Researchers at Socket discovered two malicious Go packages that typosquat popular UUID libraries and exfiltrate data to the pastebin-style service dpaste. The packages (github.com/bpoorman/uuid and github.com/bpoorman/uid) preserve expected UUID behavior while adding a hidden Valid function that encrypts caller-supplied data and uploads it with a hardcoded dpaste API token. #bpoorman #dpaste
Keypoints
- Socket Threat Research Team identified two malicious Go packages, github.com/bpoorman/uuid and github.com/bpoorman/uid, that typosquat trusted UUID libraries.
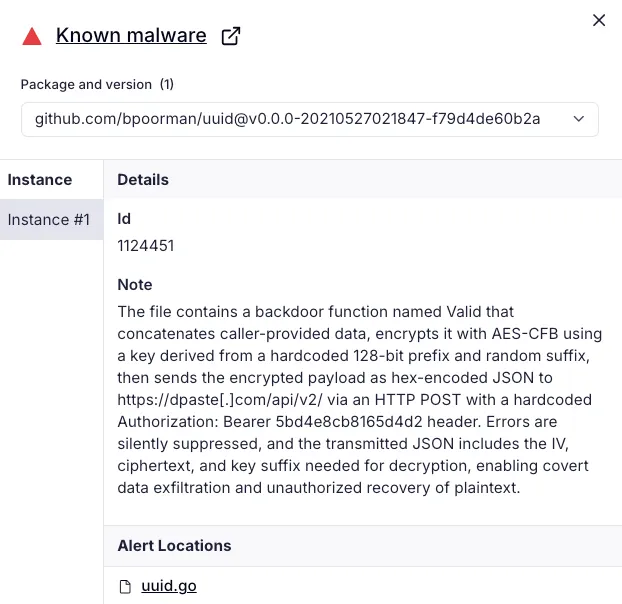
- The malicious packages preserve normal UUID API behavior but add a hidden Valid function that aggregates, encrypts, and exfiltrates data to dpaste.com using a hardcoded bearer token.
- github.com/bpoorman/uuid has been publicly available since May 2021 and remains accessible via the Go module mirror (proxy.golang.org); github.com/bpoorman/uid is cached on the mirror as well.
- The exfiltration routine uses AES CFB with a fixed key prefix (57a475a22da17139), random suffix bytes, hex-encoded payloads, and a short HTTP timeout to fail quietly on errors.
- The malicious behavior triggers only when application code calls Valid, making any caller-supplied sensitive data (IDs, tokens, keys) a potential leak point, including CI/build pipelines.
- Socket reported the packages to the Go security team and recommends treating new dependencies as untrusted, scanning for typosquats, and enforcing CI/build controls and dependency allowlists.
MITRE Techniques
- [T1195.002 ] Supply Chain Compromise – Typosquatted and published malicious libraries to the Go ecosystem to introduce a backdoor and exfiltration primitive. (‘two related malicious Go packages, github[.]com/bpoorman/uuid and github[.]com/bpoorman/uid, that typosquat trusted UUID libraries’)
- [T1204.005 ] User Execution: Malicious Library – The backdoor executes only when developers call the misleading Valid helper, relying on developer usage rather than automatic triggers. (‘The malicious behavior triggers only when application code explicitly calls Valid, a name that plays on the legitimate Validate helper’)
- [T1036 ] Masquerading – The actor closely imitates legitimate packages and maintainer names (pborman → bpoorman) to appear authentic and avoid detection. (‘typosquats the maintainer name (pborman versus bpoorman) while keeping the /uuid suffix’)
- [T1656 ] Impersonation – The package imitates long-standing, widely used UUID implementations to blend in with normal dependencies. (‘imitates the long-standing github.com/google/uuid and github.com/pborman/uuid packages’)
- [T1567.003 ] Exfiltration Over Web Service: Exfiltration to Text Storage Sites – Stolen, encrypted data is uploaded to a public paste service using its API and a hardcoded bearer token. (‘encrypts and uploads caller-supplied data using a hardcoded dpaste API token’)
- [T1027.013 ] Obfuscated Files or Information: Encrypted/Encoded File – The routine hex-encodes ciphertext and JSON payloads before transmission to conceal exfiltrated content. (‘stringct := hex.EncodeToString(ct) // Hex ciphertext (IV + data)’ )
Indicators of Compromise
- [Domain ] Exfiltration endpoint – dpaste.com (https://dpaste.com/api/v2/) used as the collection endpoint for encrypted payloads.
- [GitHub package ] Malicious Go packages – github[.]com/bpoorman/uuid, github[.]com/bpoorman/uid (typosquat packages implementing the exfiltration Valid function).
- [GitHub account ] Publisher repository – github[.]com/bpoorman (repository uid with uid.go containing the exfiltration code).
- [API token / Header ] Hardcoded bearer token for dpaste API – Authorization: Bearer 5bd4e8cb8165d4d2.
- [Crypto key material ] AES key prefix – 57a475a22da17139 (fixed key prefix used to derive the AES key).
- [Module version / VCS reference ] Cached module identifier – v0.0.0-20210528062104-e068190dd06b (github.com/bpoorman/uid available via proxy.golang.org).
Read more: https://socket.dev/blog/malicious-go-packages-impersonate-googles-uuid-library-and-exfiltrate-data