A sudden collapse in Salty2FA infrastructure in late October 2025 coincided with samples that contained indicators, code, and delivery fallbacks from both Salty2FA and Tycoon2FA, producing single payloads that executed stages from each kit. This hybridization complicates attribution and detection, and suggests defenders should treat Salty2FA and Tycoon2FA as a linked threat cluster and update hunting and detection logic accordingly. #Salty2FA #Tycoon2FA
Keypoints
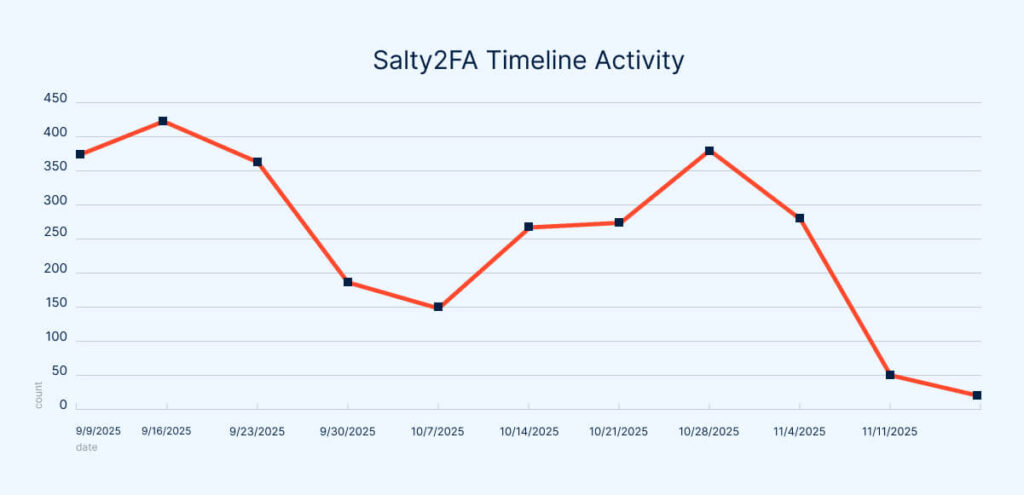
- Salty2FA submissions to ANY.RUN dropped sharply in early November 2025, falling from ~250+ weekly to only 51 submissions by November 11, 2025.
- Analysts observed samples and sessions containing overlapping indicators and detection rule triggers for both Salty2FA and Tycoon2FA within the same analysis sessions.
- Code-level analysis showed hybrid payloads: initial stages matched Salty2FA patterns while later stages reproduced Tycoon2FA’s execution chain almost line-for-line.
- Salty2FA infrastructure showed DNS/hosting failures (SERVFAIL), causing scripts to switch to hardcoded fallback URLs that delivered Tycoon-like payload stages.
- The overlap supports earlier hypotheses linking Storm-1747 to Tycoon2FA and possibly to Salty2FA, increasing the likelihood of shared operator activity or collaboration.
- Defenders should prioritize behavioral detections (DOM manipulation, multi-stage execution logic, DGA/fast-flux patterns) and update IR playbooks and hunting hypotheses to account for mixed execution chains and fallback payloads.
- ANY.RUN’s interactive sandboxing and TI feeds help rapidly surface mixed execution chains, fresh IOCs, and historical context to validate attribution and tune detections.
MITRE Techniques
- [T1566 ] Phishing – Phishing pages hosted on abused developer hosting were used to collect credentials and redirect victims to multi-stage payloads (‘mimic Microsoft’s official authentication page’).
- [T1059.007 ] JavaScript – Malicious JavaScript performed multi-stage execution, including Base64 decoding and eval() to load additional payload stages (‘Base64 decoding followed by an eval() call’).
- [T1027 ] Obfuscated Files or Information – Payload stages were obfuscated using Base64 and Base64-XOR techniques to hide execution logic (‘obfuscated using a Base64-XOR technique’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – Stolen data and payload stages were sent and retrieved via HTTP POST/GET to web hosts, including requests to DGA- and fast-flux-style domains (‘POST request to a server using a characteristic DGA-generated domain name’).
- [T1483 ] Domain Generation Algorithms – The campaign used DGA-generated domains and fast-flux hosting patterns tied to Tycoon2FA’s infrastructure (‘DGA-generated domains tied to the kit’s fast-flux infrastructure’).
- [T1497.001 ] Virtualization/Sandbox Evasion – The JavaScript contained anti-analysis checks, blocking DevTools shortcuts and timing checks to detect debugging or sandboxed execution (‘blocking keyboard shortcuts that open DevTools and performing execution-timing checks designed to detect debugging attempts’).
Indicators of Compromise
- [Domain ] delivery and payload hosting – omvexe[.]shop, 1otyu7944x8[.]workers[.]dev, and 5 more related domains observed in the analyses.
- [URL ] hardcoded fallback URLs in JavaScript – hxxps[://]omvexe[.]shop//, hxxps[://]4inptv[.]1otyu7944x8[.]workers[.]dev/ (used as secondary payload hosts when primary domains failed).
- [Hosting endpoints ] abused developer hosting platforms – diogeneqc[.]pages[.]dev, lapointelegal-portail[.]pages[.]dev (Cloudflare Pages / Workers used to host phishing pages and payload stages).
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/salty2fa-tycoon2fa-hybrid-phishing-2025/