SEQRITE APT-Team identified “Operation Hanoi Thief,” a spear‑phishing campaign using fake resumes and a pseudo‑polyglot document to deliver a multi‑stage infection chain targeting Vietnamese IT and recruitment professionals. The campaign abuses trusted Windows binaries (ftp.exe, DeviceCredentialDeployment.exe, ctfmon.exe) to decode and sideload a DLL implant named LOTUSHARVEST that steals browser credentials and exfiltrates them to attacker-controlled endpoints. #LOTUSHARVEST #OperationHanoiThief
Keypoints
- Campaign named “Operation Hanoi Thief” targets IT and recruitment/HR professionals in Vietnam using fake resume lures.
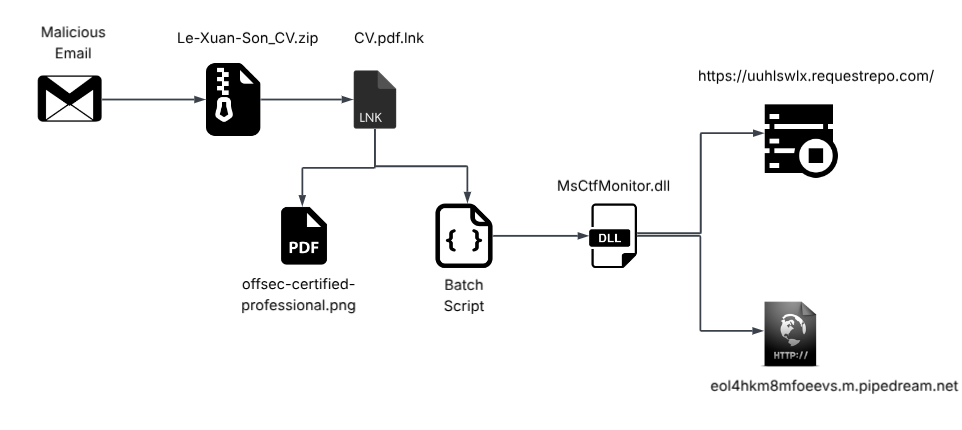
- Initial delivery is a spear‑phishing ZIP (Le-Xuan-Son_CV.zip) containing an LNK shortcut and a pseudo‑polyglot pseudo-PDF that also hides a batch script.
- The LNK abuses ftp.exe (LOLBin) to invoke the pseudo‑polyglot, which contains a base64 payload that is decoded into a DLL (MsCtfMonitor.dll / LOTUSHARVEST).
- The installer leverages DLL sideloading by placing the DLL alongside a copied ctfmon.exe so Windows loads the malicious DLL instead of the legitimate one.
- LOTUSHARVEST performs anti‑analysis checks, harvests browser history and saved credentials (Chrome/Edge), decrypts passwords via CryptUnprotectData, and exfiltrates data over HTTPS to attacker domains.
- Infrastructure includes randomly generated subdomains (e.g., uuhlswlx.requestrepo.com and eol4hkm8mfoeevs.m.pipedream.net) used for C2/exfiltration; attribution is tentatively Chinese‑origin with medium confidence.
- IOCs include multiple SHA‑256 hashes for the ZIP, LNK, pseudo‑polyglot, and DLL; SEQRITE detects these as Trojan.50086.SL / Trojan.A18678918.
MITRE Techniques
- [T1566.001 ] Spearphishing Attachment – Delivered via a malicious spear‑phishing ZIP containing the lure and stagers (‘a malicious spear-phishing ZIP file named Le-Xuan-Son_CV.zip’)
- [T1587.001 ] Develop Payloads: Malware – Use of a crafted pseudo‑polyglot payload and staged DLL implant (‘a pseudo-polyglot payload to hide the malicious intentions’)
- [T1204.002 ] User Execution: Malicious File – Execution requires user interaction to open the LNK which triggers the second stage (‘the LNK file… executes the second stager’)
- [T1218 ] Signed Binary Proxy Execution – Abuses signed/trusted binaries (ftp.exe) to execute local commands and scripts (‘usage of ftp.exe to execute the pseudo-polyglot file, with a flag known as -s’)
- [T1036.007 ] Masquerading: misleading file extension – Files and names are disguised to appear legitimate (e.g., LNK named as PDF and PNG renamed to PDF) (‘renaming the file offsec-certified-professional.png to CV-Nguyen-Van-A.pdf’)
- [T1140 ] Deobfuscate/Decode Files or Information – Script extracts and decodes a base64 blob from the pseudo‑polyglot to reconstruct the DLL (‘searches for a base64 encoded data blob within the pseudo-polyglot file… decodes it’)
- [T1574.002 ] DLL Side-Loading – Places MsCtfMonitor.dll alongside a copied ctfmon.exe so the benign executable loads the malicious DLL (‘creates a DLL file named MsCtfMonitor.dll… making it a case of DLL sideloading’)
- [T1082 ] System Information Discovery – Collects host details by calling GetComputerNameA and GetUserNameA to tag exfiltrated data (‘attaches the computer name and username… from GetComputerNameA and GetUserNameA’)
- [T1012 ] File and Directory Discovery (for browser data) – Opens browser SQLite databases to locate history and login stores (‘opens the browsers’ SQLite History databases… and the Login Data database’)
- [T1555.003 ] Credentials from Password Stores – Reads stored login credentials and attempts to decrypt them using CryptUnprotectData (‘reads up to five stored login credentials… attempts to decrypt each password using the classic CryptUnprotectData API’)
- [T1005 ] Data from Local System – Collects browser history and saved credentials and formats results for exfiltration (‘extract the 20 most recently visited URLs… formats the results as a JSON array’)
- [T1041 ] Exfiltration Over C2 Channel – Sends stolen browser information as a JSON POST to the attacker endpoint (‘issues a POST request to the /service endpoint and sends the stolen browser information as a JSON payload’)
- [T1071.001 ] Application Layer Protocol: HTTPS – Uses HTTPS to communicate with attacker-controlled servers over port 443 (‘connects to the attacker-controlled server eol4hkm8mfoeevs.m.pipedream.net over port 443’)
Indicators of Compromise
- [File Hash ] Delivery and components – 1beb8fb1b6… (ZIP), 77373ee986… (LNK), and 2 more hashes
- [File Name ] Malicious files used in the campaign – Le-Xuan-Son_CV.zip, CV.pdf.lnk, and other files like offsec-certified-professional.png / MsCtfMonitor.dll
- [Domain ] C2 and exfiltration endpoints – eol4hkm8mfoeevs.m.pipedream.net, uuhlswlx.requestrepo.com
- [Phone Number ] Contact listed in fake resume – +84912345678 (used in the lure; likely not reliable)
- [Malware Name ] Final payload classification – LOTUSHARVEST (MsCtfMonitor.dll) and detections Trojan.50086.SL / Trojan.A18678918
Read more: https://www.seqrite.com/blog/9479-2/