Calisto (aka ColdRiver/Star Blizzard), an intrusion set attributed to Russia’s FSB, resumed spear-phishing campaigns in May–June 2025 targeting NGOs, researchers, and institutions supporting Ukraine using impersonation, compromised redirectors and an AiTM phishing kit that can relay 2FA. The group used ProtonMail-themed decoys, PHP redirectors on compromised sites, and a homemade JavaScript-based kit hosted on domains such as simleasip[.]org to capture credentials. #Calisto #ReportersWithoutBorders
Keypoints
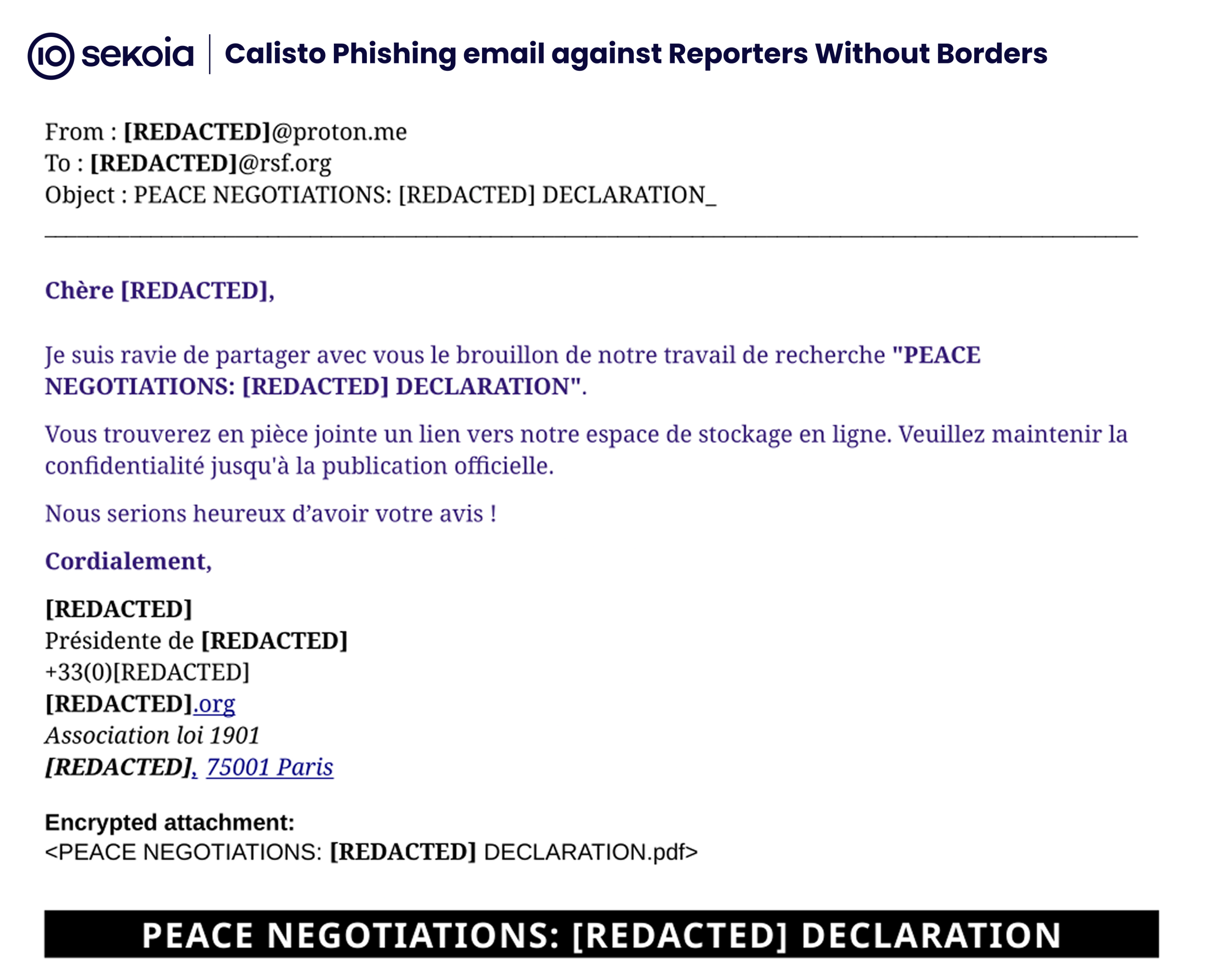
- Calisto targeted NGOs (including Reporters Without Borders), researchers and organisations supporting Ukraine with spear-phishing in May–June 2025.
- Attackers impersonated trusted contacts and used a “missing attachment” or dysfunctional PDF tactic to elicit follow-up requests from victims.
- Follow-up messages redirected victims via compromised websites to ProtonDrive-themed phishing pages that presented malicious or deceptive PDF decoys.
- Researchers detonated a phishing kit (hosted on account.simpleasip[.]org) that injects malicious JavaScript to force cursor focus, pre-fill usernames, and interact with an attacker-controlled API to relay MFA/CAPTCHA (AiTM).
- Redirectors were implemented as PHP scripts on compromised sites, likely deployed using credentials leaked by information stealers; domains were registered via Namecheap and Regway.
- Investigators observed successful credential capture accompanied by an IP (196.44.117[.]196) accessing a decoy account and associated with the Big Mama Proxy service.
- TDR tracked Calisto activity since 2022 and noted continued use of credential harvesting, ClickFix for code execution, and targeting aligned with Russian strategic interests.
MITRE Techniques
- [T1566 ] Phishing – Calisto used spear-phishing emails that impersonate trusted contacts and omit attachments to prompt replies: ‘the phishing email came from a ProtonMail address made to look like a trusted contact. It asked the recipient to review a document, but no document was attached.’
- [T1204.002 ] User Execution: Malicious Link – victims were redirected from emails to compromised sites and then to a ProtonDrive URL or phishing page: ‘the Calisto operator responded with another email … containing a link to a previously compromised website… The site acted as a redirector to a ProtonDrive URL that likely presented a malicious PDF to the user.’
- [T1059.007 ] Command and Scripting Interpreter: JavaScript – the phishing kit injects JavaScript into the sign-in page to force focus and interact with authentication flows: ‘malicious JavaScript is injected to keep the user’s cursor focused on the password field…’
- [T1556 ] Modify Authentication Process – the kit relays two-factor authentication using an Adversary-in-the-Middle technique to capture credentials and MFA: ‘The kit can relay two-factor authentication and seems to employ an Adversary-in-the-Middle (AiTM) technique…’
- [T1078 ] Valid Accounts – PHP redirectors were deployed on compromised websites likely breached using leaked credentials from information stealers: ‘This redirector is a PHP script deployed on compromised websites, likely breached through credentials leaked by information stealers.’
- [T1583.001 ] Acquire Infrastructure: Domain Registration – infrastructure was obtained via domain registrations and free DNS services (Namecheap/Regway), enabling the phishing and redirector domains: ‘Most of the domain names used by Calisto rely on free authoritative servers from Namecheap… the domains used during Q1 and Q2 were initially registered through Regway.’
Indicators of Compromise
- [URL ] PHP redirector endpoints on compromised sites – hxxps://admin.artemood[.]com/vendor/plugx/*.php, hxxps://mittalcpa[.]com/wp-content/plugins/bungs/*.php, and 5 more redirector URLs.
- [Domain ] phishing and infrastructure domains used by Calisto – simleasip[.]org, proton-decrypt[.]com, and 90+ other domains from the campaign (non-exhaustive list).
- [IP Address ] actor or proxy access observed – 196.44.117[.]196 accessed the decoy account (associated with Big Mama Proxy service).
- [Host ] phishing kit host and API domains – account.simpleasip[.]org (phishing kit host), scorelikelygateway.simleasip[.]org (attacker-controlled API).
- [File Name ] malicious/modified JavaScript bundle on phishing page – public-index.7162a3fd.js (patched Webpack bundle differing from ProtonMail’s asset).
- [File Name ] deceptive attachment – a ZIP archive renamed with a .pdf extension used to masquerade as a PDF decoy.
Read more: https://blog.sekoia.io/ngo-reporters-without-borders-targeted-by-calisto-in-recent-campaign/