ByteToBreach is a financially motivated data‑leak trader and access broker active since mid‑2025 who sells corporate datasets and access from banks, telecoms, IT providers, and other large enterprises across multiple countries. On November 14, 2025 the actor claimed a breach of Eurofiber’s GLPI service‑management platform, exfiltrating roughly 10,000 password hashes and configuration/ticket data using rented VPS infrastructure to run time‑based SQL extraction. #ByteToBreach #Eurofiber
Keypoints
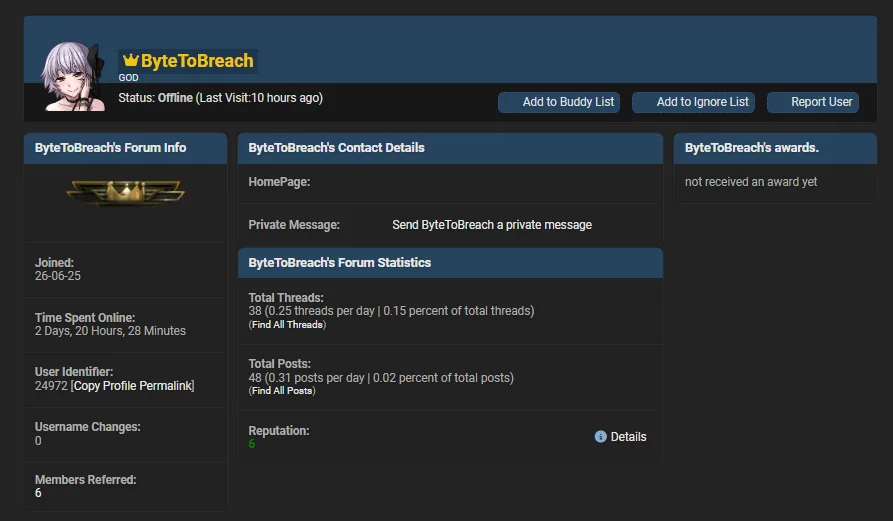
- ByteToBreach is an individual or small group acting as an access broker and data seller, using a consistent handle across forums and a public WordPress site for victim shaming and promotion.
- At least 35 victims are attributed, heavily targeting financial services (13 victims), telecoms (7 victims), and IT/technology service providers, with geographic spread across the US, India, Europe, CIS states, and more.
- The actor exploited internet‑facing systems and known software vulnerabilities (e.g., GLPI SQL injection, Oracle WebLogic) as well as stolen credentials and phishing to gain initial access.
- Concrete cases include a claimed Oracle WebLogic exploit at Seychelles Commercial Bank (2.2 GB exfiltrated) and a GLPI compromise at Eurofiber yielding ~10,000 password hashes and downstream customer credentials.
- Operations involve parallelized data extraction using rented VPS servers (about 20) across European countries, then monetizing breaches via Dark Web markets, forum sales threads, and a branded leak site.
- Recommended defenses include attack surface reduction, rapid patching of public‑facing software, MFA and credential hygiene, database/backups hardening, exfiltration detection, and supplier security controls.
MITRE Techniques
- [T1583.003 ] Virtual Private Server – Actor rents many VPS instances across European countries to parallelize long-running SQL injection and data extraction; (‘approximately 20 rented VPS servers in several European countries to parallelize requests and retrieve roughly 10,000 password hashes and related secrets over a period of about ten days’).
- [T1583.006 ] Web Services – Operates a public WordPress site that functions as a leak and victim‑shaming platform branded “Pentesting Ltd”; (‘Operates a WordPress site branded as “Pentesting Ltd” that acts as a leak and victim shaming site, hosting logos, samples, and contact details.’).
- [T1190 ] Exploit Public-Facing Application – Uses SQL injection and other exploits against internet‑facing applications like GLPI to gain initial access; (‘Describes the use of SQL injection and other exploits against internet-facing apps like GLPI and similar enterprise platforms to gain first access.’).
- [T1059 ] Command and Scripting Interpreter – Postings advertise reverse shell access into compromised enterprises, implying use of shell commands after exploitation; (‘Advertises “reverse shell access” into large enterprises, which implies use of shell commands after exploitation, based on wording in sale posts.’).
- [T1213 ] Data from Information Repositories – Exfiltrates and sells complete databases from ITSM platforms, LMS systems, and financial data stores once inside victims; (‘Sells complete databases from ITSM platforms, LMS systems, and financial or corporate data stores, showing focus on structured repositories once inside.’).
Indicators of Compromise
- [Victim Organizations ] listed breached or advertised victims – Eurofiber, Seychelles Commercial Bank, and 33 more known victims.
- [Vulnerable Applications ] exploited public-facing software – GLPI (service management platform), Oracle WebLogic (exploited at Seychelles Commercial Bank).
- [Credentials / Hashes ] stolen authentication material – roughly 10,000 password hashes (Eurofiber) and reused credentials from infostealer logs.
- [Data Volumes / Datasets ] exfiltrated datasets used for sale or extortion – 2.2 GB of banking and government data (Seychelles Commercial Bank), ticket/configuration databases and KYC files.
- [Leak Sites & Listings ] actor-controlled promotion channels – WordPress leak site “Pentesting Ltd” (public victim shaming page), DarkForums sale threads and forum profile listings.
- [Infrastructure Used ] rented hosting resources to conduct extraction – approximately 20 VPS servers across several European countries used to parallelize SQL extraction.
Read more: https://socradar.io/dark-web-profile-bytetobreach/