ESET reports that MuddyWater (TA450) conducted a focused cyberespionage campaign primarily against organizations in Israel and one confirmed target in Egypt using new custom tools including the Fooder loader and the MuddyViper backdoor to improve evasion and persistence. The campaign also deployed credential stealers (CE-Notes, LP-Notes), browser stealers (Blub), go‑socks5 reverse tunnels, and adopted the CNG API for encryption to exfiltrate credentials and browser data. #MuddyWater #MuddyViper
Keypoints
- MuddyWater targeted primarily Israeli organizations (multiple sectors) and one organization in Egypt between Sept 30, 2024 and Mar 18, 2025.
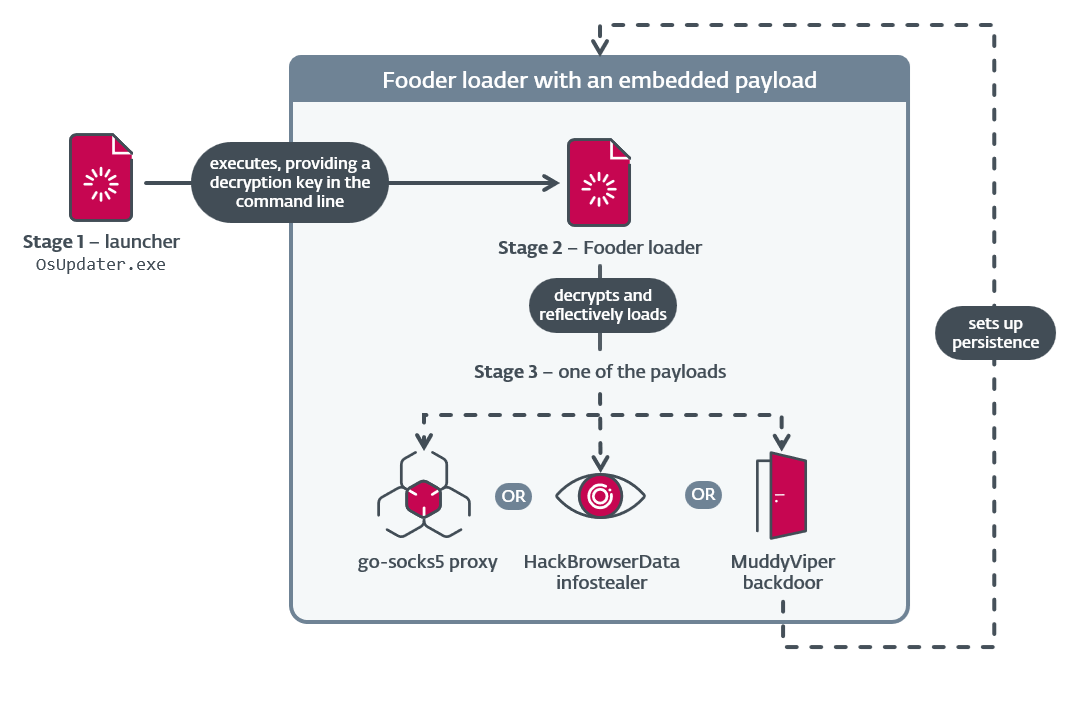
- Researchers documented previously unknown custom tooling: the Fooder loader (masquerading as Snake) and the MuddyViper C/C++ backdoor, deployed reflectively in memory.
- MuddyViper provides extensive capabilities (system info, file transfer, reverse shell, browser and Windows credential theft) and can persist via a scheduled task ManageOnDriveUpdater or Startup folder.
- Operators used evasion techniques including game-inspired delay loops and frequent Sleep API calls, dynamic API resolution, and use of the CNG API for AES-CBC encryption to hinder analysis and secure C2 traffic.
- The campaign also used CE-Notes and LP-Notes credential/browser stealers, Blub browser stealer, HackBrowserData, and customized go‑socks5 reverse tunnels for proxying and exfiltration.
- MuddyWater conducted overlap/cooperation with Lyceum (OilRig subgroup), likely acting as an initial access broker by delivering RMM installers and harvested credentials to other Iran-aligned operators.
MITRE Techniques
- [T1591 ] Gather Victim Org Information – MuddyWater gathers victim org info to use in spearphishing emails. (‘MuddyWater gathers victim org info to use in spearphishing emails.’)
- [T1583 ] Acquire Infrastructure – MuddyWater uses acquired infrastructure to host malware download locations and C&C servers. (‘MuddyWater uses acquired infrastructure to host malware download locations and C&C servers.’)
- [T1608 ] Stage Capabilities – MuddyWater stages tools like RMM tools and data stealers on file-hosting sites such as OneHub and Mega Limited. (‘MuddyWater stages tools like RMM tools and data stealers on file-hosting sites such as OneHub and Mega Limited.’)
- [T1587.001 ] Develop Capabilities: Malware – MuddyWater develops backdoors like MuddyViper and tools such as the Fooder loader, LP-Notes credential stealer, and the Blub and CE-Notes browser-data stealers. (‘MuddyWater develops backdoors like MuddyViper and tools such as the Fooder loader, LP-Notes credential stealer, and the Blub and CE-Notes browser-data stealers.’)
- [T1588.002 ] Obtain Capabilities: Tool – MuddyWater uses publicly available tools from GitHub, such as HackBrowserData and Go-based reverse proxies. (‘MuddyWater uses publicly available tools from GitHub, such as HackBrowserData and Go-based reverse proxies.’)
- [T1566.002 ] Phishing: Spearphishing Link – MuddyWater uses spearphishing emails with links to file hosting sites like OneHub and Mega Limited to host RMM software (Atera, Level, and PDQ). (‘MuddyWater uses spearphishing emails with links to file hosting sites like OneHub and Mega Limited to host RMM software (Atera, Level, and PDQ).’)
- [T1059.001 ] Command-Line Interface: PowerShell – MuddyViper has the capability to open and execute PowerShell scripts. (‘MuddyViper has the capability to open and execute PowerShell scripts.’)
- [T1059.003 ] Command-Line Interface: Windows Command Shell – MuddyViper has the capability to offer the Windows Command shell as a reverse shell. (‘MuddyViper has the capability to offer the Windows Command shell as a reverse shell.’)
- [T1559.001 ] Inter-Process Communication: Component Object Model – MuddyViper uses the ITaskService COM object to create a scheduled task for persistence. (‘MuddyViper uses the ITaskService COM object to create a scheduled task for persistence.’)
- [T1106 ] Native API – MuddyViper uses the CreateProcess API to execute additional files and commands. (‘MuddyViper uses the CreateProcess API to execute additional files and commands.’)
- [T1204.001 ] User Execution: Malicious Link – MuddyWater operators rely on targets clicking malicious links delivered through spearphishing. (‘MuddyWater operators rely on targets clicking malicious links delivered through spearphishing.’)
- [T1547.001 ] Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder – MuddyViper has the capability to copy itself to the victim’s Startup folder. (‘MuddyViper has the capability to copy itself to the victim’s Startup folder.’)
- [T1543.003 ] Create or Modify System Process: Windows Service – MuddyWater operators attempt to install RMM tools in %PROGRAMFILES%, which also includes creating a Windows service set to autostart. (‘MuddyWater operators attempt to install RMM tools in %PROGRAMFILES%, which also includes creating a Windows service set to autostart.’)
- [T1053 ] Scheduled Task/Job – MuddyViper can be persisted as a scheduled task named ManageOnDriveUpdater. (‘MuddyViper can be persisted as a scheduled task named ManageOnDriveUpdater.’)
- [T1134.001 ] Access Token Manipulation: Token Impersonation/Theft – The LP-Notes and CE-Notes tools attempt to impersonate a logged-on user’s security context via ImpersonateLoggedOnUser. (‘The LP-Notes and CE-Notes tools attempt to impersonate a logged-on user’s security context via ImpersonateLoggedOnUser.’)
- [T1140 ] Deobfuscate/Decode Files or Information – Blub uses string obfuscation for storing stolen data.Fooder can extract embedded, AES-encrypted payloads.CE-Notes and LP-Notes both use a custom byte-wise decryption routine to decrypt strings. (‘Blub uses string obfuscation for storing stolen data.Fooder can extract embedded, AES-encrypted payloads.CE-Notes and LP-Notes both use a custom byte-wise decryption routine to decrypt strings.’)
- [T1620 ] Reflective Code Loading – The Fooder loader performs reflective code loading to run additional tools (MuddyViper, reverse tunnels, and HackingBrowserData). (‘The Fooder loader performs reflective code loading to run additional tools (MuddyViper, reverse tunnels, and HackingBrowserData).’)
- [T1497.003 ] Virtualization/Sandbox Evasion: Time Based Evasion – MuddyViper uses many calls to a sleep function to detect and avoid virtualization and analysis environments, and generally to inhibit dynamic analysis. (‘MuddyViper uses many calls to a sleep function to detect and avoid virtualization and analysis environments, and generally to inhibit dynamic analysis.’)
- [T1027.007 ] Obfuscated Files or Information: Dynamic API Resolution – CE-Notes and LP-Notes perform dynamic API resolution by decrypting strings at runtime. (‘CE-Notes and LP-Notes perform dynamic API resolution by decrypting strings at runtime.’)
- [T1134.002 ] Access Token Manipulation: Create Process with Token – Fooder’s launcher attempts to duplicate the token of a process specified by the operator when launching Fooder via CreateProcessAsUserA. (‘Fooder’s launcher attempts to duplicate the token of a process specified by the operator when launching Fooder via CreateProcessAsUserA.’)
- [T1622 ] Debugger Evasion – MuddyViper searches for specific debugging tools, adjusting its behavior accordingly. (‘MuddyViper searches for specific debugging tools, adjusting its behavior accordingly.’)
- [T1070.009 ] Indicator Removal: Clear Persistence – MuddyViper can modify registry keys used for persistence, if instructed to uninstall itself. (‘MuddyViper can modify registry keys used for persistence, if instructed to uninstall itself.’)
- [T1070.004 ] Indicator Removal: File Deletion – MuddyViper can delete itself from the system, if instructed to uninstall itself. (‘MuddyViper can delete itself from the system, if instructed to uninstall itself.’)
- [T1036 ] Masquerading – Some versions of Fooder masquerade as an innocuous Snake game. (‘Some versions of Fooder masquerade as an innocuous Snake game.’)
- [T1036.004 ] Masquerading: Masquerade Task or Service – MuddyViper can create a task named ManageOnDriveUpdater. (‘MuddyViper can create a task named ManageOnDriveUpdater.’)
- [T1112 ] Modify Registry – MuddyViper can modify the HKCUSoftwareMicrosoftWindowsCurrentVersionExplorerUser Shell FoldersStartup and HKCUSoftwareMicrosoftWindowsCurrentVersionExplorerShell FoldersStartup registry keys, to change the location of the Startup folder. (‘MuddyViper can modify the HKCUSoftwareMicrosoftWindowsCurrentVersionExplorerUser Shell FoldersStartup and HKCUSoftwareMicrosoftWindowsCurrentVersionExplorerShell FoldersStartup registry keys, to change the location of the Startup folder.’)
- [T1027.009 ] Obfuscated Files or Information: Embedded Payloads – Fooder can extract an embedded, AES-encrypted payload. (‘Fooder can extract an embedded, AES-encrypted payload.’)
- [T1027.013 ] Obfuscated Files or Information: Encrypted/Encoded File – Fooder can extract an embedded, AES-encrypted payload. (‘Fooder can extract an embedded, AES-encrypted payload.’)
- [T1555.003 ] Credentials from Password Stores: Credentials from Web Browsers – CE-Notes and Blub attempt to steal credentials stored in browsers. (‘CE-Notes and Blub attempt to steal credentials stored in browsers.’)
- [T1056.002 ] Input Capture: GUI Input Capture – MuddyViper and LP-Notes have the ability to display a Windows security login prompt to capture login credentials and confirm the credentials’ veracity by relaying those credentials to legitimate Windows APIs. (‘MuddyViper and LP-Notes have the ability to display a Windows security login prompt to capture login credentials and confirm the credentials’ veracity by relaying those credentials to legitimate Windows APIs.’)
- [T1082 ] System Information Discovery – MuddyViper collects system information from compromised systems and reports it back to the C&C server. (‘MuddyViper collects system information from compromised systems and reports it back to the C&C server.’)
- [T1518.001 ] Software Discovery: Security Software Discovery – MuddyViper attempts to get a process list of running applications, looks for security-related processes and, if found, reports them to the C&C server and modifies its behavior. (‘MuddyViper attempts to get a process list of running applications, looks for security-related processes and, if found, reports them to the C&C server and modifies its behavior.’)
- [T1074.001 ] Data Staged: Local Data Staging – Blub, CE-Notes, and LP-Notes stage stolen credentials on disk for MuddyViper, reverse tunnels, or RMM tools to collect and exfiltrate. (‘Blub, CE-Notes, and LP-Notes stage stolen credentials on disk for MuddyViper, reverse tunnels, or RMM tools to collect and exfiltrate.’)
- [T1560.001 ] Archive Collected Data: Archive via Utility – MuddyViper uses PowerShell’s Compress-Archive command to compress browser data collected via the HackBrowserData utility. (‘MuddyViper uses PowerShell’s Compress-Archive command to compress browser data collected via the HackBrowserData utility.’)
- [T1573.001 ] Encrypted Channel: Symmetric Cryptography – MuddyViper uses AES-CBC encryption to encrypt data before exchanging data with the C&C server. (‘MuddyViper uses AES-CBC encryption to encrypt data before exchanging data with the C&C server.’)
- [T1219 ] Remote Access Software – MuddyWater use Atera, Level, and PDQ RMM tools for remote access to victims’ systems. (‘MuddyWater use Atera, Level, and PDQ RMM tools for remote access to victims’ systems.’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – MuddyViper uses HTTPS for C&C communications. The reverse tunnels use a mixture of HTTP and HTTPS for C&C communications. (‘MuddyViper uses HTTPS for C&C communications. The reverse tunnels use a mixture of HTTP and HTTPS for C&C communications.’)
- [T1105 ] Ingress Tool Transfer – MuddyViper has the capability to download additional payloads from its C&C server. (‘MuddyViper has the capability to download additional payloads from its C&C server.’)
- [T1001 ] Data Obfuscation – MuddyViper leverages HTTPS for C&C communications, using the Status header to hide a backdoor command ID in the server-to-client direction of the communication. (‘MuddyViper leverages HTTPS for C&C communications, using the Status header to hide a backdoor command ID in the server-to-client direction of the communication.’)
- [T1090 ] Proxy – MuddyWater uses customized versions of go‑socks5 reverse proxy tools. (‘MuddyWater uses customized versions of go‑socks5 reverse proxy tools.’)
- [T1041 ] Exfiltration Over C2 Channel – MuddyWater tools exfiltrate data to C&C servers using C&C channels (HTTP and HTTPS). (‘MuddyWater tools exfiltrate data to C&C servers using C&C channels (HTTP and HTTPS).’)
- [T1030 ] Data Transfer Size Limits – MuddyViper supports downloading/uploading files in chunks of limited size. (‘MuddyViper supports downloading/uploading files in chunks of limited size.’)
Indicators of Compromise
- [File hash ] Fooder/MuddyViper and other tool binaries – 76632910CF67697BF5D7285FAE38BFCF438EC082 (OsUpdater.exe launcher), 25361183DE63F296BA71B6FCF0725E022B3C989A (0bff183a39ruQsY.dll), and many other hashes listed in the report.
- [Filename ] Documented malicious filenames and staged data – OsUpdater.exe (Fooder launcher), ce-notes.txt / lp-notes.txt (staged stolen data).
- [IP address ] C2 and staging servers – 35.175.224[.]64 (observed MuddyWater C&C server), 206.71.149[.]51 (staging server used to host payloads).
- [Domain ] C2 and hosting domains – processplanet[.]org (staging and C&C server), magicallyday[.]com (observed MuddyWater C&C server).
Read more: https://www.welivesecurity.com/en/eset-research/muddywater-snakes-riverbank/