multiple patched Next.js releases listed for remediation).
- [Proof-of-concept payload] exploit trigger pattern used by scanner – ‘[“$1:a:a”]’ sent against an empty object to cause vulnerable servers to return a 500 with E{“digest”: …} (used by Assetnote to differentiate vulnerable vs patched hosts).
- [Detection/Rule name] runtime detection identifiers – Falco rule ‘Detecting React2Shell Remote Code Execution’ and Sysdig rules ‘Suspicious Command Executed by Web Server’, ‘Reverse Shell Detected’ (used to flag exploitation activity).
Read more: https://www.sysdig.com/blog/detecting-react2shell